Mastering Vulnerability Assessment

Mastering Vulnerability Assessment In 2024 Best Practices Join us to develop the practical, analytical, and strategic skills required to secure enterprise systems through effective vulnerability assessment and management practices. Cybersecurity is no longer just a matter of preventing breaches; it's about managing vulnerabilities efficiently and effectively. welcome to the master course: cybersecurity vulnerability management 2.0.

Mastering Vulnerability Assessment A vulnerability assessment is a structured process for identifying weaknesses in systems, applications, identities, and configurations, then translating them into decisions that reduce risk. In this article, we will explore the key methodologies, tools, and techniques used in vulnerability assessment, as well as provide guidance on implementing a vulnerability management program. In the world of cybersecurity, performing a vulnerability assessment is an important step in protecting your systems and data from potential threats. this detailed guide is here to help you understand what vulnerability assessment is and how it helps improve the overall security of an organization. As companies continue to expand their digital footprint, they inevitably become more vulnerable to cyber attacks. hence, it becomes essential to conduct vulnerability assessments regularly. in this blog post, we will cover everything you need to know about vulnerability assessments.
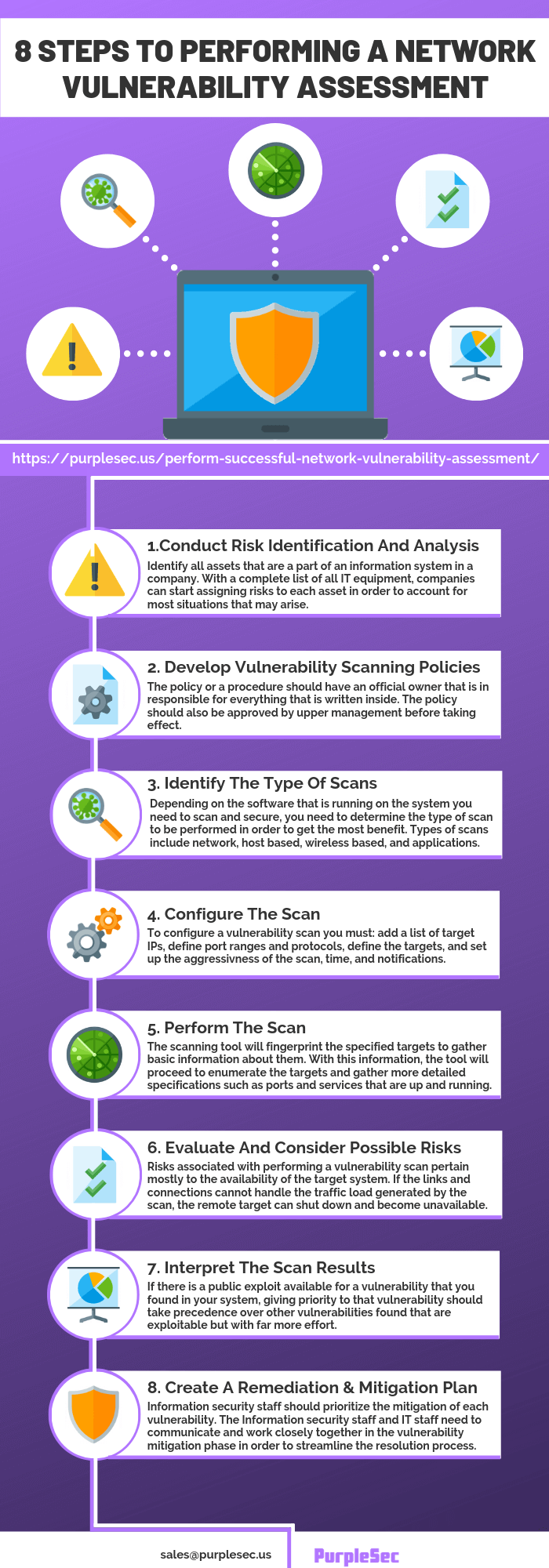
Vulnerability Assessment Vulnerability Assessment In the world of cybersecurity, performing a vulnerability assessment is an important step in protecting your systems and data from potential threats. this detailed guide is here to help you understand what vulnerability assessment is and how it helps improve the overall security of an organization. As companies continue to expand their digital footprint, they inevitably become more vulnerable to cyber attacks. hence, it becomes essential to conduct vulnerability assessments regularly. in this blog post, we will cover everything you need to know about vulnerability assessments. This detailed guide will walk you through the key concepts, methodologies, tools, and best practices that i’ve learned during my course on vulnerability assessment. Explore our guide on the vulnerability assessment process! learn step by step methods for identifying and mitigating vulnerabilities in your systems. 🔍🛡️. Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Mastering vulnerability assessment is a fundamental component of effective cybersecurity. by regularly identifying, analyzing, and mitigating vulnerabilities, organizations can significantly enhance their security posture.

Vulnerability Assessment Usafe Infosec Solutions Corp This detailed guide will walk you through the key concepts, methodologies, tools, and best practices that i’ve learned during my course on vulnerability assessment. Explore our guide on the vulnerability assessment process! learn step by step methods for identifying and mitigating vulnerabilities in your systems. 🔍🛡️. Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Mastering vulnerability assessment is a fundamental component of effective cybersecurity. by regularly identifying, analyzing, and mitigating vulnerabilities, organizations can significantly enhance their security posture.
Comments are closed.