Md5 Algorithm What Is Md5 Algorithm Md5 Algorithm Explained Network Security Simplilearn

Ppt Md5 Algorithm What Is Md5 Algorithm Md5 Algorithm Explained In this article, you will understand what the md5 algorithm is, how it works step by step, why it is no longer considered secure, and where it may still be used in practice. Md5 is a cryptographic hash function algorithm that takes the message as input of any length and changes it into a fixed length message of 16 bytes. md5 algorithm stands for the message digest algorithm.
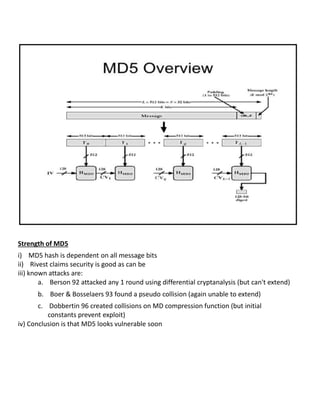
Ppt Md5 Algorithm What Is Md5 Algorithm Md5 Algorithm Explained Md5 is one in a series of message digest algorithms designed by professor ronald rivest of mit (rivest, 1992). when analytic work indicated that md5's predecessor md4 was likely to be insecure, rivest designed md5 in 1991 as a secure replacement. What is md5 algorithm? a cryptographic hash algorithm called md5 (message digest method 5) can be used to create a 128 bit digest from a string of arbitrary length. In this article, we discuss the underlying processes of the md5 algorithm and how the math behind the md5 hash function works. The message digest algorithm md5 is a cryptographic hash that is used to generate and verify digital signatures or message digests. md5 is still widely used despite being declared “cryptographically broken” over a decade ago.

Ppt Md5 Algorithm What Is Md5 Algorithm Md5 Algorithm Explained In this article, we discuss the underlying processes of the md5 algorithm and how the math behind the md5 hash function works. The message digest algorithm md5 is a cryptographic hash that is used to generate and verify digital signatures or message digests. md5 is still widely used despite being declared “cryptographically broken” over a decade ago. Learn what the md5 (message digest algorithm) hashing algorithm is, how it's used and why it has been deprecated in favor of more secure alternatives. Through this devops engineer course, you will develop technical expertise in deploying, managing, and monitoring cloud applications. Understanding md5: a step by step breakdown of the hashing process. md5 (message digest algorithm 5) is one of the most widely used cryptographic hash functions. it takes an input message and. Md5, or message digest algorithm 5, is a cryptographic algorithm that secures our data. learn how to use md5 hashes and how they work.

Md5 Algorithm Pdf Security Computer Security Learn what the md5 (message digest algorithm) hashing algorithm is, how it's used and why it has been deprecated in favor of more secure alternatives. Through this devops engineer course, you will develop technical expertise in deploying, managing, and monitoring cloud applications. Understanding md5: a step by step breakdown of the hashing process. md5 (message digest algorithm 5) is one of the most widely used cryptographic hash functions. it takes an input message and. Md5, or message digest algorithm 5, is a cryptographic algorithm that secures our data. learn how to use md5 hashes and how they work.
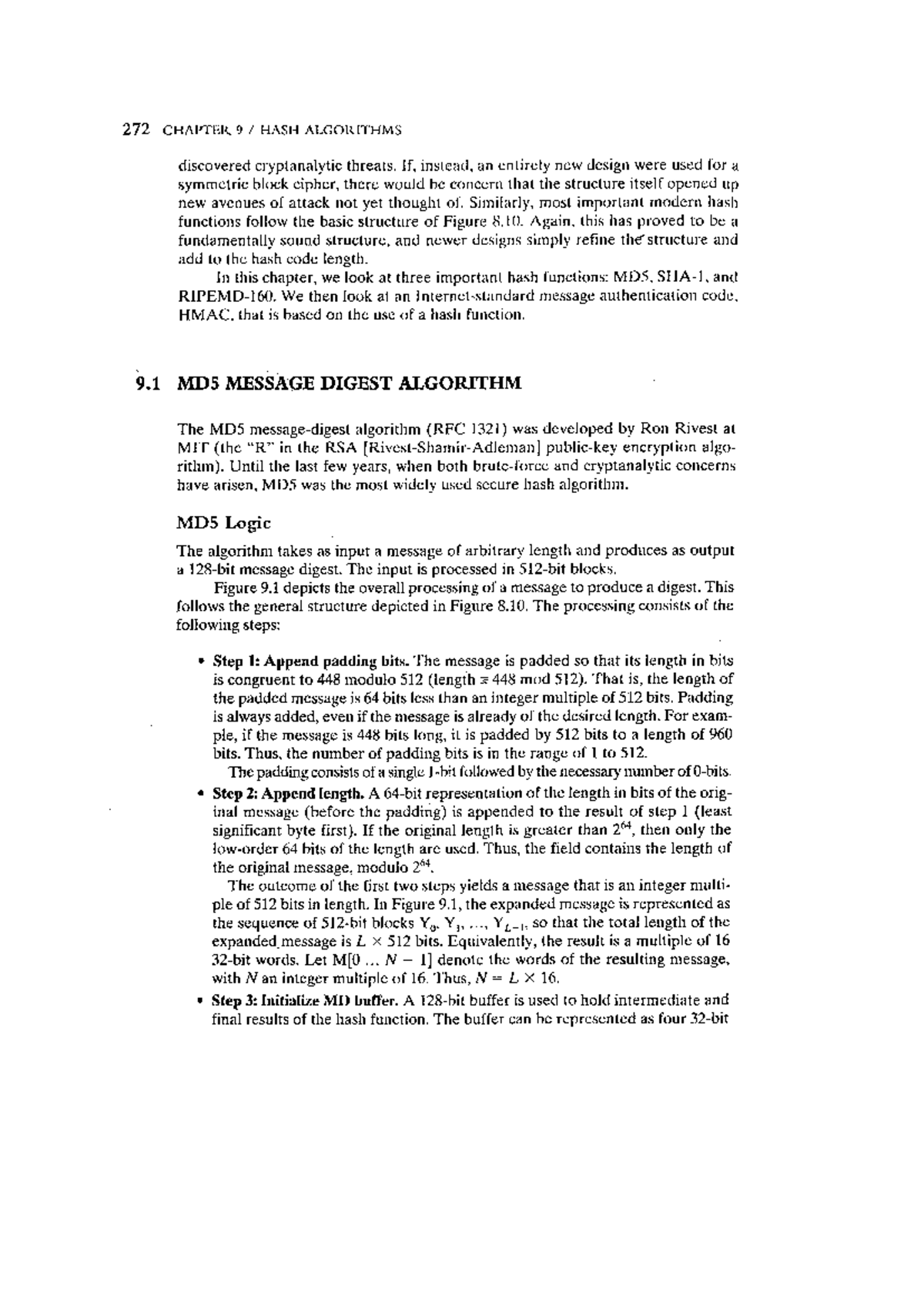
Md5 Algorithm Cryptography And Network Security Studocu Understanding md5: a step by step breakdown of the hashing process. md5 (message digest algorithm 5) is one of the most widely used cryptographic hash functions. it takes an input message and. Md5, or message digest algorithm 5, is a cryptographic algorithm that secures our data. learn how to use md5 hashes and how they work.
Network Security Md5 Pdf
Comments are closed.