Microsoft Intune Tutorial Zero Trust Explained

Intune Zerotrust Cybersecurity Microsoft Intune For detailed deployment guidance including prerequisites, licensing requirements, cross team coordination, and implementation steps, see zero trust deployment approach with microsoft intune. For detailed deployment guidance including prerequisites, licensing requirements, cross team coordination, and implementation steps, see zero trust deployment approach with microsoft intune.
Never Trust Always Verify Tips For Zero Trust With Intune Microsoft Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Microsoft intune, a robust endpoint management tool, is a cornerstone for implementing the zero trust model effectively. let’s explore how intune can help organizations adopt zero trust to protect their digital ecosystems. Learn how to implement zero trust identity and device access policies using microsoft intune, including app protection, device compliance, and conditional access integration. In this blog, i explore how to build a device centric zero trust foundation by leveraging microsoft intune and defender for endpoint. learn the key capabilities and configuration settings, and understand how to deploy them effectively, to enhance your device security posture.
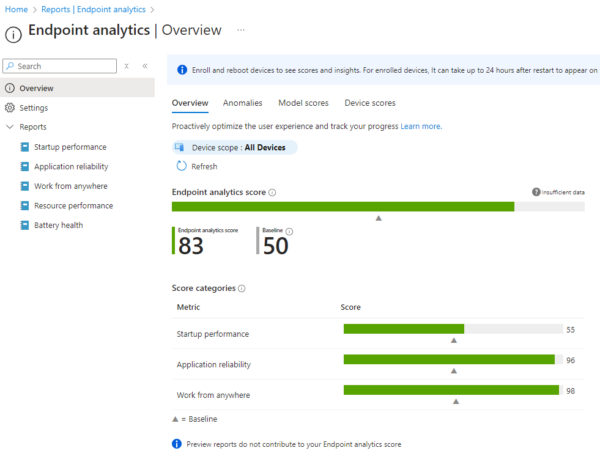
Achieving Zero Trust Security With Microsoft Intune Greystone Learn how to implement zero trust identity and device access policies using microsoft intune, including app protection, device compliance, and conditional access integration. In this blog, i explore how to build a device centric zero trust foundation by leveraging microsoft intune and defender for endpoint. learn the key capabilities and configuration settings, and understand how to deploy them effectively, to enhance your device security posture. You can use intune to protect access and data on organization owned and user's personal devices and have compliance and reporting features that support zero trust. From a zero trust perspective, device management with intune allows you to build conditional access policies around the concept of device trust where your organization can then enforce device compliance before allowing the device to connect to applications. Managing endpoints in the cloud is crucial for putting zero trust principles into practice and for enabling a secure, productive workspace. this session covers how microsoft intune brings zero trust to endpoint management by connecting device and app management, compliance, and threat protection. Zero trust is not a single product — it’s a security mindset. by leveraging microsoft entra id and intune, organizations can progressively implement zero trust controls across identity, devices, applications, and data — without disrupting productivity.
Comments are closed.