Media Risk Based Authentication
Media Risk Based Authentication Risk based authentication is an automated way for digital platforms to build in bob's father's sense of judgment. it automatically sorts out authentic actions from probable scams. When using these illustrations, you need to give appropriate credit based on the media type. the required attributions are stated below.
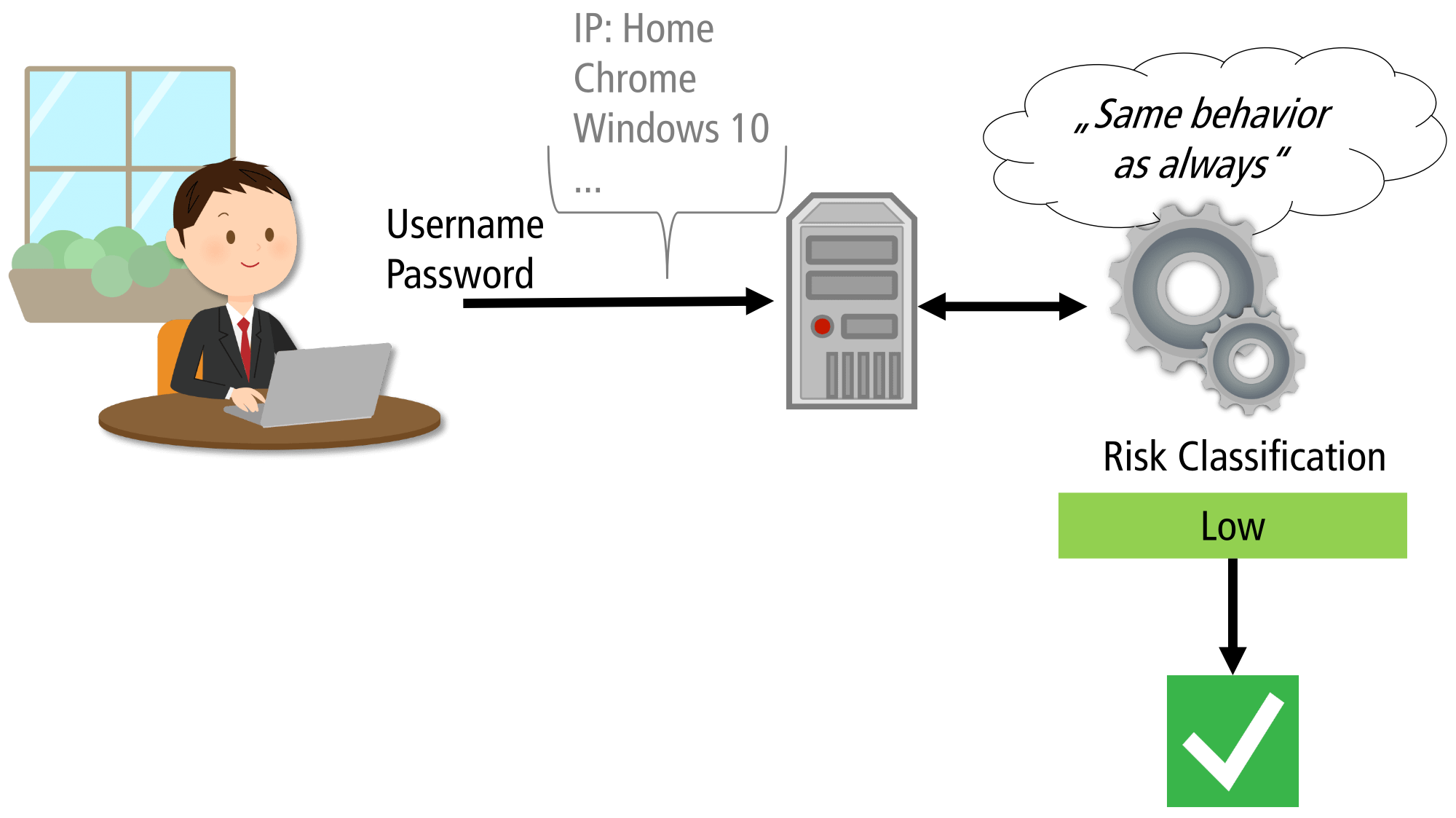
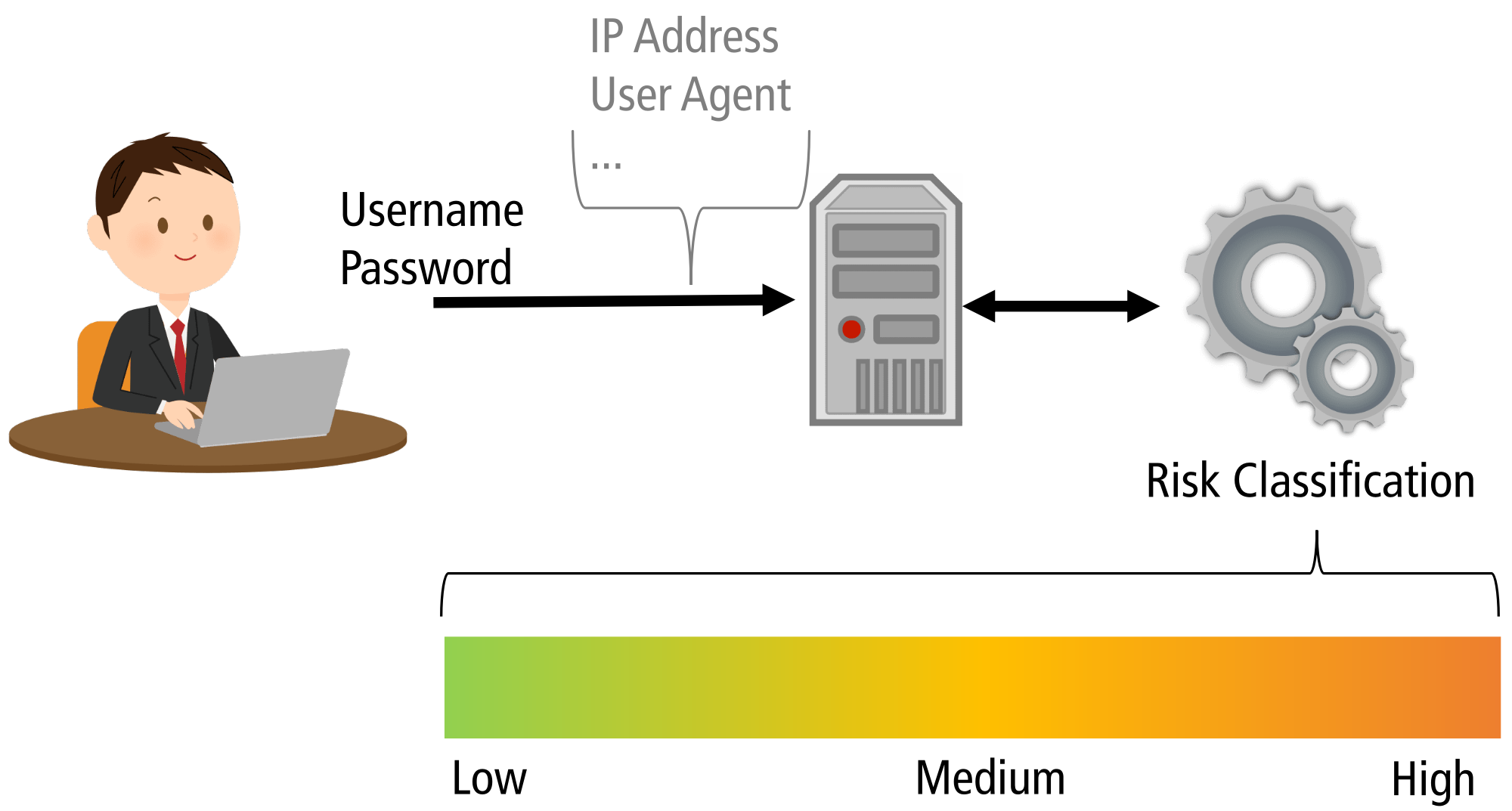
Media Risk Based Authentication In 2026, risk based authentication makes that balance possible because it evaluates contextual signals such as your location, device, ip address, and login timing before deciding how much verification you need, with this approach reflecting a broader shift in cybersecurity priorities. Risk based authentication provides a frictionless yet secure experience by analyzing user behavior, device reputation, network environment, and contextual data. this allows organizations to. This article covers the essential aspects of implementing risk based authentication (rba), focusing on adaptive authentication methods and risk assessment techniques. Learn risk based authentication strategies and best practices to strengthen identity security, reduce fraud, and improve user experience.
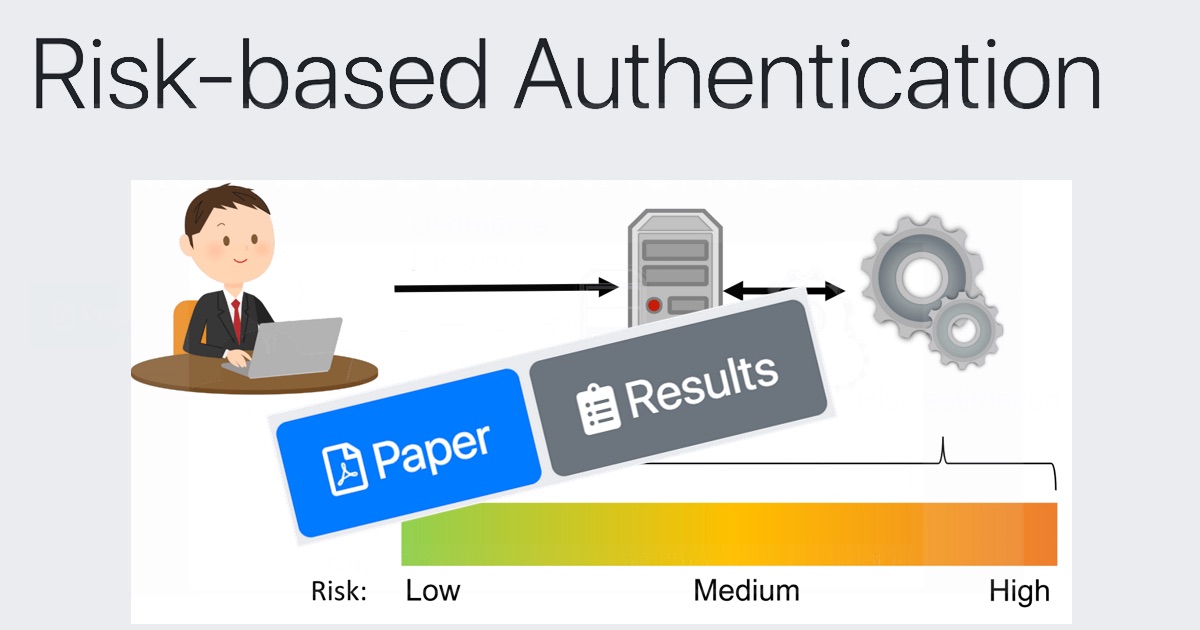
Risk Based Authentication Improves Password Security Without This article covers the essential aspects of implementing risk based authentication (rba), focusing on adaptive authentication methods and risk assessment techniques. Learn risk based authentication strategies and best practices to strengthen identity security, reduce fraud, and improve user experience. Risk based authentication represents a significant step forward in cybersecurity, offering a dynamic, intelligent approach to securing digital identities. by adapting authentication requirements based on real time risk assessment, rba enhances security while maintaining a seamless user experience. These guidelines focus on the authentication of subjects interacting with government systems over open networks, establishing that a given claimant is a subscriber who has been previously authenticated. This tutorial shows an administrator how to enable risk based multifactor authentication (mfa). if your it team hasn't enabled the ability to use microsoft entra multifactor authentication or you have problems during sign in, reach out to your helpdesk for additional assistance. In a risk based authentication system, the institution decides if additional authentication is necessary. if the risk is deemed appropriate, enhanced authentication will be triggered, such as a one time password delivered via an out of band communication.
Talk Risk Based Authentication Risk based authentication represents a significant step forward in cybersecurity, offering a dynamic, intelligent approach to securing digital identities. by adapting authentication requirements based on real time risk assessment, rba enhances security while maintaining a seamless user experience. These guidelines focus on the authentication of subjects interacting with government systems over open networks, establishing that a given claimant is a subscriber who has been previously authenticated. This tutorial shows an administrator how to enable risk based multifactor authentication (mfa). if your it team hasn't enabled the ability to use microsoft entra multifactor authentication or you have problems during sign in, reach out to your helpdesk for additional assistance. In a risk based authentication system, the institution decides if additional authentication is necessary. if the risk is deemed appropriate, enhanced authentication will be triggered, such as a one time password delivered via an out of band communication.
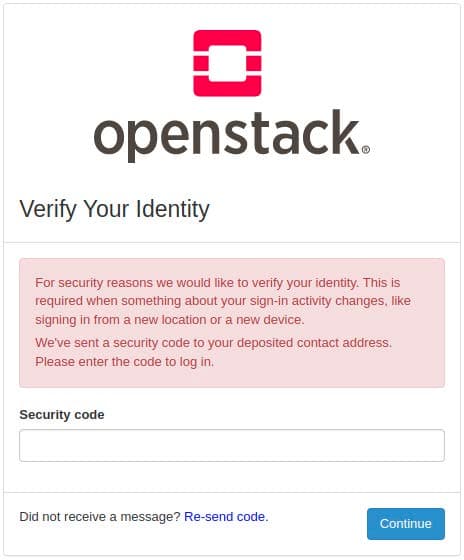
Open Source Risk Based Authentication This tutorial shows an administrator how to enable risk based multifactor authentication (mfa). if your it team hasn't enabled the ability to use microsoft entra multifactor authentication or you have problems during sign in, reach out to your helpdesk for additional assistance. In a risk based authentication system, the institution decides if additional authentication is necessary. if the risk is deemed appropriate, enhanced authentication will be triggered, such as a one time password delivered via an out of band communication.

Privacy Considerations For Risk Based Authentication Systems Risk
Comments are closed.