Malware Analysis File Pptx

Malware Analysis Pdf Malware File Format To safely conduct malware analysis, one should create an isolated virtual lab separated from production networks, and install behavioral monitoring and code analysis tools like ollydbg, process monitor, and wiresh download as a pptx, pdf or view online for free. This is a completely adaptable powerpoint template design that can be used to interpret topics like malware analysis, dynamic malware, manual malware. so download instantly and tailor it with your information.

Malware Analysis File 2 Pptx Pptx Malware analysis of files, detect the type of malware and check whether its a malware or not by using virus total. malware analysis malware.pptx at main · nitya123 github malware analysis. Malware analysis ppt free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. this document discusses malware analysis using machine learning techniques. Malware is one of the most significant security risks because it spreads on its own through human weaknesses or irresponsibility. it is critical to effectively identify malware in order to prevent a computer from infection or remove malware from a compromised computer system. This repository contains the documentation, presentation, and resources for our project on malware analysis and prevention strategy, featuring the implementation of a wazuh security information and event management (siem) system.
Malware Analysis File Pptx Malware is one of the most significant security risks because it spreads on its own through human weaknesses or irresponsibility. it is critical to effectively identify malware in order to prevent a computer from infection or remove malware from a compromised computer system. This repository contains the documentation, presentation, and resources for our project on malware analysis and prevention strategy, featuring the implementation of a wazuh security information and event management (siem) system. It also lists resources for malware analysis like tools for static analysis, reverse engineering, and reporting. download as a pptx, pdf or view online for free. This easy to customize presentation on malware analysis will stun your audience with its captivating layouts. available for powerpoint and google slides!. Understanding malware is crucial for protecting data and preventing financial losses, as it spreads through phishing emails, malicious downloads, and software vulnerabilities. Embedded a backdoor in executable file using veil evasion, and metasploit framework to establish connection between kali linux and windows. then to detect and analyse this malware, we used static and dynamic analysis.
Malware Analysis File Pptx It also lists resources for malware analysis like tools for static analysis, reverse engineering, and reporting. download as a pptx, pdf or view online for free. This easy to customize presentation on malware analysis will stun your audience with its captivating layouts. available for powerpoint and google slides!. Understanding malware is crucial for protecting data and preventing financial losses, as it spreads through phishing emails, malicious downloads, and software vulnerabilities. Embedded a backdoor in executable file using veil evasion, and metasploit framework to establish connection between kali linux and windows. then to detect and analyse this malware, we used static and dynamic analysis.

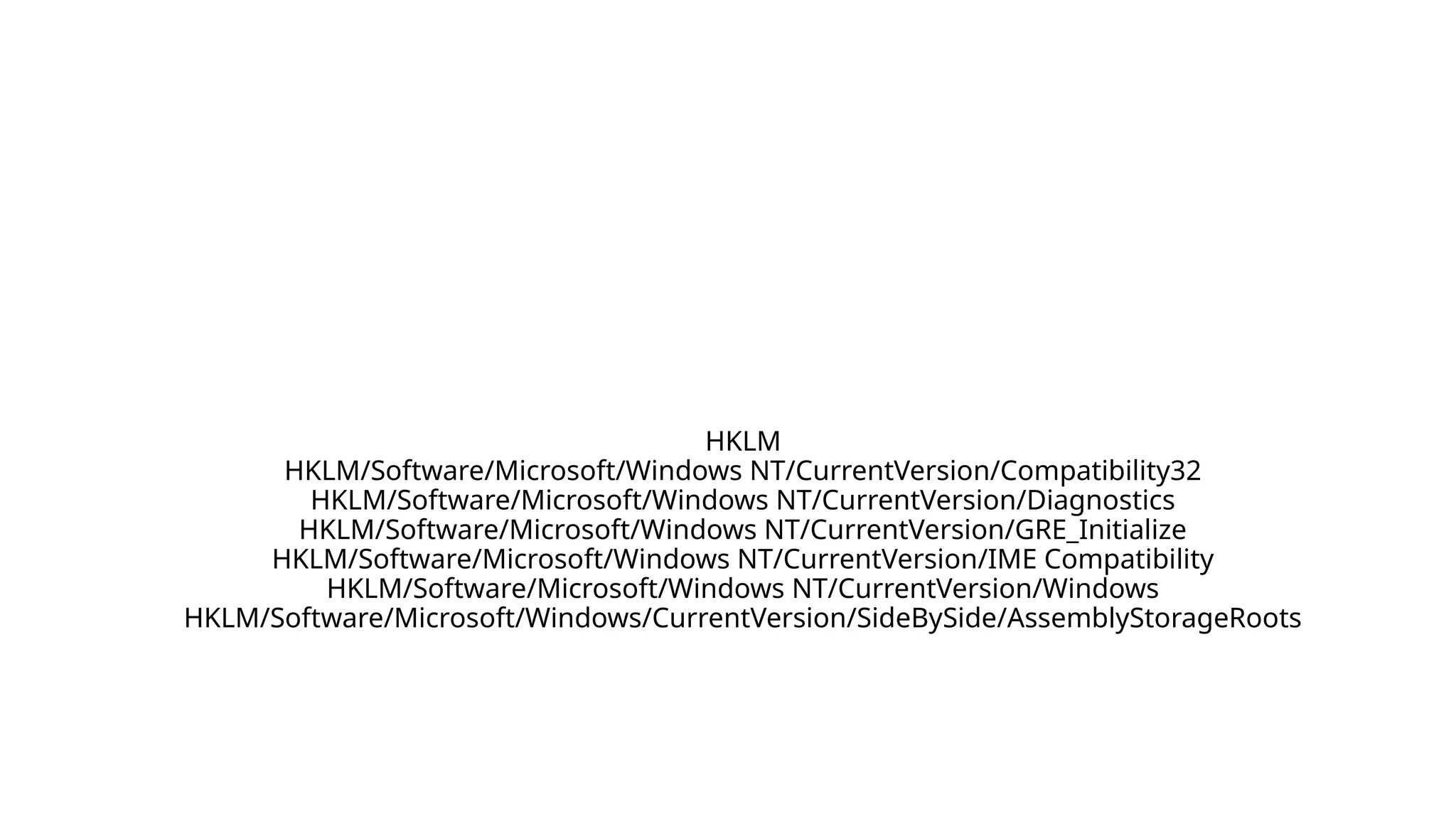
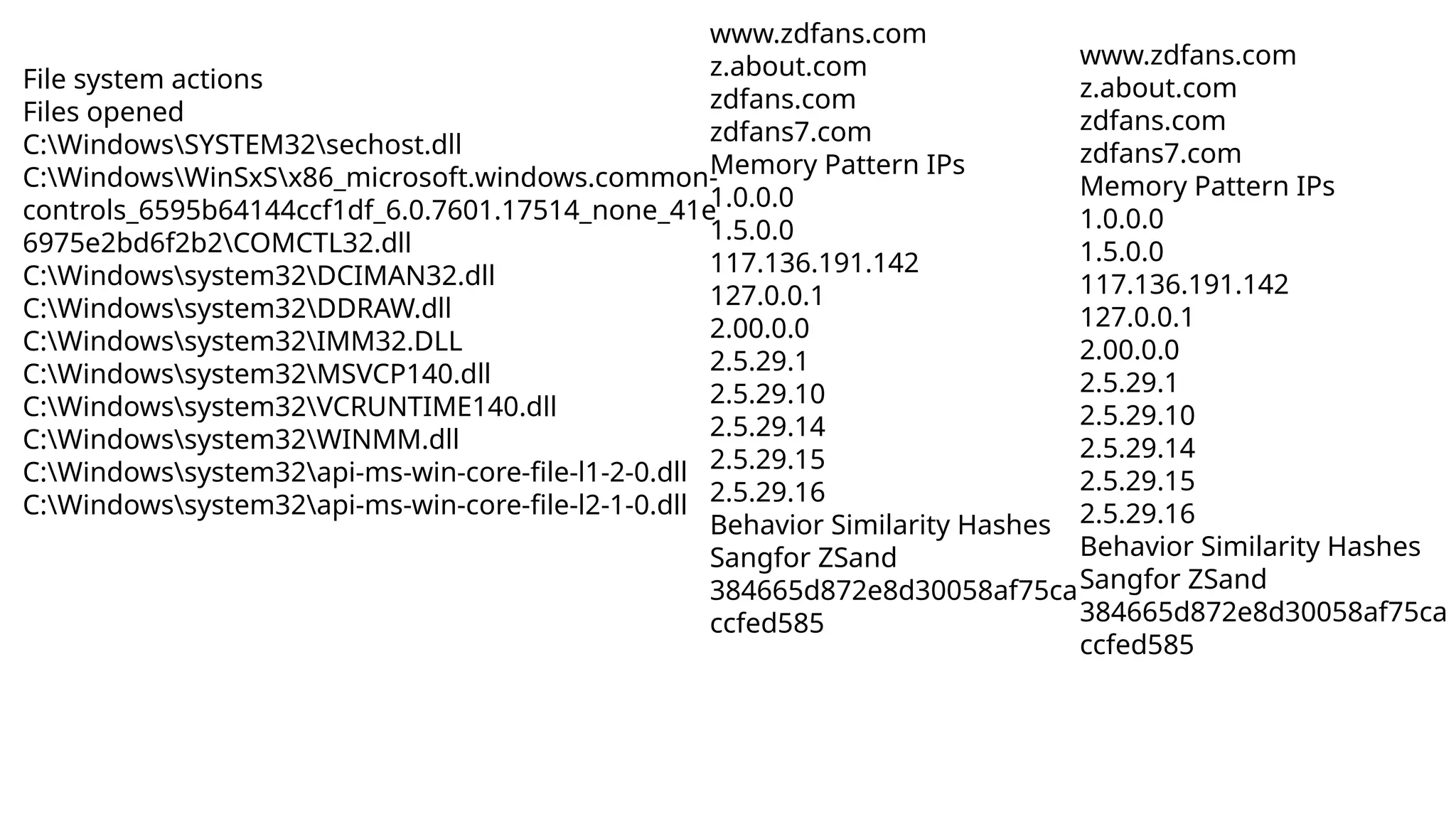
Malware Analysis Final Pptx In Cybersecuriey Pptx Understanding malware is crucial for protecting data and preventing financial losses, as it spreads through phishing emails, malicious downloads, and software vulnerabilities. Embedded a backdoor in executable file using veil evasion, and metasploit framework to establish connection between kali linux and windows. then to detect and analyse this malware, we used static and dynamic analysis.
Comments are closed.