Microsoft Windows Wlan Autoconfig Service Remote Code Execution

Microsoft Windows Wlan Autoconfig Service Remote Code Execution Windows wlan autoconfig service remote code execution vulnerability. probability of exploitation activity in the next 30 days epss score history. Apply the appropriate security or cumulative update to address the vulnerability. reboot the system if prompted. epss is a daily estimate of the probability of exploitation activity being observed over the next 30 days.
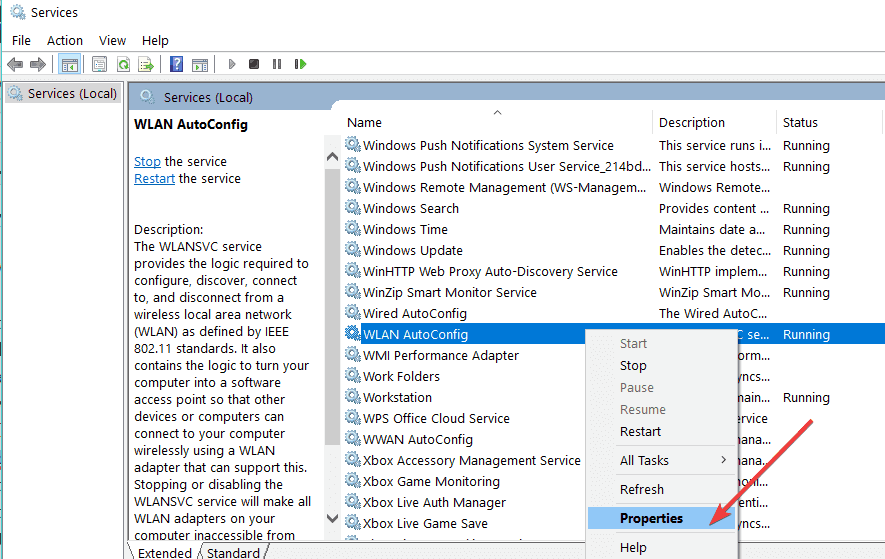
Fix Wlan Autoconfig Service Not Running Error 1067 In Windows 10 A vulnerability classified as critical was found in microsoft windows 10 10 1607 10 1809 10 1909 10 2004 10 20h2 server 2016 server 2019 server up to 2004 (operating system). this vulnerability affects an unknown functionality of the component wlan autoconfig service. applying a patch is able to eliminate this problem. First published: wed sep 15 2021 (updated:) windows wlan autoconfig service remote code execution vulnerability credit:secure@microsoft secure@microsoft. This vulnerability exists in the windows wlan autoconfig service, which manages wi fi network connections. if an attacker is within wireless range (think: next coffee shop, conference, public space), they can send specially crafted network packets to your device. Heap based buffer overflow in the wireless lan autoconfig service (aka wlansvc) in microsoft windows vista gold, sp1, and sp2 and server 2008 gold and sp2 allows remote attackers to execute arbitrary code via a malformed wireless frame, aka "wireless frame parsing remote code execution vulnerability.".
Résolu Windows N A Pas Pu Démarrer Le Service De Configuration This vulnerability exists in the windows wlan autoconfig service, which manages wi fi network connections. if an attacker is within wireless range (think: next coffee shop, conference, public space), they can send specially crafted network packets to your device. Heap based buffer overflow in the wireless lan autoconfig service (aka wlansvc) in microsoft windows vista gold, sp1, and sp2 and server 2008 gold and sp2 allows remote attackers to execute arbitrary code via a malformed wireless frame, aka "wireless frame parsing remote code execution vulnerability.". By selecting these links, you will be leaving nist webspace. we have provided these links to other web sites because they may have information that would be of interest to you. no inferences should be drawn on account of other sites being referenced, or not, from this page. More than 150 million people use github to discover, fork, and contribute to over 420 million projects. Learn about cve 2021 36965, a critical windows wlan autoconfig service remote code execution vulnerability published by microsoft. find out the impact, affected systems, and mitigation steps. Title: windows wlan autoconfig service remote code execution vulnerability. this container includes required additional information provided by the cve program for this vulnerability.

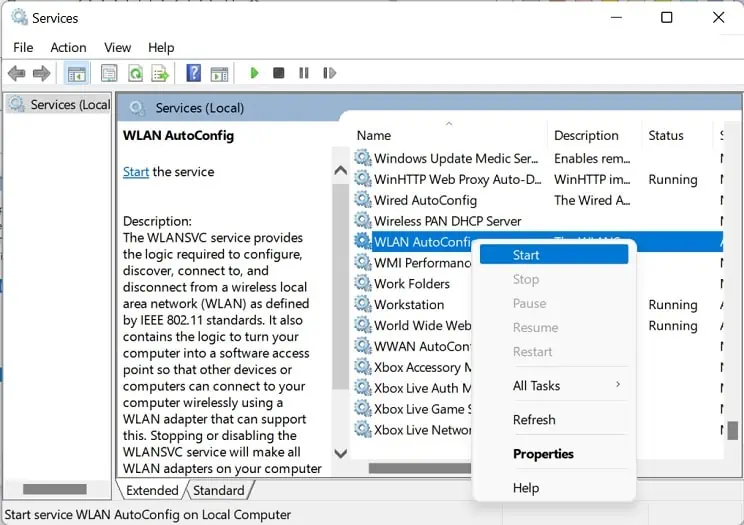
Start Wlan Autoconfig Wlansvc Service On Windows 10 Windows 11 By selecting these links, you will be leaving nist webspace. we have provided these links to other web sites because they may have information that would be of interest to you. no inferences should be drawn on account of other sites being referenced, or not, from this page. More than 150 million people use github to discover, fork, and contribute to over 420 million projects. Learn about cve 2021 36965, a critical windows wlan autoconfig service remote code execution vulnerability published by microsoft. find out the impact, affected systems, and mitigation steps. Title: windows wlan autoconfig service remote code execution vulnerability. this container includes required additional information provided by the cve program for this vulnerability.
Comments are closed.