Malware Analysis Of Xor Encrypted Shellcode
Sans Digital Forensics And Incident Response Blog Tools For Examining By employing xor encryption, attackers can disguise their shellcode, making it harder for security mechanisms to detect and analyze. when it comes to execution, the encrypted shellcode must first undergo decryption using the correct key. This post will first show the steps in writing a simple malware program to inject shellcode into a remote target process by suppling the pid.

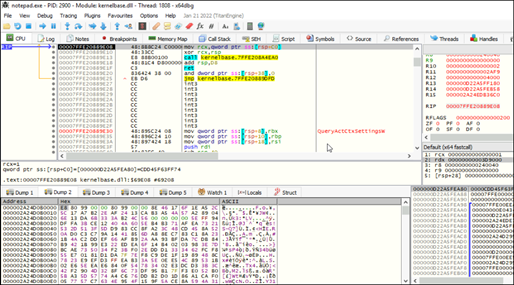
Malware Development Journey Xor Payload Encryption Rc4 Payload Introduction this write up documents my analysis of challenge 4 (apt9001) from mandiant's flare on reverse engineering ctf. the challenge involved a malicious pdf containing embedded javascript, a heap spray exploit, and x86 shellcode protected by self modifying code with multi layer xor encryption. this was not a straightforward solve. With our shellcode in hand, we now need to encrypt it using xor and a key of our choice. to do this, i created a simple python script that encrypts the data entered into it using a key. First, you need to obtain a usable shellcode from metasploit (run it from a kali distribution), so something like: second, run the shellcode encoder.py script along with the desired arguments: this will generate c#, c and python code file in the result folder. those files are ready to use compile. encrypting shellcode to bypass av . In malware and loaders, xor is popular because it’s extremely fast, tiny in code size, and easy to implement in assembly or c. attackers often xor strings, shellcode, or dll blobs on disk.

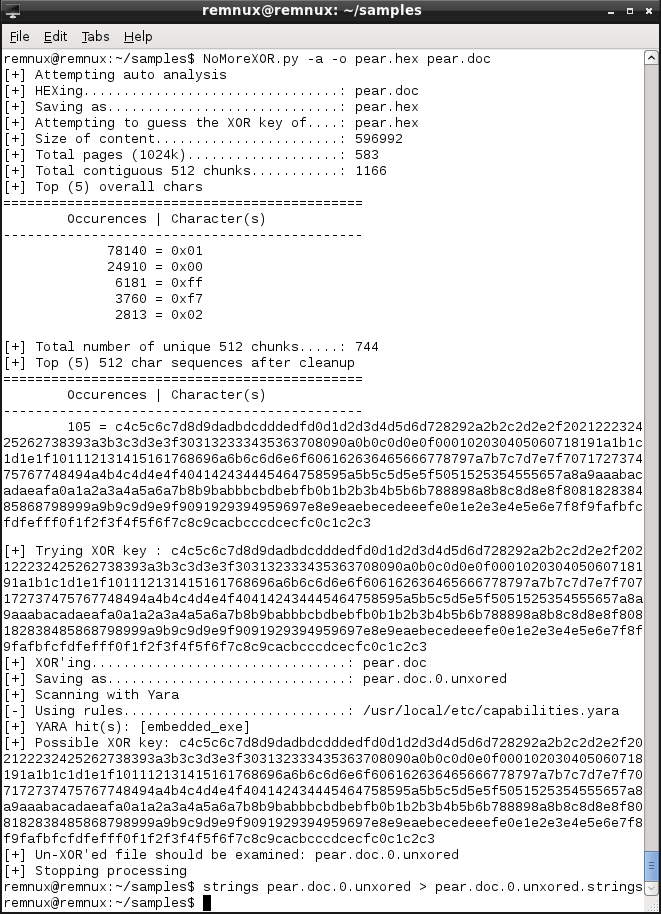
Xworm Malware Analysis New Tricks For An Old Payload First, you need to obtain a usable shellcode from metasploit (run it from a kali distribution), so something like: second, run the shellcode encoder.py script along with the desired arguments: this will generate c#, c and python code file in the result folder. those files are ready to use compile. encrypting shellcode to bypass av . In malware and loaders, xor is popular because it’s extremely fast, tiny in code size, and easy to implement in assembly or c. attackers often xor strings, shellcode, or dll blobs on disk. This blog post will go over solving an easy exploitation challenge called “execute” from hack the box where it implements a simple detection mechanism in the form of a byte blacklist that blocks certain common bytes that often show up in shellcode. Here's a look at several tools for deobfuscating xor encoded data during static malware analysis. we'll cover xorsearch, xorstrings, xorbruteforcer, brutexor and nomorexor. Xor obfuscation helps malware bypass signature based detection by altering its binary structure. attackers use xor to conceal shellcode within exploits, making detection harder. sensitive data is xor encrypted before exfiltration to avoid network security monitoring. Analyze shellcode for malware research: understand structure, identify encoding schemes, use emulators and debuggers, and extract iocs from malicious code.

Xworm Malware Analysis New Tricks For An Old Payload This blog post will go over solving an easy exploitation challenge called “execute” from hack the box where it implements a simple detection mechanism in the form of a byte blacklist that blocks certain common bytes that often show up in shellcode. Here's a look at several tools for deobfuscating xor encoded data during static malware analysis. we'll cover xorsearch, xorstrings, xorbruteforcer, brutexor and nomorexor. Xor obfuscation helps malware bypass signature based detection by altering its binary structure. attackers use xor to conceal shellcode within exploits, making detection harder. sensitive data is xor encrypted before exfiltration to avoid network security monitoring. Analyze shellcode for malware research: understand structure, identify encoding schemes, use emulators and debuggers, and extract iocs from malicious code.
Xworm Malware Analysis New Tricks For An Old Payload Xor obfuscation helps malware bypass signature based detection by altering its binary structure. attackers use xor to conceal shellcode within exploits, making detection harder. sensitive data is xor encrypted before exfiltration to avoid network security monitoring. Analyze shellcode for malware research: understand structure, identify encoding schemes, use emulators and debuggers, and extract iocs from malicious code.
Xworm Malware Analysis New Tricks For An Old Payload
Comments are closed.