Metasploit Framework With Basic Commands Hackingdna

Metasploit Framework With Basic Commands Technikal Gyaan Learn metasploit cheat sheet in the hackerdna security cheat sheets course. comprehensive cheat sheets for essential cybersecurity tools. quick reference commands, syntax, and examples for nmap, hydra, metasploit, burp suite, sqlmap, and more. Metasploit can be used to test the vulnerability of computer systems to protect them and metaspoit can be used to break into remote systems.
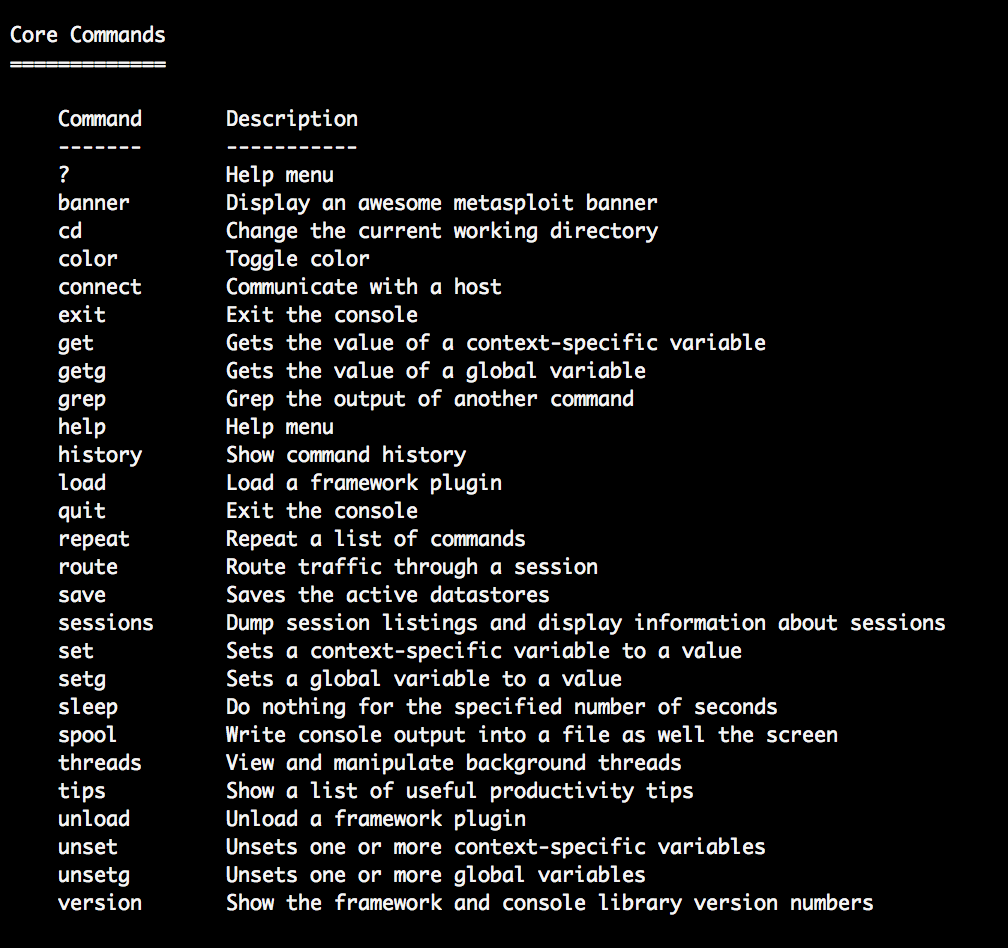
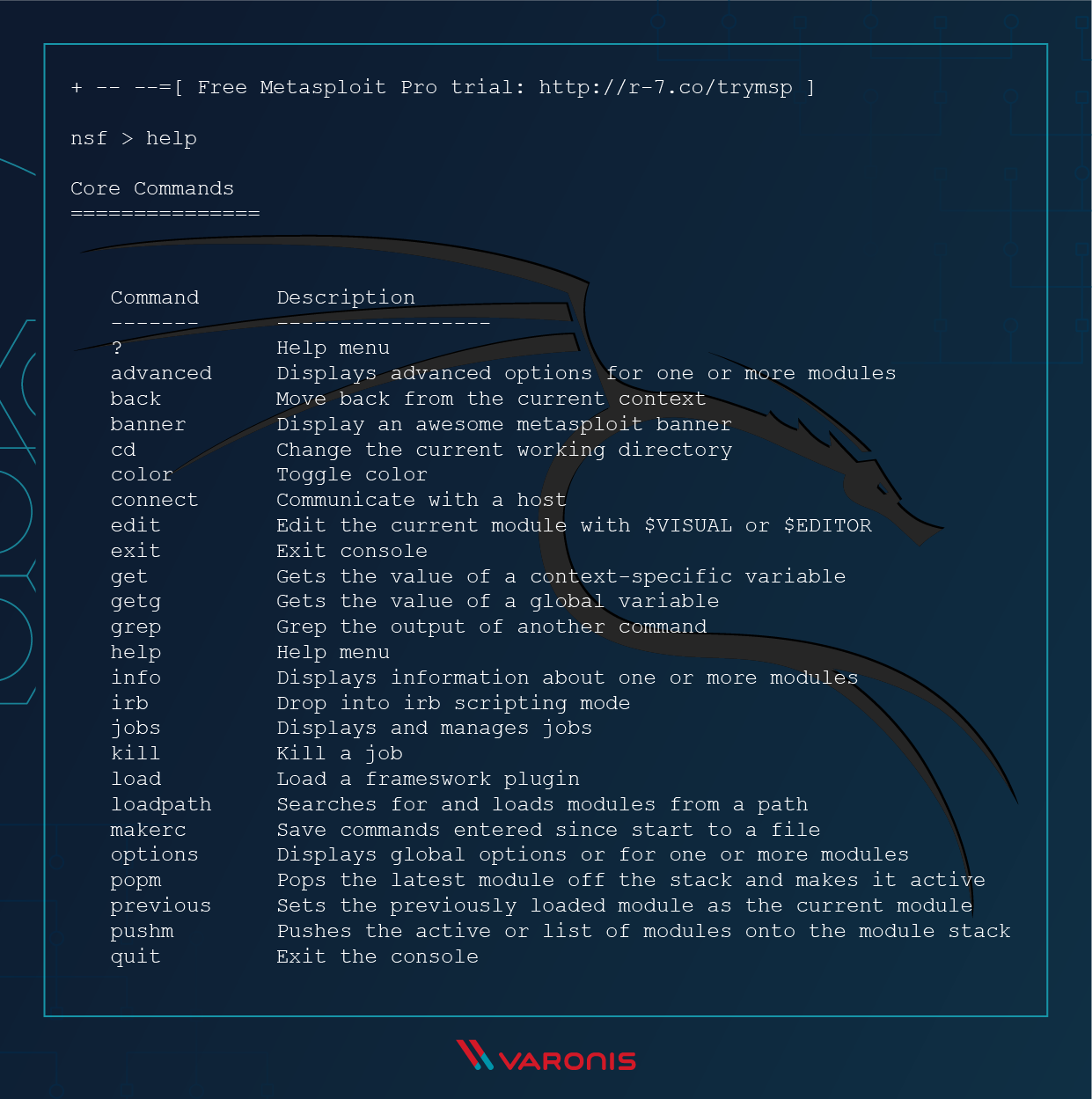
Introduction To Metasploit Rangeforce In this chapter, we will discuss some basic commands that are frequently used in metasploit. first of all, open the metasploit console in kali. you can do so by following the path: applications → exploitation tools → metasploit. We put together the metasploit cheat sheet. we include all the commands in an easy to download and reference format. downloadable jpeg, pdf or html tables. Execute cmd.exe with all available tokens and make it a hidden process: execute f
What Is Metasploit The Beginner S Guide Execute cmd.exe with all available tokens and make it a hidden process: execute f
Comments are closed.