Malicious Npm Packages Stealing Developers Sensitive Data

Malicious Npm Packages Target Ethereum Developers Private Keys Cybersecurity researchers have discovered a set of 10 malicious npm packages that are designed to deliver an information stealer targeting windows, linux, and macos systems. Cybersecurity researchers have uncovered 10 malicious npm packages targeting windows, macos, and linux.
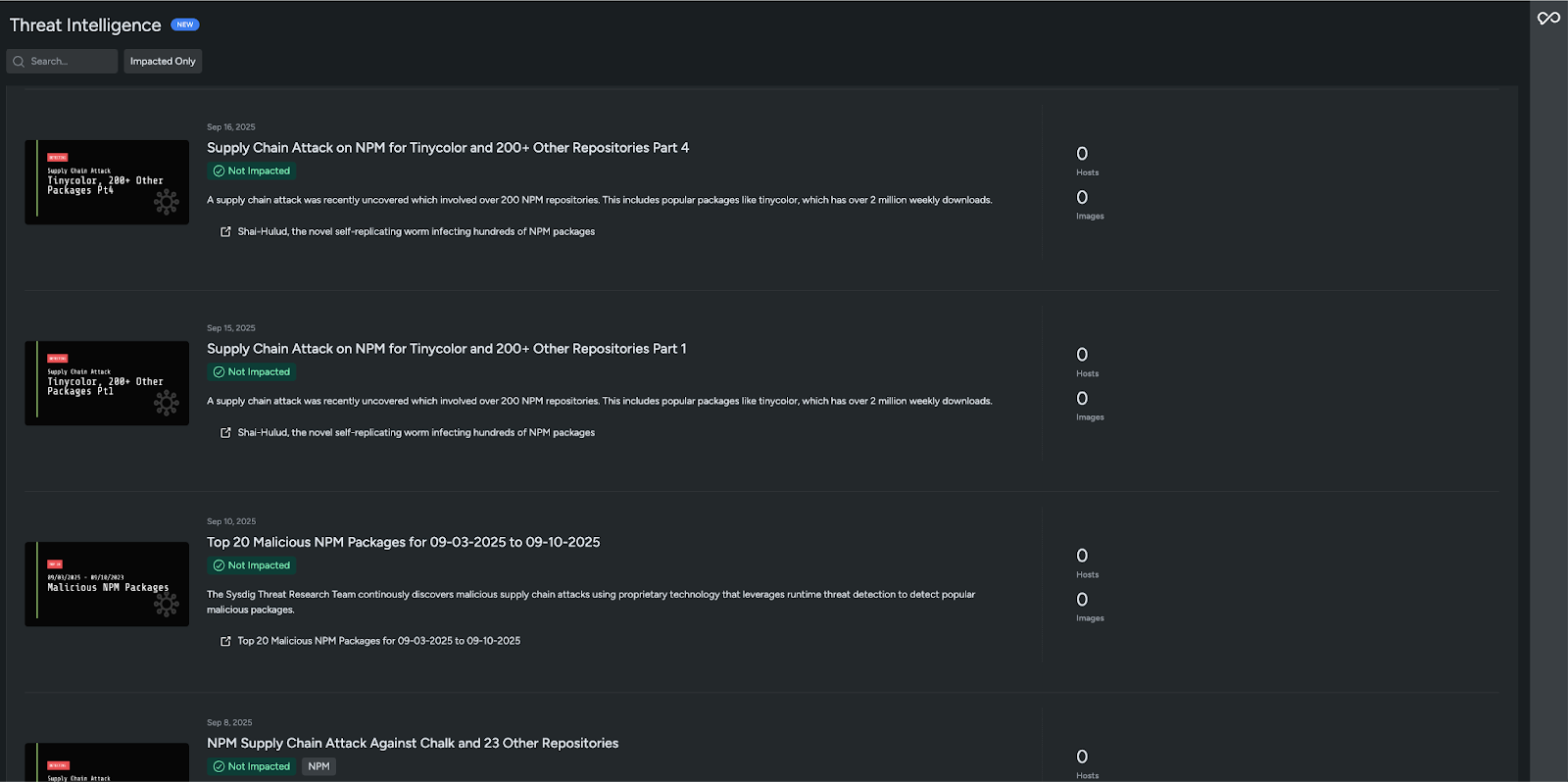
Malicious Npm Packages Are You Exposed Sysdig Ten malicious packages mimicking legitimate software projects in the npm registry download an information stealing component that collects sensitive data from windows, linux, and macos. A set of 10 malicious npm packages have been discovered that can steal sensitive developer credentials. the malicious packages impersonated popular npm libraries and served a fake captcha prompt to trick users into installing them. Cybersecurity company socket has discovered ten malicious npm packages that masquerade as widely used libraries to stealthily harvest developer credentials. this sophisticated attack uses. Ten npm packages, posing as legitimate developer tools, covertly stole credentials across windows, macos, and linux. the attack highlights urgent supply chain and open source security gaps. in october 2025, security researchers uncovered a coordinated supply chain attack targeting the npm ecosystem.

Malicious Npm Packages Are You Exposed Sysdig Cybersecurity company socket has discovered ten malicious npm packages that masquerade as widely used libraries to stealthily harvest developer credentials. this sophisticated attack uses. Ten npm packages, posing as legitimate developer tools, covertly stole credentials across windows, macos, and linux. the attack highlights urgent supply chain and open source security gaps. in october 2025, security researchers uncovered a coordinated supply chain attack targeting the npm ecosystem. Hundreds of compromised npm packages have already been found, and the list continues to grow as a major supply chain attack spreads malware. developers are urged to be extremely cautious after hackers planted malicious scripts in crowdstrike’s npm packages and other widely used libraries. npm (node package manager) is the world’s largest software registry, used by developers building web. Security researchers recently discovered that ten malicious npm packages were uploaded to the public npm registry. these packages were designed to look like legitimate ones but had slightly altered names, a trick known as typosquatting. Attackers published 10 packages that mimic well known npm projects. when a developer installs any of these packages, a malicious postinstall hook runs automatically and launches a chain of scripts that ultimately fetch and execute a 24 mb pyinstaller packed information stealer. After gaining initial access, the malicious cyber actor deployed malware that scanned the environment for sensitive credentials. the cyber actor then targeted github personal access tokens (pats) and application programming interface (api) keys for cloud services, including amazon web services (aws), google cloud platform (gcp), and microsoft.

North Korea Linked Supply Chain Attack Targets Developers With 35 Hundreds of compromised npm packages have already been found, and the list continues to grow as a major supply chain attack spreads malware. developers are urged to be extremely cautious after hackers planted malicious scripts in crowdstrike’s npm packages and other widely used libraries. npm (node package manager) is the world’s largest software registry, used by developers building web. Security researchers recently discovered that ten malicious npm packages were uploaded to the public npm registry. these packages were designed to look like legitimate ones but had slightly altered names, a trick known as typosquatting. Attackers published 10 packages that mimic well known npm projects. when a developer installs any of these packages, a malicious postinstall hook runs automatically and launches a chain of scripts that ultimately fetch and execute a 24 mb pyinstaller packed information stealer. After gaining initial access, the malicious cyber actor deployed malware that scanned the environment for sensitive credentials. the cyber actor then targeted github personal access tokens (pats) and application programming interface (api) keys for cloud services, including amazon web services (aws), google cloud platform (gcp), and microsoft.

Hackers Are Using These Malicious Npm Packages To Target Developers On Attackers published 10 packages that mimic well known npm projects. when a developer installs any of these packages, a malicious postinstall hook runs automatically and launches a chain of scripts that ultimately fetch and execute a 24 mb pyinstaller packed information stealer. After gaining initial access, the malicious cyber actor deployed malware that scanned the environment for sensitive credentials. the cyber actor then targeted github personal access tokens (pats) and application programming interface (api) keys for cloud services, including amazon web services (aws), google cloud platform (gcp), and microsoft.
Comments are closed.