Malware Hashes And Hash Functions
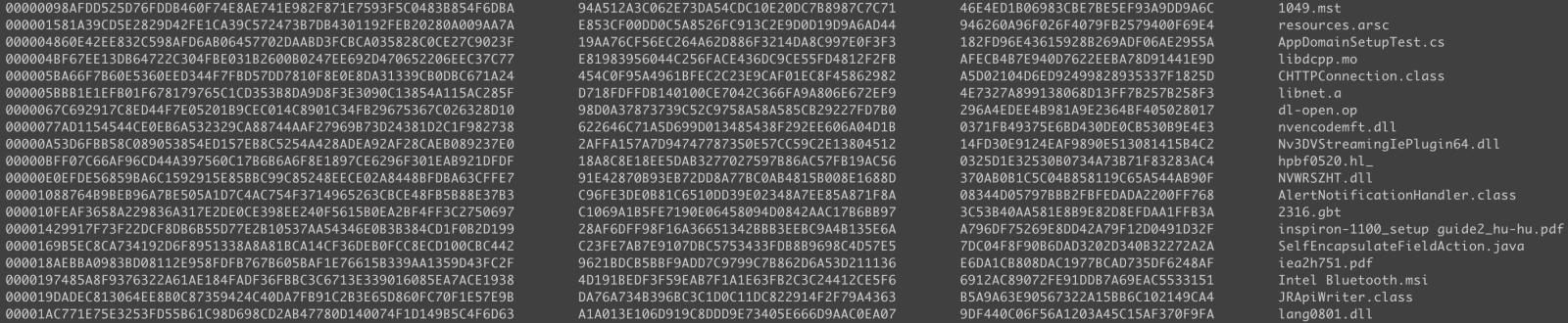
Goodware Hash Sets Sans Internet Storm Center Learn how malware hashes are used in cybersecurity to detect, block, and analyze threats across networks and systems. File hashes let analysts quickly check a suspicious file against known malware. hashing (e.g., md5 sha1 sha256) is lightweight, so huge malware collections can be indexed and searched efficiently.
Cloud Computing Patterns Mechanisms Malware Hash Arcitura Patterns We evaluate the limits and benefits of applying similarity hashing functions for malware detection and classification in real world scenarios, investigate the impact of removing common blocks from the similarity scoring, and show the issues of using av labels as ground truth from malware clustering. The output is known as a hash, hash code, hash sum, hash value, checksum, digital fingerprint, or message digest. a hash calculated for a malware file is a malware hash. Hashes are important for malware analysis. but why do so many of them exist and when should you use which hash function? let's shine a light on this. To help in bridging this gap, we performed a set of experiments to characterize the application of these functions on long term, realistic malware analysis scenarios.
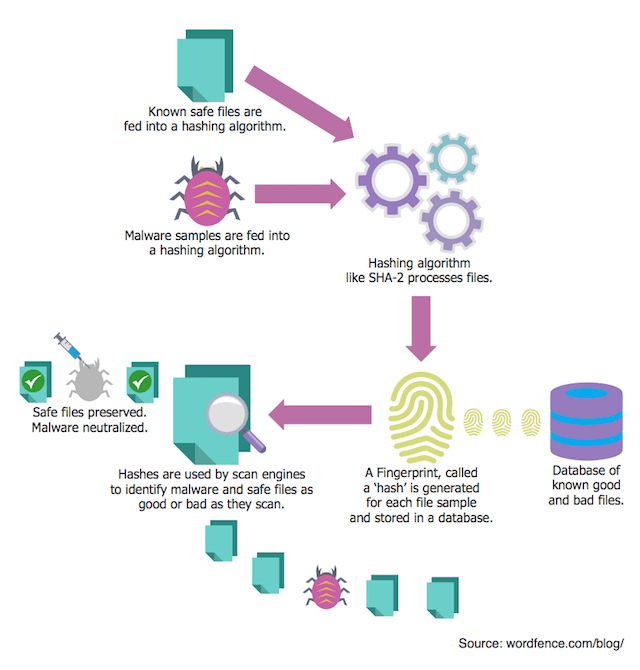
Avoid Malware Scanners That Use Insecure Hashing Hashes are important for malware analysis. but why do so many of them exist and when should you use which hash function? let's shine a light on this. To help in bridging this gap, we performed a set of experiments to characterize the application of these functions on long term, realistic malware analysis scenarios. Hashes are a nice way to identify malware samples, payload, or any type of suspicious files (i usually share the hash of the malware analyzed in my diaries). in your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes. This blog post explains how our team developed an approach that can take a collection of known malware files and use their section hashes to identify and analyze other candidate files in a malware repository. The author provides a practical demonstration using a powershell script to hash function names and a c program to dynamically resolve the hashed function addresses. the article emphasizes the effectiveness of api hashing in malware evasion and the challenges it poses to security analysts. In this work, we explore an automated approach to deobfuscate api hashing. by leveraging dynamic program analysis, we identify and map hash values back to their original function names while also extracting information about the hashing scheme.
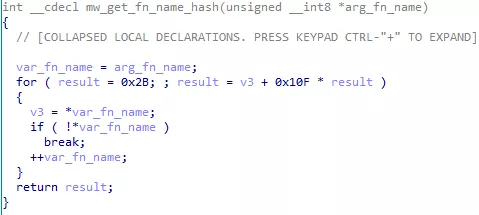
Sodinokibi Revil Malware Analysis Amossys Hashes are a nice way to identify malware samples, payload, or any type of suspicious files (i usually share the hash of the malware analyzed in my diaries). in your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes. This blog post explains how our team developed an approach that can take a collection of known malware files and use their section hashes to identify and analyze other candidate files in a malware repository. The author provides a practical demonstration using a powershell script to hash function names and a c program to dynamically resolve the hashed function addresses. the article emphasizes the effectiveness of api hashing in malware evasion and the challenges it poses to security analysts. In this work, we explore an automated approach to deobfuscate api hashing. by leveraging dynamic program analysis, we identify and map hash values back to their original function names while also extracting information about the hashing scheme.
Comments are closed.