Maths Pdf Cipher Cryptography

Cryptography Maths Pdf This article provides an overview of various cryptography algorithms, discussing their mathematical underpinnings and the areas of mathematics needed to understand them. Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme.

Cryptography Basics And Ciphers Pdf Cryptography Encryption This book provides an introduction to the theory of public key cryptography and to the mathematical ideas underlying that theory. public key cryptography draws on many areas of mathematics, including number theory, abstract algebra, probability, and information theory. Cryptology is the science of constructing and breaking codes. it consist of cryptography, the creation of codes and cryptanalysis, the theory of cracking codes. related in information theory is the construction of error correcting codes. Fortunately, the magical mathematics of cryptography can help. cryptography provides techniques for keeping information secret, for determining that information has not been tampered with, and for determining who authored pieces of information. Suppose we divide a and b by m, obtaining integer quotients and remainders, where the remainders are between 0 and m 1. that is, a = q1m r1 and. = q2m r2, where 0 r1 m 1 and 0 r2 m 1. then it is not di cult to see that a b (mod m) if and only if r1 = r2.
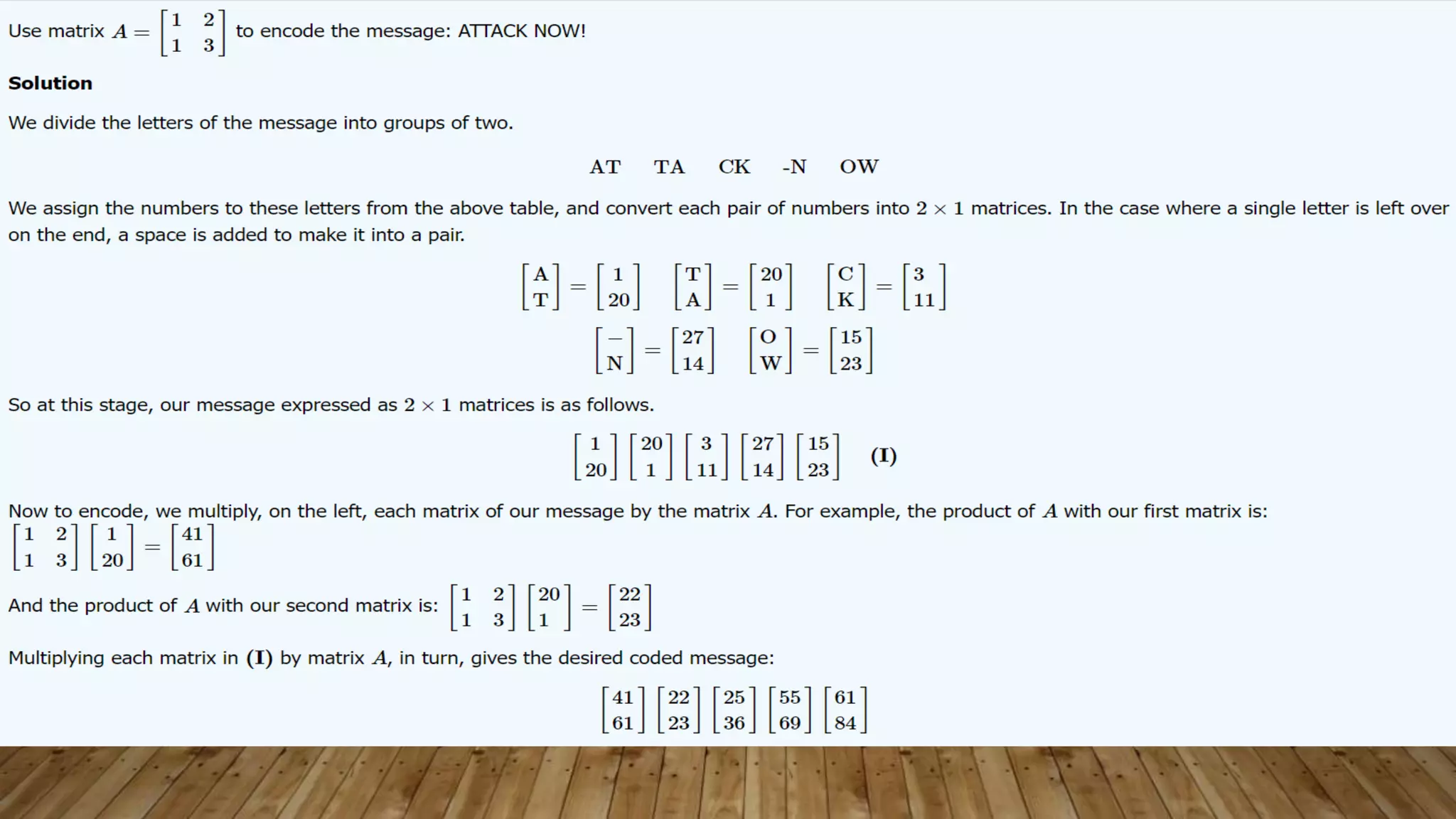
Maths In Cryptography Final Pptx Will inform our discussion of cryptography. i assume no prior acquaintance with ring or group theory, but as this is not a course in abstract algeb a, we will be selective in what we do cover. This document provides an analysis of encryption methods including ancient and modern cryptographic techniques. it begins by defining key cryptographic concepts and describing symmetric and asymmetric encryption. The foundational use of linear algebra in the hill cipher has paved the way for the development of more advanced block ciphers and continues to serve as an invaluable educational tool for understanding the mathematical principles underlying modern encryption techniques. Mit opencourseware is a web based publication of virtually all mit course content. ocw is open and available to the world and is a permanent mit activity.
Comments are closed.