Microsoft 365 Admin User Phishing Threats

Microsoft 365 Phishing Attacks Growing In Sophistication Admins can learn about the anti phishing policies that are available in the built in security features for all cloud mailboxes and in microsoft defender for office 365. Learn how to stop phishing attacks in microsoft 365 with microsoft defender. this step by step guide helps you configure defender, set up anti phishing policies, and fine tune security settings to protect your inbox without the chaos.

Enhance Security Against Phishing Threats With Microsoft Defender S In a shocking turn of events, a new wave of phishing scams has emerged that specifically targets microsoft users. cybercriminals are now exploiting vulnerabilities in the microsoft 365 admin portal, allowing them to send deceptive emails that appear to come directly from official microsoft accounts. Conduct ongoing user trainings, including routine end user phishing tests. if you believe your office 365 environment is missing key security components or could be better configured, contact us today to discuss our office 365 management and support options. Protect users against phishing and other attacks in microsoft 365 for business in addition to the protections offered by microsoft 365 for business, there are other steps all users can take you help protect the organization. This article dives deep into the evolving phishing threat landscape, explores real world attack scenarios, and provides actionable strategies for securing microsoft 365 environments against phishing based threats.
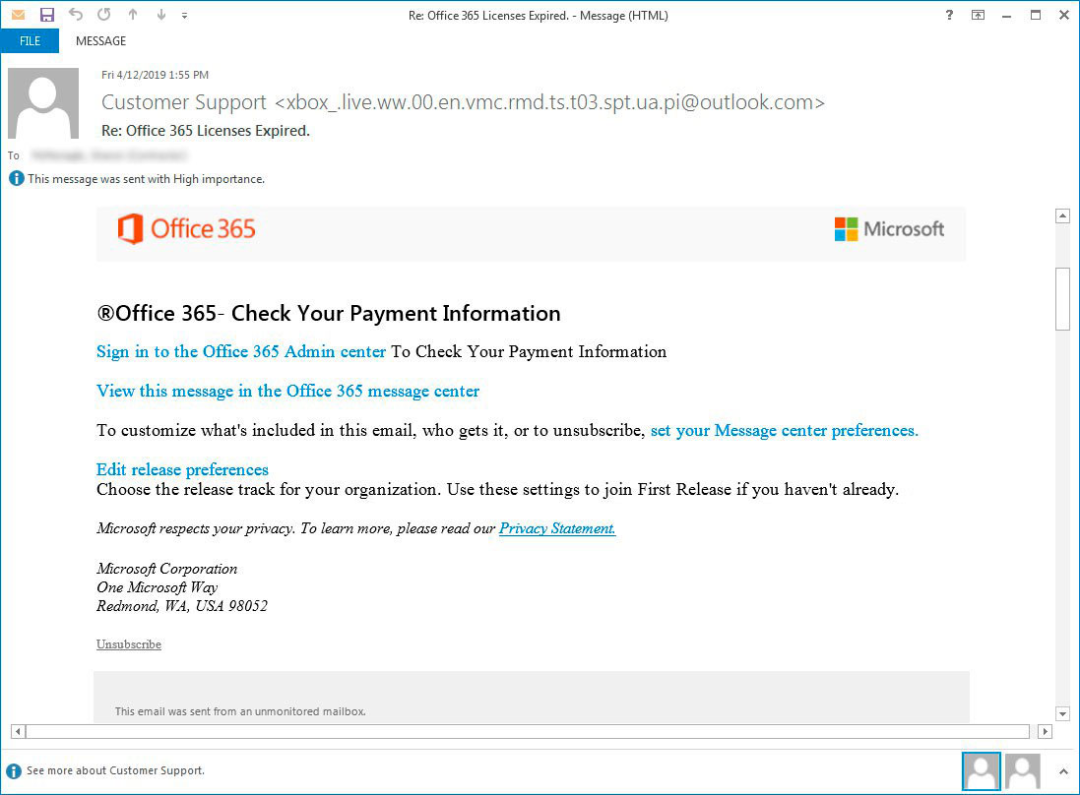
Office 365 Phishing Scam Targeting Admins Ccsi Protect users against phishing and other attacks in microsoft 365 for business in addition to the protections offered by microsoft 365 for business, there are other steps all users can take you help protect the organization. This article dives deep into the evolving phishing threat landscape, explores real world attack scenarios, and provides actionable strategies for securing microsoft 365 environments against phishing based threats. Credential phishing is just one of many attacks, including spear phishing, whaling, and malware phishing. that's why detecting phishing emails is crucial, and this guide will show you how to get phishing emails report in microsoft 365 effectively. Step by step guide to configure anti phishing policies in microsoft defender to protect users from spoofing, impersonation, and phishing attacks. Learn how a sophisticated microsoft 365 phishing campaign bypasses defenses and how to detect and prevent account takeovers. A complete step by step guide to microsoft 365 attack simulation training, covering setup, phishing payload selection, targeting, training assignments, reporting, and best practices to help organizations strengthen user awareness and reduce phishing risks.
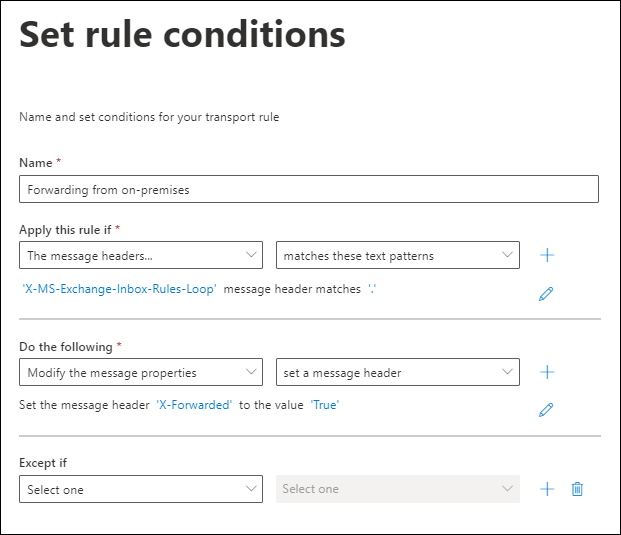
Microsoft 365 Phishing Threats Are Evolving Are Your Defenses Credential phishing is just one of many attacks, including spear phishing, whaling, and malware phishing. that's why detecting phishing emails is crucial, and this guide will show you how to get phishing emails report in microsoft 365 effectively. Step by step guide to configure anti phishing policies in microsoft defender to protect users from spoofing, impersonation, and phishing attacks. Learn how a sophisticated microsoft 365 phishing campaign bypasses defenses and how to detect and prevent account takeovers. A complete step by step guide to microsoft 365 attack simulation training, covering setup, phishing payload selection, targeting, training assignments, reporting, and best practices to help organizations strengthen user awareness and reduce phishing risks.

Microsoft 365 Phishing Threats Are Evolving Are Your Defenses Learn how a sophisticated microsoft 365 phishing campaign bypasses defenses and how to detect and prevent account takeovers. A complete step by step guide to microsoft 365 attack simulation training, covering setup, phishing payload selection, targeting, training assignments, reporting, and best practices to help organizations strengthen user awareness and reduce phishing risks.
Comments are closed.