Machine Workload Identity Teleport

Introduction To Workload Identity Teleport The following steps will help you get started with machine and workload identity. at the core of this flow is tbot, a lightweight agent that runs on your machines and workloads to automatically issue and renew short lived certificates. In this video, we’ll look at how teleport machine & workload identity secures ci cd pipelines, microservices, iac configurations, ai agents, and more, by treating machines and workloads.
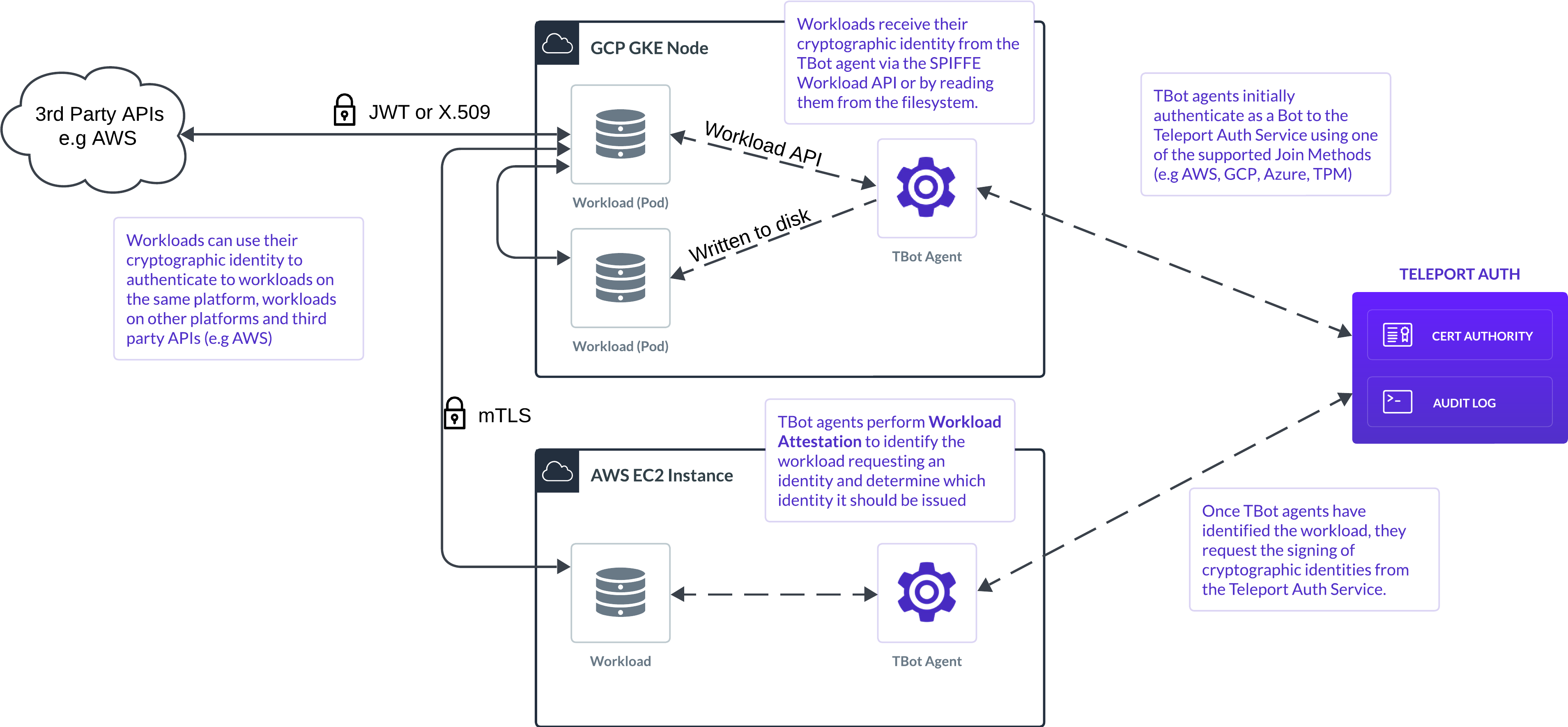
Introduction To Workload Identity Teleport Teleport announced the introduction of teleport machine & workload identity, a breakthrough solution that provides seamless authentication, authorization, and access control for non human identities across modern infrastructure environments. Teleport today added an offering that makes it simpler to declaratively secure it infrastructure and workloads using short lived x.509 certificates. Machine & workload identity is used through an agent called tbot. tbot authenticates with the teleport cluster and then generates credentials and configuration files for other tools to use to connect to teleport resources using the bot's identity. Teleport’s expansion into machine and workload identity ensures that these critical components of infrastructure receive the same level of protection as human users.

Introduction To Machine Workload Identity Teleport Machine & workload identity is used through an agent called tbot. tbot authenticates with the teleport cluster and then generates credentials and configuration files for other tools to use to connect to teleport resources using the bot's identity. Teleport’s expansion into machine and workload identity ensures that these critical components of infrastructure receive the same level of protection as human users. In this video, we’ll look at how teleport machine & workload identity secures ci cd pipelines, microservices, iac configurations, ai agents, and more, by treating machines and workloads as first class identities with short lived certificates, policy driven access, and full audit, no static secrets. In this video, we’ll look at how teleport machine & workload identity secures ci cd pipelines, microservices, iac configurations, ai agents, and more, by treating machines and workloads as first class identities with short lived certificates, policy driven access, and full audit, no static secrets. Learn more video walkthrough of the teleport machine & workload identity getting started guide documentation: goteleport docs machine w. The teleport machine & workload identity solution aims to make secure access pervasive and easier, which is key for cloud engineers who must often grant access to assets and resources on the fly to enable faster development.

Machine Workload Identity Teleport In this video, we’ll look at how teleport machine & workload identity secures ci cd pipelines, microservices, iac configurations, ai agents, and more, by treating machines and workloads as first class identities with short lived certificates, policy driven access, and full audit, no static secrets. In this video, we’ll look at how teleport machine & workload identity secures ci cd pipelines, microservices, iac configurations, ai agents, and more, by treating machines and workloads as first class identities with short lived certificates, policy driven access, and full audit, no static secrets. Learn more video walkthrough of the teleport machine & workload identity getting started guide documentation: goteleport docs machine w. The teleport machine & workload identity solution aims to make secure access pervasive and easier, which is key for cloud engineers who must often grant access to assets and resources on the fly to enable faster development.

Top Use Cases Trends In Machine Workload Identity Teleport Learn more video walkthrough of the teleport machine & workload identity getting started guide documentation: goteleport docs machine w. The teleport machine & workload identity solution aims to make secure access pervasive and easier, which is key for cloud engineers who must often grant access to assets and resources on the fly to enable faster development.
Comments are closed.