Making Cents Of Malware Configurations
Extract Malware Configurations With Malconfscan Apnic Blog Making cents of malware configurations brandon murphy, konstantin klinger, jack mott suricon 2021, boston, usa. Presented at suricon 2021 by konstantin klinger, jack mott, & brandon murphymalware is increasingly using encryption and tls for command and control network.
Ebook Malware Configurations How To Find And Use Them However, configuration extractor requires redline payload to work on. step 1. throw the sample into dnspy and find the entrypoint. step 2. search for dynamic il loading apis and place a breakpoint at the instruction. Malware 101 is a complete, step by step guide on malware development. from basic concepts to advanced techniques, we'll explore malware types, build them with languages like python, rust, c c , go, and powershell, and understand how they impact systems. When all system configurations and software installations are complete, you’re able to analyze and investigate malware properly. in this post, i wanted to share my own experiences and scripts to help ease the workload of setting up a malware environment to explore malicious software. The ability to create and understand malware is essential for cybersecurity professionals to develop effective countermeasures. in this article, we explored the basics of creating a simple malware simulation using python, which is a common language used in cybersecurity for scripting and automation.
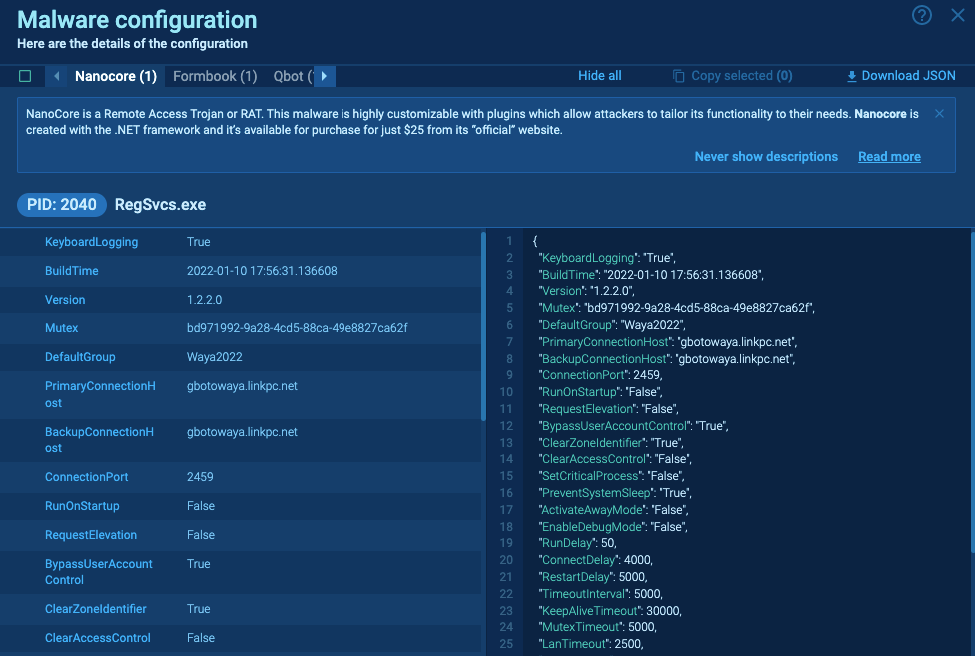
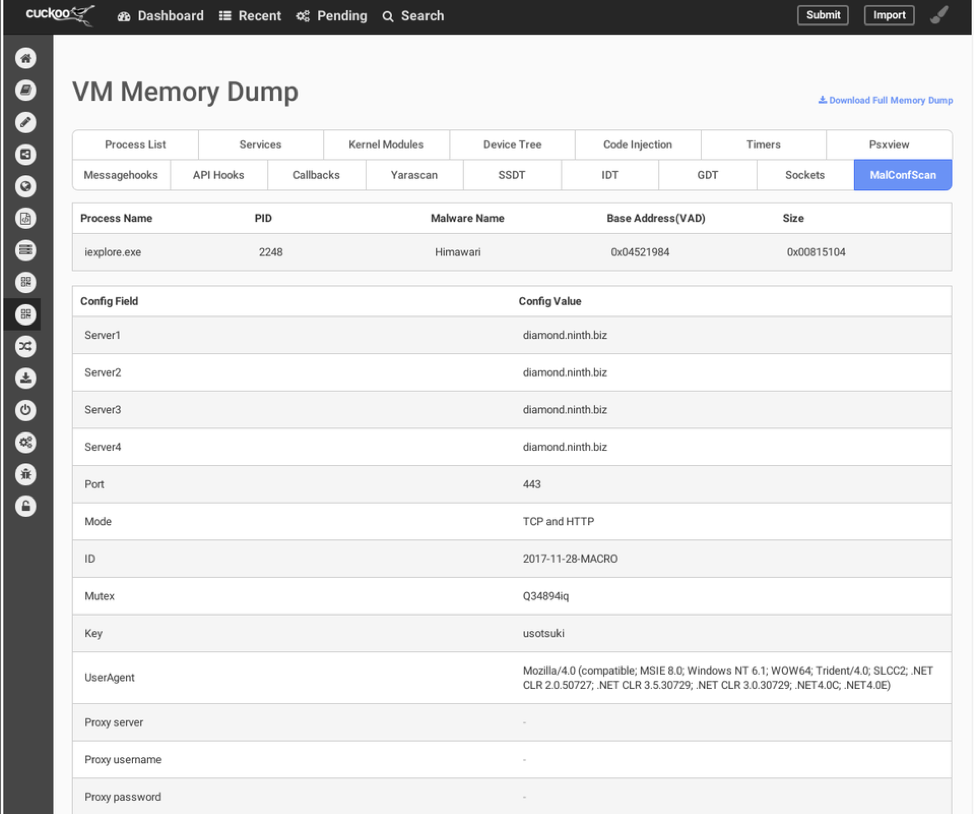
Easily Extract Malware Configuration In Any Run Any Run S When all system configurations and software installations are complete, you’re able to analyze and investigate malware properly. in this post, i wanted to share my own experiences and scripts to help ease the workload of setting up a malware environment to explore malicious software. The ability to create and understand malware is essential for cybersecurity professionals to develop effective countermeasures. in this article, we explored the basics of creating a simple malware simulation using python, which is a common language used in cybersecurity for scripting and automation. The idea of this post is to help make it a bit easier for people starting in malware development by sharing some general direction, tips, and resources i personally have used and found very useful throughout my experiences. Below is a safe, high level guide intended to help it and security professionals understand how malware is typically configured and what defensive measures and safe analysis practices can reduce risk and improve detection. Getting malware configurations is a laborious task that involves breaking through lines of heavily obfuscated code, delving into memory dumps of malware samples, reverse engineering and debugging. the challenge is even greater with modern malware that uses modular architecture. Learn why malware configuration parsing is an essential skill for any threat hunter, plus how to use a malware configuration parsers to do this automatically.
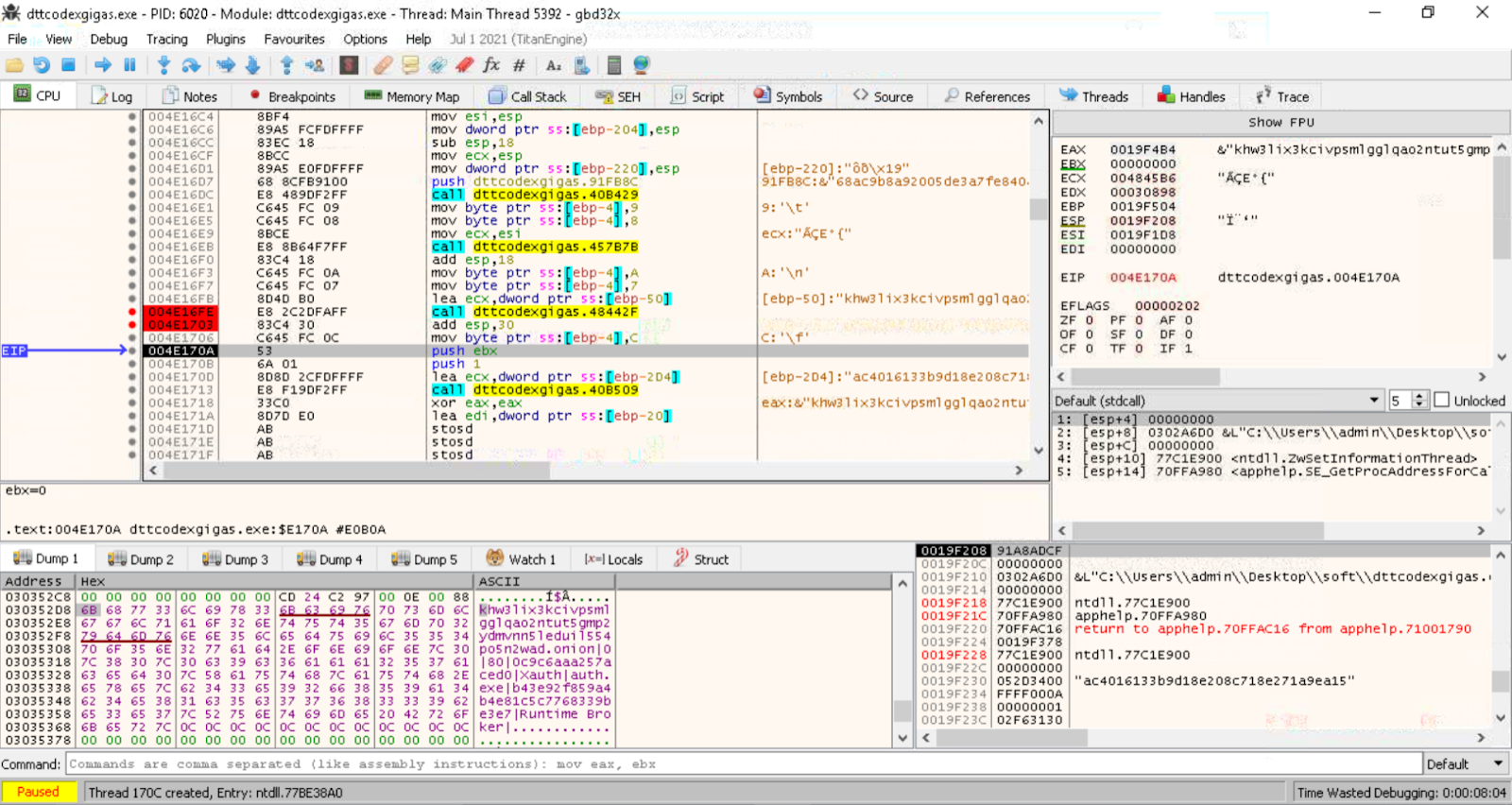
Easily Extract Malware Configuration In Any Run Any Run S The idea of this post is to help make it a bit easier for people starting in malware development by sharing some general direction, tips, and resources i personally have used and found very useful throughout my experiences. Below is a safe, high level guide intended to help it and security professionals understand how malware is typically configured and what defensive measures and safe analysis practices can reduce risk and improve detection. Getting malware configurations is a laborious task that involves breaking through lines of heavily obfuscated code, delving into memory dumps of malware samples, reverse engineering and debugging. the challenge is even greater with modern malware that uses modular architecture. Learn why malware configuration parsing is an essential skill for any threat hunter, plus how to use a malware configuration parsers to do this automatically.
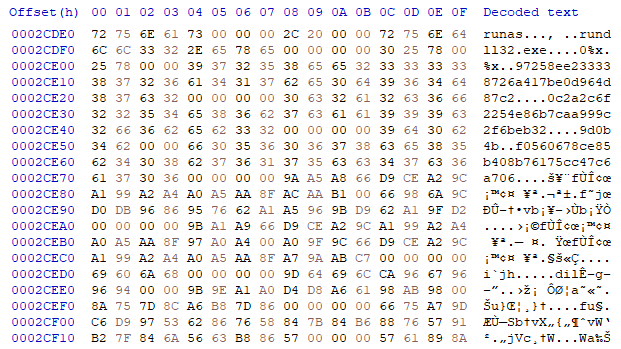
Easily Extract Malware Configuration In Any Run Any Run S Getting malware configurations is a laborious task that involves breaking through lines of heavily obfuscated code, delving into memory dumps of malware samples, reverse engineering and debugging. the challenge is even greater with modern malware that uses modular architecture. Learn why malware configuration parsing is an essential skill for any threat hunter, plus how to use a malware configuration parsers to do this automatically.

Easily Extract Malware Configuration In Any Run Any Run S
Comments are closed.