Machine Learning Ai Mitigating Insider Threats

Mitigating Insider Threats In The Age Of Ai Abacode Insider threats are on the rise. learn how ai and ml can stop them before they cause damage and strengthen your organization's defenses. This survey reviews existing research between 2010 and 2024 on detecting insider threats. it not only expounds on the novel taxonomy based on previous works and diverse motivations for insider threats but also identifies challenges and gaps in detecting malicious insiders.

Mitigating Insider Threats With Ai And Machine Learning Protecting Ai’s advanced algorithms can filter through vast amounts of data to identify patterns or behaviors within a network, flagging potential risks before they escalate into serious issues. Addressing insider’s threats is a critical challenge in organizational security. this study presents the development and evaluation of a hybrid machine learning model aimed at enhancing insider’s threat detection effectiveness. It integrates machine learning based detection controls, dynamic protections, and advanced privacy controls to help organizations effectively manage and mitigate insider risks. This research paper presents an intelligent system for insider threat detection using machine learning (ml) techniques. the system employs user behavior analytics, real time log monitoring, and anomaly detection to identify suspicious activities.
Mitigating Insider Threats With Ai And Machine Learning Protecting It integrates machine learning based detection controls, dynamic protections, and advanced privacy controls to help organizations effectively manage and mitigate insider risks. This research paper presents an intelligent system for insider threat detection using machine learning (ml) techniques. the system employs user behavior analytics, real time log monitoring, and anomaly detection to identify suspicious activities. Identifying insider threats using ai: detecting malicious behavior in corporate networks and systems via machine learning publisher: ieee pdf all authors. As insider threats grow more common—and more complex to track and prevent—insider threat programs can (and should) leverage machine learning algorithms and data mesh architecture to improve their ability to detect, monitor, and respond to suspicious network activity. Why cisos are bifurcating into proactive and wait and see camps on ai safeguard implementation; how ai driven threats have forced cybersecurity vendors to move from traditional ml to language model based detection; how proofpoint's ai security platform extends its human insider risk model to ai agents. This is where machine learning fundamentally changes what cybersecurity teams can see and respond to. this article explains how ai and machine.

Ai Driven Threat Intelligence Leveraging Machine Learning To Empower Identifying insider threats using ai: detecting malicious behavior in corporate networks and systems via machine learning publisher: ieee pdf all authors. As insider threats grow more common—and more complex to track and prevent—insider threat programs can (and should) leverage machine learning algorithms and data mesh architecture to improve their ability to detect, monitor, and respond to suspicious network activity. Why cisos are bifurcating into proactive and wait and see camps on ai safeguard implementation; how ai driven threats have forced cybersecurity vendors to move from traditional ml to language model based detection; how proofpoint's ai security platform extends its human insider risk model to ai agents. This is where machine learning fundamentally changes what cybersecurity teams can see and respond to. this article explains how ai and machine.
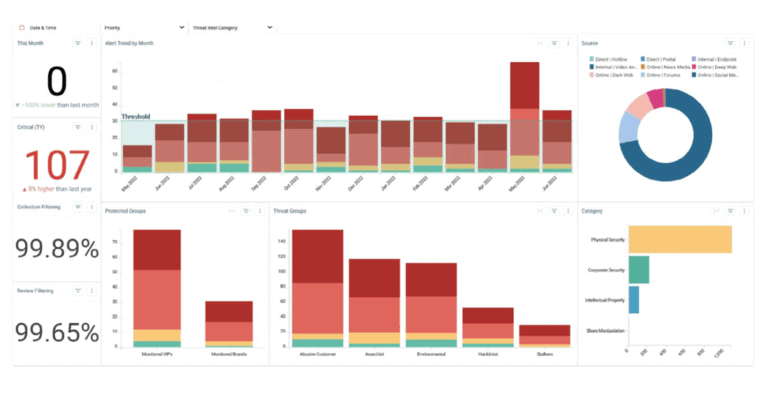
6 Strategies For Mitigating Insider Threats Resolver Why cisos are bifurcating into proactive and wait and see camps on ai safeguard implementation; how ai driven threats have forced cybersecurity vendors to move from traditional ml to language model based detection; how proofpoint's ai security platform extends its human insider risk model to ai agents. This is where machine learning fundamentally changes what cybersecurity teams can see and respond to. this article explains how ai and machine.

6 Strategies For Mitigating Insider Threats Resolver
Comments are closed.