Malware Representation Using Graphs

Malware Representation Using Graphs Our paper focuses on analyzing recent research studies based on such methods for malware detection, starting from the extraction of graph structured data using reverse engineering tools, to the classification of malware based on graph embeddings. To address these challenges, this paper integrates novel graph reduction techniques and gnn explainability in to a malware detection framework to enhance both efficiency and interpretability.

Malware Detection And Classification Based On Graph Convolutional Therefore, we propose a control flow graph (cfg) and graph isomorphism network (gin) based malware classification system. It is a graphical representation of the execution flow of a program, which can be used to identify abnormal patterns and malicious behavior in the program. in cybersecurity, cfg analysis has become a critical static analysis technique for malware detection. In this section, we describe ways to represent malware as expressive graph structures along with a general methodology to leverage graph representation learning in downstream malware detection tasks. In this paper, we propose a new framework for malware detection that uses graph based methodologies using api call sequences and dlls to construct meaningful graph representations.
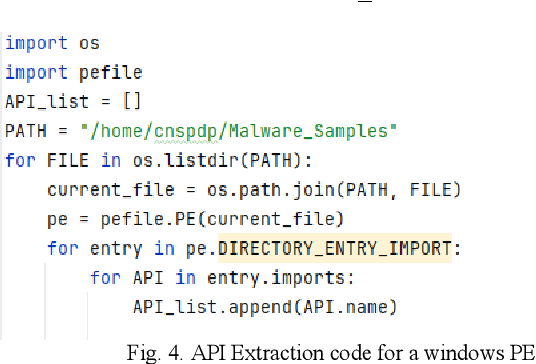
Figure 4 From Malware Detection Using Control Flow Graphs Semantic In this section, we describe ways to represent malware as expressive graph structures along with a general methodology to leverage graph representation learning in downstream malware detection tasks. In this paper, we propose a new framework for malware detection that uses graph based methodologies using api call sequences and dlls to construct meaningful graph representations. In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. To address the challenges of privacy preservation, scalability, and resistance to various malware attacks in ioht environments, this research proposes a shift from centralized graph neural networks (gnns) to distributed gnns using federated learning (fl). Our proposed malware detection system can directly extract cfg based graph information of malware from pe les and then compress the cfg information into the feature vector with gin. By leveraging graph structures, malware detection models can identify shared subgraph patterns, measure similarity between malware families, and uncover hidden relationships that conventional methods might miss.
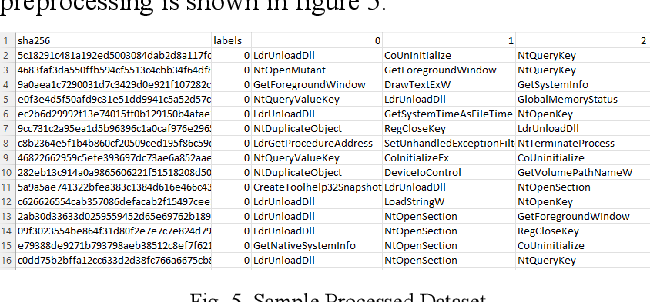
Figure 5 From Malware Detection Using Control Flow Graphs Semantic In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. To address the challenges of privacy preservation, scalability, and resistance to various malware attacks in ioht environments, this research proposes a shift from centralized graph neural networks (gnns) to distributed gnns using federated learning (fl). Our proposed malware detection system can directly extract cfg based graph information of malware from pe les and then compress the cfg information into the feature vector with gin. By leveraging graph structures, malware detection models can identify shared subgraph patterns, measure similarity between malware families, and uncover hidden relationships that conventional methods might miss.
Comments are closed.