Mapping A Control In Trustops

Control Mapping What It Is How It Can Help Simplify Your Compliance How does trustops help with mapping controls? trustops, through trustcloud’s common controls framework (tcccf), simplifies the process of mapping controls to custom controls and certified compliance standards. Learn how to map policies and evidence to security controls in a clear, practical way to improve compliance, audit readiness, and control visibility.
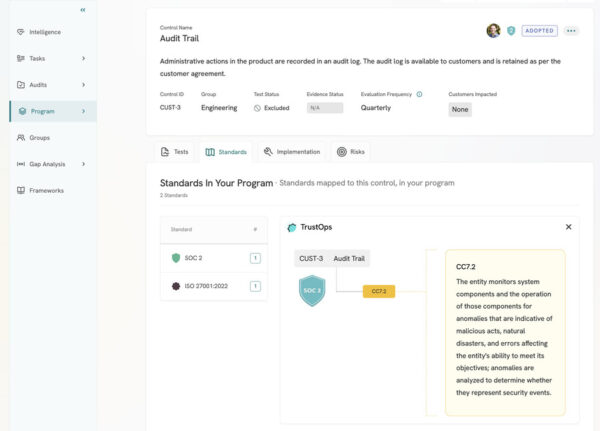
Mapping A Control In Trustops Controls can’t just be created and then forgotten, they need to be monitored to verify the supply of evidence, assess the quality of the control statements, and ensure that controls are appropriately mapped to your organization's needs and compliance standards. Learn how to design controls aligned to trust services criteria with traceable evidence, risk alignment, and audit ready documentation. Mapping controls to real teams is the step that turns shared responsibility from an external provider customer idea into an internal operating model. Controls overview all you need to know about controls in trustops for trustcloud documentation & grc resources visit: more.
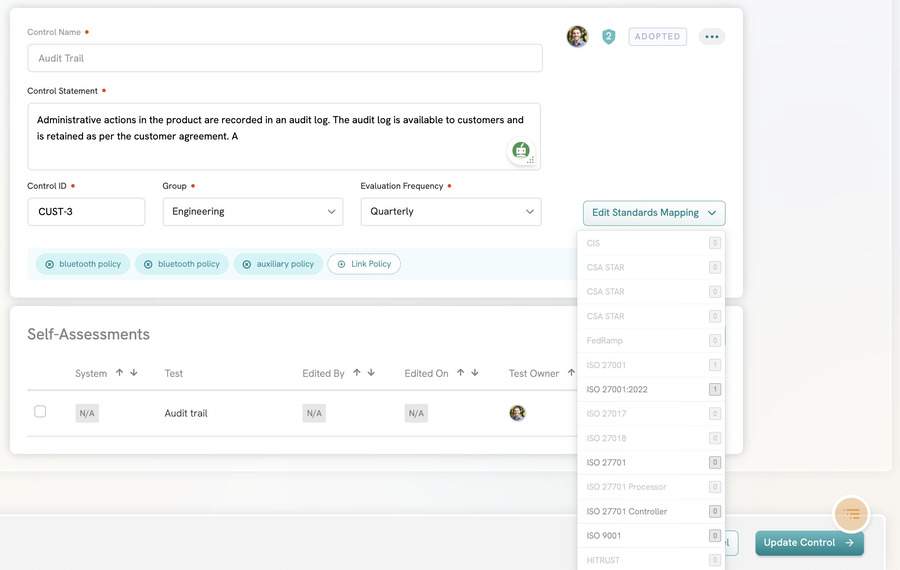
Mapping A Control In Trustops Mapping controls to real teams is the step that turns shared responsibility from an external provider customer idea into an internal operating model. Controls overview all you need to know about controls in trustops for trustcloud documentation & grc resources visit: more. Our framework is designed to map controls to major industry standards and regulations, including soc 2, iso 27001, hipaa, and gdpr. we automate the verification of these controls, simplifying the path to certification and ensuring ongoing adherence to data protection and privacy requirements. In this paper, we argue that gathering verifiable evidence during software development and operations is needed for creating a new trust model. Keep ai systems documented, traceable, and compliant over time. apply standards aligned controls, collect evidence automatically, and stay audit ready at scale. Objective create and manage mapping tables that define which users can access which data, enabling granular row level security controls.
Comments are closed.