Malware Analysis Malicious Nordvpn Setup Beginner Sample
Malware Analysis Malicious Activity Verloop Io Recently, a malicious installer disguised as the legitimate nordvpn setup has been circulating online, targeting unsuspecting users. this example demonstrates typical behaviors of beginner level malware, including persistence, basic data collection, and communication with a command and control (c2) server. We analyze a trojanized setup file. the analysis of this sample is pretty straightforward if you know where to look. but as a beginner it can be challenging if you don't.
Nordvpn S Malware Scanner Malware Free Browsing Nordvpn The analysis of this sample is pretty straightforward if you know where to look. but for new analysts, it can be challenging if you don't. i recommend analyzing it before watching the video. Sample uses string decryption to hide its real strings contains functionality to compare user and computer (likely to detect sandboxes) tries to harvest and steal browser information (history, passwords, etc) drops executable to a common third party application directory pe file has nameless sections source code contains very large strings. Introduction to malware binary triage (imbt) course looking to level up your skills? get 10% off using coupon code: mwnews10 for any flavor. enroll now and save 10%: coupon code mwnews10. The analysis of this nordvpn installer reveals a carefully constructed attack that exploits user trust. the malware authors did not employ sophisticated code obfuscation or zero day exploits.

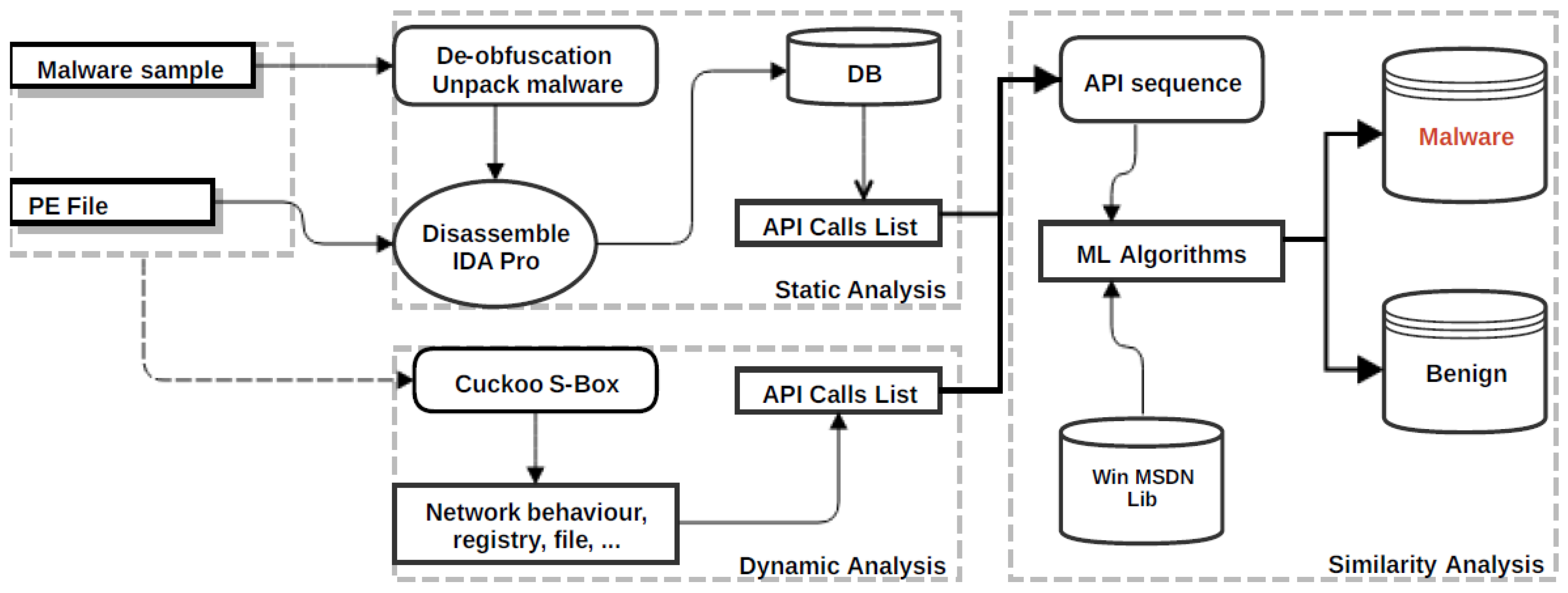
How To Write A Malware Analysis Report Cyber Security News Introduction to malware binary triage (imbt) course looking to level up your skills? get 10% off using coupon code: mwnews10 for any flavor. enroll now and save 10%: coupon code mwnews10. The analysis of this nordvpn installer reveals a carefully constructed attack that exploits user trust. the malware authors did not employ sophisticated code obfuscation or zero day exploits. This malware is a multi stage windows threat designed to persist on the system, hijack browser traffic, and enable large scale https interception through an attacker controlled proxy. Objective: learn how to safely execute and monitor malware in a virtual machine to observe its behavior. tasks: set up a sandbox environment, use tools like process monitor, wireshark, and regshot to monitor system changes and network activity, and create a detailed report on the malware's actions. Nordvpn.exe (pid: 3652) nordvpn.exe (pid: 440) the sample compiled with english language support nordvpn.exe (pid: 3652) dfsvc.exe (pid: 6224) nordvpn.exe (pid: 440) xcopy.exe (pid: 396) process checks whether uac notifications are on dfsvc.exe (pid: 6224) reads the computer name nordvpn.exe (pid: 3652) dfsvc.exe (pid: 6224) nordvpn.exe (pid: 440). For this blog, we performed a deep dive technical analysis of the malicious setup files, the evasion techniques used, and the final payload delivered. the attack starts when users visit a lookalike website registered by the threat actor to distribute vpn applications.
Malware Analysis Start Me This malware is a multi stage windows threat designed to persist on the system, hijack browser traffic, and enable large scale https interception through an attacker controlled proxy. Objective: learn how to safely execute and monitor malware in a virtual machine to observe its behavior. tasks: set up a sandbox environment, use tools like process monitor, wireshark, and regshot to monitor system changes and network activity, and create a detailed report on the malware's actions. Nordvpn.exe (pid: 3652) nordvpn.exe (pid: 440) the sample compiled with english language support nordvpn.exe (pid: 3652) dfsvc.exe (pid: 6224) nordvpn.exe (pid: 440) xcopy.exe (pid: 396) process checks whether uac notifications are on dfsvc.exe (pid: 6224) reads the computer name nordvpn.exe (pid: 3652) dfsvc.exe (pid: 6224) nordvpn.exe (pid: 440). For this blog, we performed a deep dive technical analysis of the malicious setup files, the evasion techniques used, and the final payload delivered. the attack starts when users visit a lookalike website registered by the threat actor to distribute vpn applications.

Malware Analysis Lab Cyber Security Crafts Nordvpn.exe (pid: 3652) nordvpn.exe (pid: 440) the sample compiled with english language support nordvpn.exe (pid: 3652) dfsvc.exe (pid: 6224) nordvpn.exe (pid: 440) xcopy.exe (pid: 396) process checks whether uac notifications are on dfsvc.exe (pid: 6224) reads the computer name nordvpn.exe (pid: 3652) dfsvc.exe (pid: 6224) nordvpn.exe (pid: 440). For this blog, we performed a deep dive technical analysis of the malicious setup files, the evasion techniques used, and the final payload delivered. the attack starts when users visit a lookalike website registered by the threat actor to distribute vpn applications.
Comments are closed.