Mac Table Flooding Attack Demonstration

4 1 42 Mac Flooding Attack Pdf In this video, we'll dive into the world of network attacks by demonstrating a mac flooding attack using kali linux. we'll start with the basics, explaining what a network switch is and how it. In this lab, we’re going to simulate powerful layer 2 attack that target network switches: mac flooding (mac table overflow) — where an attacker uses tools like macof to flood the switch.
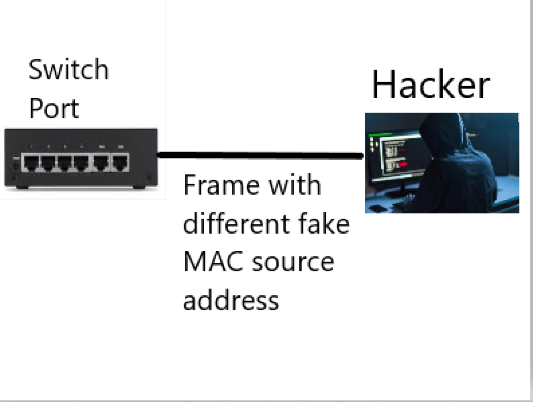
Github Utshaw Mac Table Flooding Attack Of The Switch In this tutorial, we looked over how a switched lan network works, and we saw how a mac flooding and a mac spoofing attack works. we discussed what the attacker could achieve and how network administrators can mitigate these attacks. After launching the macof tool, you can see, quite literally, a flood of ipv4 packets; this is our mac flood attack. in this lab, we won’t be going any further, but rest assured that we will utilize various techniques in order to “sniff” traffic in a network. This lab demonstrates how to perform a **mac flooding attack** using the macof tool from the dsniff collection. mac flooding is a technique used by attackers to compromise the security of network switches by forcing them into a "fail open" state, enabling traffic sniffing. In a typical mac flooding attack, a switch is fed many ethernet frames, each containing a different source mac address, by the attacker. the intention is to consume the limited memory set aside in the switch to store the mac address table.

Mac Flooding Attack This lab demonstrates how to perform a **mac flooding attack** using the macof tool from the dsniff collection. mac flooding is a technique used by attackers to compromise the security of network switches by forcing them into a "fail open" state, enabling traffic sniffing. In a typical mac flooding attack, a switch is fed many ethernet frames, each containing a different source mac address, by the attacker. the intention is to consume the limited memory set aside in the switch to store the mac address table. A hands on lab demonstrating mac flooding attacks to saturate switch cam tables and implementing mitigation solutions using port security. Learn what a mac flooding attack is, how attackers overwhelm network switches, and practical steps to detect and prevent this layer 2 threat. In this insider‘s guide, we‘re going to pull back the curtain on an attack vector that turns fundamental network infrastructure against itself. i‘ll explain how mac flooding works, its damaging repercussions, and – most importantly – how we can actually prevent it through some key best practices. Farhan tanvir utshaw website: utshaw linkedin: utshaw github: github utshaw.
Mac Flooding Attack A hands on lab demonstrating mac flooding attacks to saturate switch cam tables and implementing mitigation solutions using port security. Learn what a mac flooding attack is, how attackers overwhelm network switches, and practical steps to detect and prevent this layer 2 threat. In this insider‘s guide, we‘re going to pull back the curtain on an attack vector that turns fundamental network infrastructure against itself. i‘ll explain how mac flooding works, its damaging repercussions, and – most importantly – how we can actually prevent it through some key best practices. Farhan tanvir utshaw website: utshaw linkedin: utshaw github: github utshaw.
Comments are closed.