Malware Classification W Graph Hash An Evan S Production

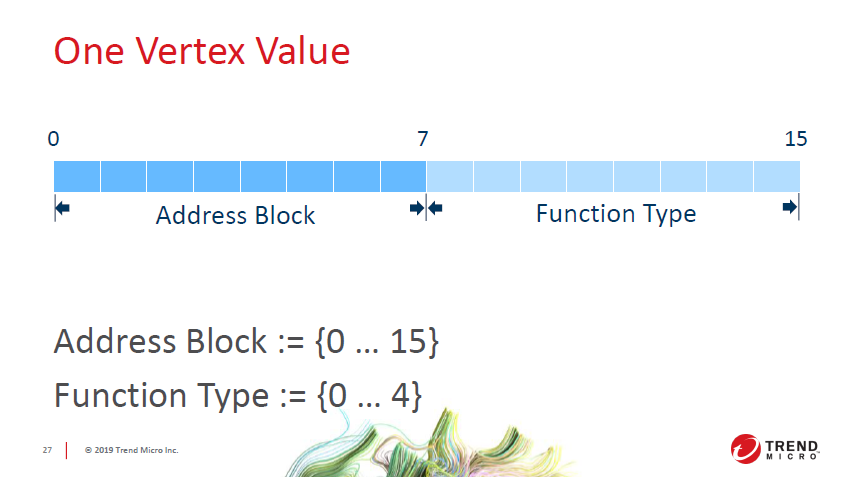
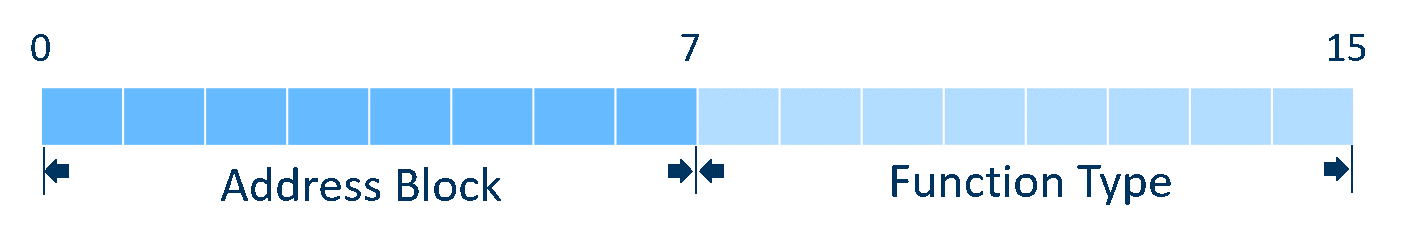
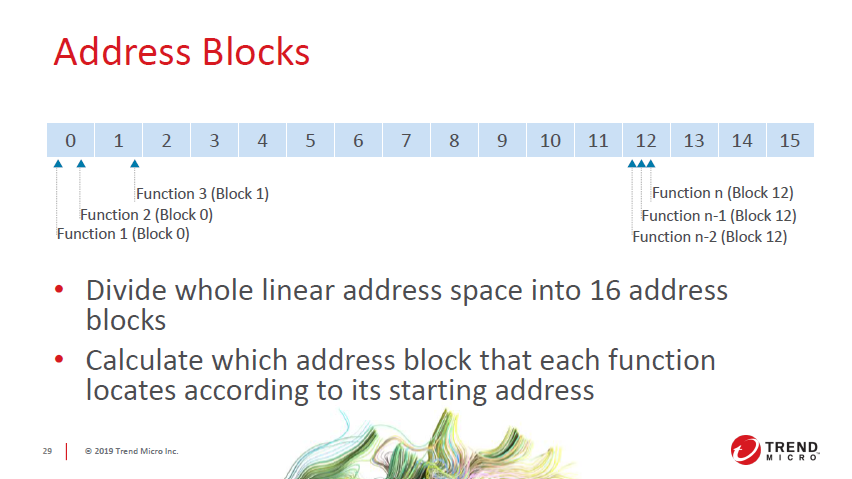
Malware Detection And Classification Based On Graph Convolutional Ssdeep: generate fuzzy hash sdhash imphash: md5 hash based on iat (pe.get imphash ()) impfuzzy: ssdeep hash based on iat t rend micro l ocality s ensitive h ashing bindiff graph hash basic concepts c all g raph p attern (dfs) c all g raph: {v ertices, e dges} v ertices: functions e dges: {a, b} (func a calls func b) vertex value references. Malware accesses important and personal data, damages the operating and network system, or performs various improper activities. it causes huge losses to businesses or individuals. thus, we developed a malware detection and classification method using a graph neural network (gnn) and deep learning.
Malware Classification W Graph Hash An Evan S Production In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. A simple classifier that chooses the predicted label by the majority in the subgraphs has been developed as a baseline. to use this on preprocessed data, the vote [binary|multiclass].py scripts in the scripts directory can be used. In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. In a method we've called “graph hash,” we calculated the hash of executable files using a graph view, which would help in classifying malware more efficiently. this research aims to provide a viable approach to malware classification.
Malware Classification W Graph Hash An Evan S Production In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. In a method we've called “graph hash,” we calculated the hash of executable files using a graph view, which would help in classifying malware more efficiently. this research aims to provide a viable approach to malware classification. To our knowledge, this paper is the first study to explore the application of graph neural network in the field of malware classification. we develop a prototype system named gdroid. In this work, graph neural networks (gnn) with function embedding techniques are used to classify malware into families. similarity analyses between malware codes must typically be conducted as part of the malware analysis to determine the relationship between two malware samples. Our paper focuses on analyzing recent research studies based on such methods for malware detection, starting from the extraction of graph structured data using reverse engineering tools, to the classification of malware based on graph embeddings. Our research, which we’ve named “ graph hash,” builds on the advantages of these two approaches by calculating the hash of executable files using a graph view, which would help in classifying malware more consistently and efficiently.
Malware Classification W Graph Hash An Evan S Production To our knowledge, this paper is the first study to explore the application of graph neural network in the field of malware classification. we develop a prototype system named gdroid. In this work, graph neural networks (gnn) with function embedding techniques are used to classify malware into families. similarity analyses between malware codes must typically be conducted as part of the malware analysis to determine the relationship between two malware samples. Our paper focuses on analyzing recent research studies based on such methods for malware detection, starting from the extraction of graph structured data using reverse engineering tools, to the classification of malware based on graph embeddings. Our research, which we’ve named “ graph hash,” builds on the advantages of these two approaches by calculating the hash of executable files using a graph view, which would help in classifying malware more consistently and efficiently.
Comments are closed.