Memu Tutorial Installing Frida Server For Android App Pentesting Ssl Piining Root Detection
Android Root Detection Bypass Using Frida 1 Pentest Limited Memu tutorial: installing frida server for android app pentesting ssl piining & root detection. In mobile application penetration testing, ssl pinning is one of the biggest challenges. most modern android apps use certificate pinning to block https interception tools like burp.

Android Root Detection Bypass Using Frida 3 Pentest Frida server (rooted devices): push and run a native daemon that lets you attach to any process. frida gadget (no root): bundle frida as a shared library inside the apk and auto load it within the target process. Installer script for frida and burp's certificate to help setup bypass ssl pinning in android applications. works with genymotion emulator. also works with android studio if the emulator is started with the writable system flag. eg: read the blog post for a detailed walkthrough > one click ssl pinning bypass setup. There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post. It is technically also possible to use frida without rooting your device, for example by repackaging the app to include frida gadget, or using a debugger to accomplish the same. but, for this introduction we’re going to focus on the simplest case: a rooted device.
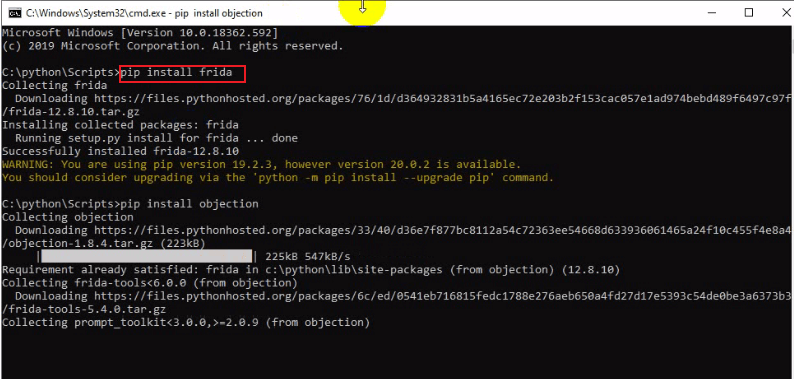
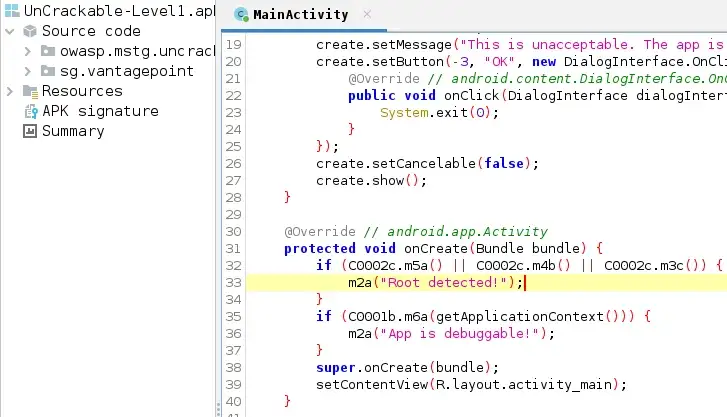
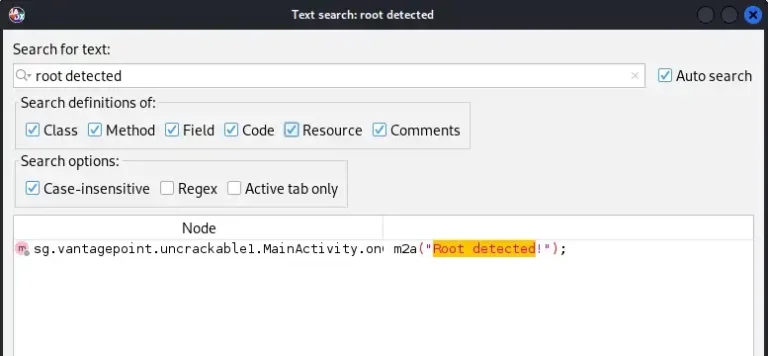
Android Root Detection Bypass Tutorial There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post. It is technically also possible to use frida without rooting your device, for example by repackaging the app to include frida gadget, or using a debugger to accomplish the same. but, for this introduction we’re going to focus on the simplest case: a rooted device. In this blog post, we will discuss how to set up frida on an emulator to perform dynamic instrumentation on android applications. to get started, you will need to set up an android emulator on your computer. you can use any emulator, such as the android studio emulator, genymotion, or bluestacks. Setup and installation: provides step by step instructions for enabling usb debugging and setting up the android development environment. frida server setup: guides through the process of downloading and configuring frida server on the device. Learn how to bypass ssl pinning on android apps using frida with step by step commands, real world techniques, and expert insights for penetration testers and security researchers. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications.
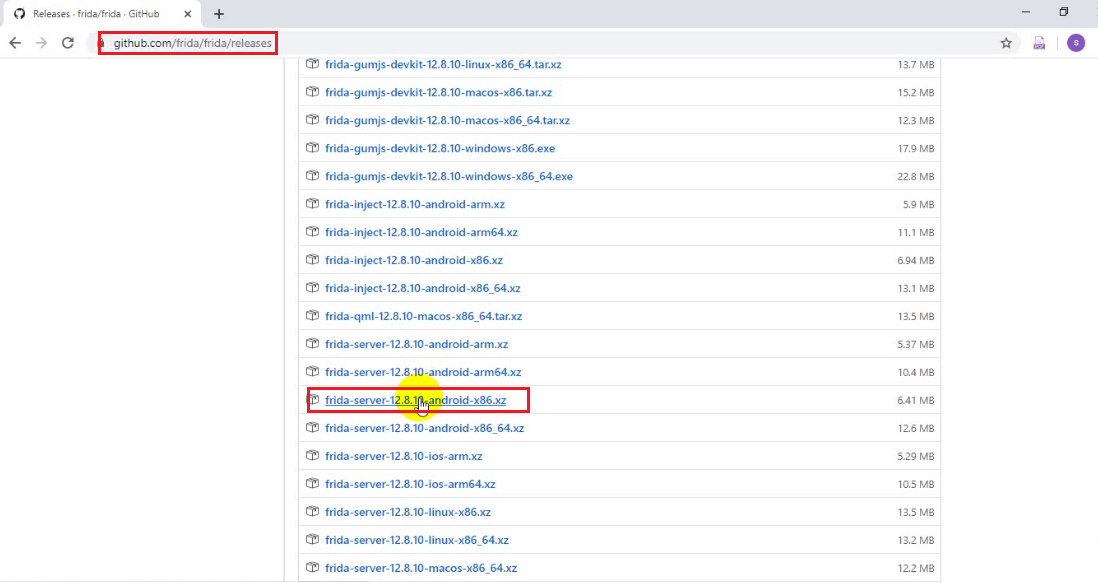
Android Root Detection Bypass Tutorial In this blog post, we will discuss how to set up frida on an emulator to perform dynamic instrumentation on android applications. to get started, you will need to set up an android emulator on your computer. you can use any emulator, such as the android studio emulator, genymotion, or bluestacks. Setup and installation: provides step by step instructions for enabling usb debugging and setting up the android development environment. frida server setup: guides through the process of downloading and configuring frida server on the device. Learn how to bypass ssl pinning on android apps using frida with step by step commands, real world techniques, and expert insights for penetration testers and security researchers. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications.
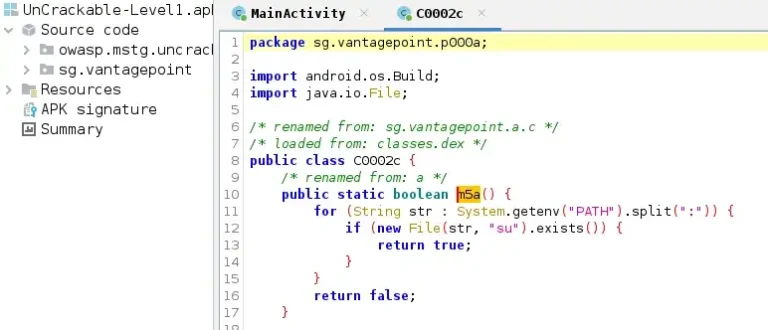
Android Root Detection Bypass Using Frida 1 Pentest Limited Learn how to bypass ssl pinning on android apps using frida with step by step commands, real world techniques, and expert insights for penetration testers and security researchers. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications.
Android Root Detection Bypass Using Frida 1 Pentest Limited
Comments are closed.