Microsoft Purview Insider Risk Priority User Groups Policy Setup
Prioritize User Groups For Insider Risk Management Policies Microsoft Learn about the priority user groups settings for microsoft purview insider risk management. In this video, i walk through priority user groups in microsoft purview insider risk management and show how to set up insider risk policies that focus on high risk,.
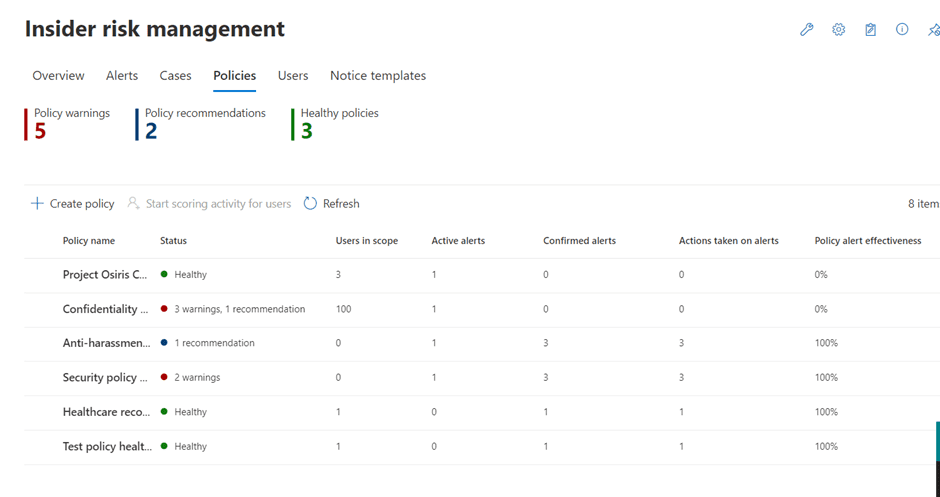
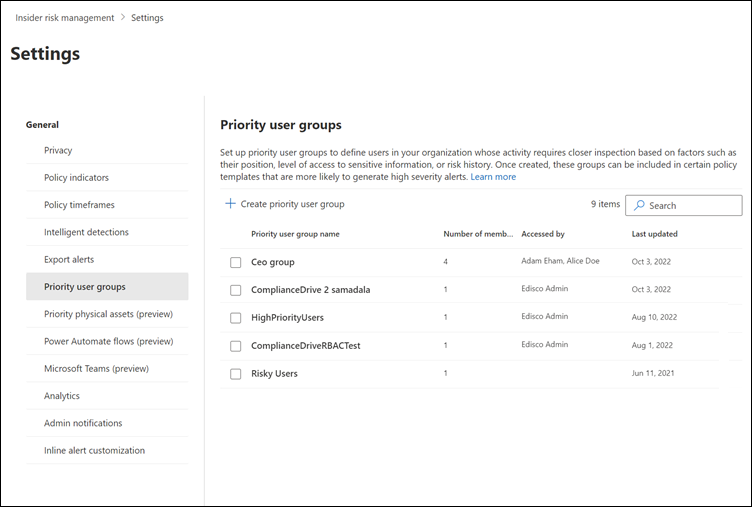
Reduce Data Theft With Microsoft Purview Insider Risk Management In this blog entry i am going to show you how to create a priority user group in irm. then i am going to demonstrate how to create an irm policy using priority users policy template. Creating a pugs a simple three step process: name the group and add a description, add members and finally choose which users can view data involving the users in the priority group. In this interactive guide, you’ll see how you can use policy templates to create policies that detect risky activities that may lead to potential data security incidents and help protect your organization’s data. To create a new insider risk management policy, generally use the policy workflow in the insider risk management solution in the microsoft purview portal. you can also create quick policies for general data leaks and data theft by departing users from analytics checks if applicable.
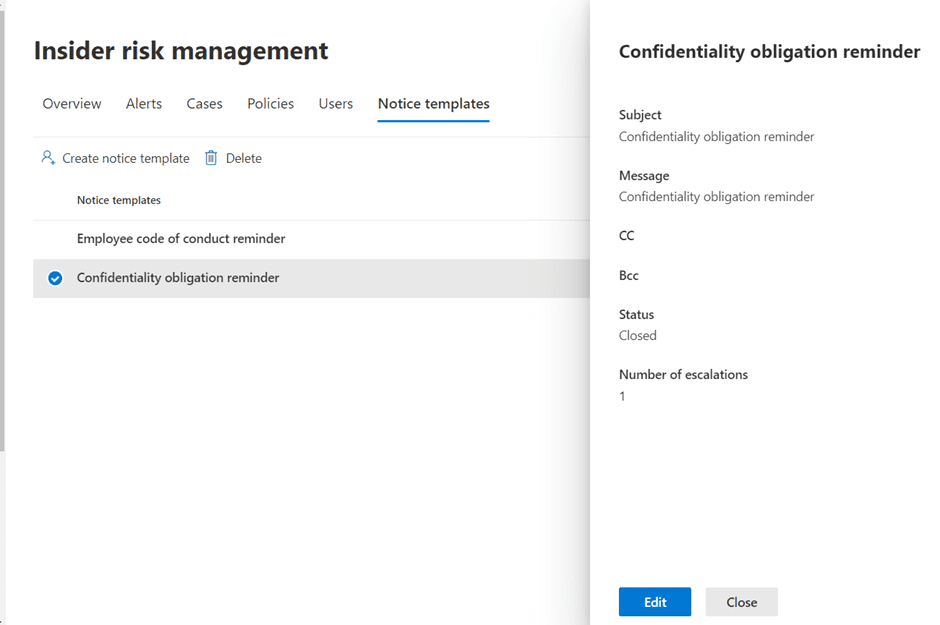
Reduce Data Theft With Microsoft Purview Insider Risk Management In this interactive guide, you’ll see how you can use policy templates to create policies that detect risky activities that may lead to potential data security incidents and help protect your organization’s data. To create a new insider risk management policy, generally use the policy workflow in the insider risk management solution in the microsoft purview portal. you can also create quick policies for general data leaks and data theft by departing users from analytics checks if applicable. Use the priority user groups setting to define the users in your organization that need closer inspection and more sensitive risk scoring. choose whether to display usernames or anonymized versions of usernames for all current and past policy matches for alerts and cases. was this page helpful?. Complete the following steps to set up prerequisites and configure an insider risk management policy. the insider risk management solution provides a tenant level option to help customers facilitate internal governance at the user level. Learn how to use ms purview irm (insider risk management) to create priority user groups and priority users policy to monitor risky users. Next we can use an adaptive scope or select users and groups to which we want to apply this policy. to makes things simple for this example, i’ve chosen to apply the policy to a user named ‘patti fernandez’ only.
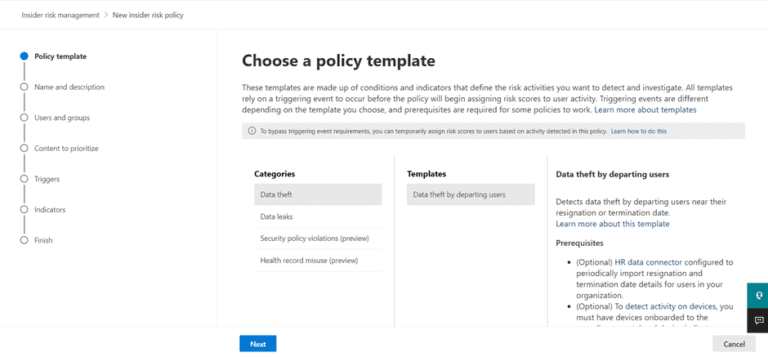
Reduce Data Theft With Microsoft Purview Insider Risk Management Use the priority user groups setting to define the users in your organization that need closer inspection and more sensitive risk scoring. choose whether to display usernames or anonymized versions of usernames for all current and past policy matches for alerts and cases. was this page helpful?. Complete the following steps to set up prerequisites and configure an insider risk management policy. the insider risk management solution provides a tenant level option to help customers facilitate internal governance at the user level. Learn how to use ms purview irm (insider risk management) to create priority user groups and priority users policy to monitor risky users. Next we can use an adaptive scope or select users and groups to which we want to apply this policy. to makes things simple for this example, i’ve chosen to apply the policy to a user named ‘patti fernandez’ only.
Comments are closed.