Malware Analysis Pdf Malware Computer Science

Malware Analysis On Pdf Pdf Malware Sensitivity And Specificity As new malware analysis techniques are developed, malware authors respond with new techniques to thwart analysis. to succeed as a malware analyst, you must be able to recognize, understand, and defeat these techniques, and respond to changes in the art of malware analysis. This paper provides an in‐depth overview on malware types, by analyzing the malware via a process called malware analysis, and other related processes depending on the type of malware.

Malware Analysis Pdf Malware Computer Virus Malwares are continuously growing in sophistication and numbers. over the last decade, remarkable progress has been achieved in anti malware mechanisms. however, several pressing issues (e.g., unknown malware samples detection) still need to be addressed adequately. In this survey, we comprehensively review the current state of the art ml based malware detection techniques and popular xai approaches. additionally, we discuss research implementations and the challenges of explainable malware analysis. This work has systematically reviewed the most advanced techniques in malware detection, highlighting the fundamental role that machine learning, deep learning, static analysis, dynamic analysis, and computer vision technologies play in cybersecurity. The malware analysis special interest group from first started this framework to enable interested people to get a first footstep into the topic and to find useful resources to support their learning process.

Understanding Malware Analysis Fundamentals Pdf Malware Computing This work has systematically reviewed the most advanced techniques in malware detection, highlighting the fundamental role that machine learning, deep learning, static analysis, dynamic analysis, and computer vision technologies play in cybersecurity. The malware analysis special interest group from first started this framework to enable interested people to get a first footstep into the topic and to find useful resources to support their learning process. This study is a systematic review of malware analysis and detection in four (4) different citation databases and considers the total of 262 research articles published from 2014 to 2024. This paper presents a brief study of malwares, overview of different kinds of malware, camouflage evolution in malware, malware obfuscation techniques, malware analysis techniques and malware detection methods. This document is a comprehensive guide to advanced malware analysis, covering both static and dynamic analysis techniques, threat intelligence, and incident response strategies. This is a book about malware. the links and software described in this book are malicious. exercise extreme caution when executing for hints about creating a safe virtualized environment for.
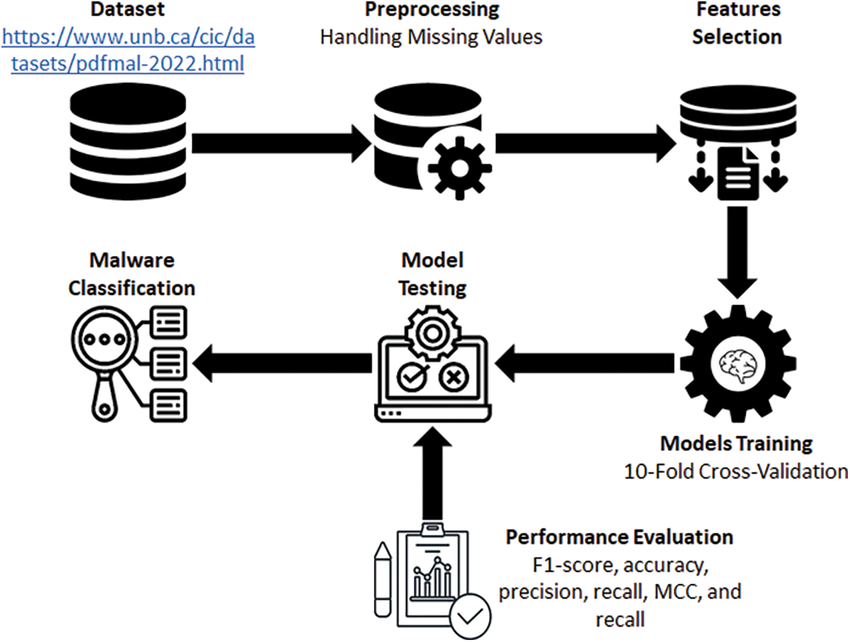
Detecting Evasive Pdf Malware A Comparative Analysis Of Advanced This study is a systematic review of malware analysis and detection in four (4) different citation databases and considers the total of 262 research articles published from 2014 to 2024. This paper presents a brief study of malwares, overview of different kinds of malware, camouflage evolution in malware, malware obfuscation techniques, malware analysis techniques and malware detection methods. This document is a comprehensive guide to advanced malware analysis, covering both static and dynamic analysis techniques, threat intelligence, and incident response strategies. This is a book about malware. the links and software described in this book are malicious. exercise extreme caution when executing for hints about creating a safe virtualized environment for.

Malware Analysis Pdf Malware Computer Virus This document is a comprehensive guide to advanced malware analysis, covering both static and dynamic analysis techniques, threat intelligence, and incident response strategies. This is a book about malware. the links and software described in this book are malicious. exercise extreme caution when executing for hints about creating a safe virtualized environment for.

Malware Analysis Pdf Malware Software Engineering
Comments are closed.