Mac Spoofing Attacks Explained A Technical Overview Securew2

Mac Spoofing Explained A Guide To Network Security Basics Learn how a mac spoofing attack works and allows unauthorized access to hackers by mimicking trusted devices. learn how you can prevent it. In layman’s terms, mac spoofing is when someone or something intercepts, manipulate or otherwise tampers with the control messages exchanged between a networked device and its unique mac address.

Mac Spoofing And Ip Spoofing Explained Mac Ip Spoofing Doovi Hackers can imitate another device’s mac address, allowing them to get through mac filtering or other mac based access control methods. Learn how mac spoofing compromises wi fi security, its risks, detection methods, and how securew2 prevents attacks with certificates. Once the switch’s mac learning capacity is exhausted, it may enter fail open mode, broadcasting traffic to all ports (like a hub), allowing the attacker to capture sensitive data. Learn what a mac spoofing attack is, how attackers fake hardware addresses to bypass network controls, detection, and how to prevent it.

How Do Mac Spoofing Attacks Work Once the switch’s mac learning capacity is exhausted, it may enter fail open mode, broadcasting traffic to all ports (like a hub), allowing the attacker to capture sensitive data. Learn what a mac spoofing attack is, how attackers fake hardware addresses to bypass network controls, detection, and how to prevent it. Among the various techniques used to breach network security, mac spoofing stands out due to its simplicity and effectiveness. this article provides an in depth exploration of mac spoofing, covering its definition, methods, applications, detection, and preventive measures. Learn what mac address spoofing (also called mac address cloning) is, why it’s used, and when it’s helpful. explore real world examples, risks, and differences from imei spoofing. includes step by step instructions for peplink, teltonika, and sierra wireless routers. This study addresses the critical cybersecurity challenges faced by small and mediumsized businesses (smbs) in protecting their local area networks (lans) against evolving mac address spoofing. The “hunting infostealers” blog series covers the ever evolving threat of infostealers. infostealers have gone from simple credential theft to.
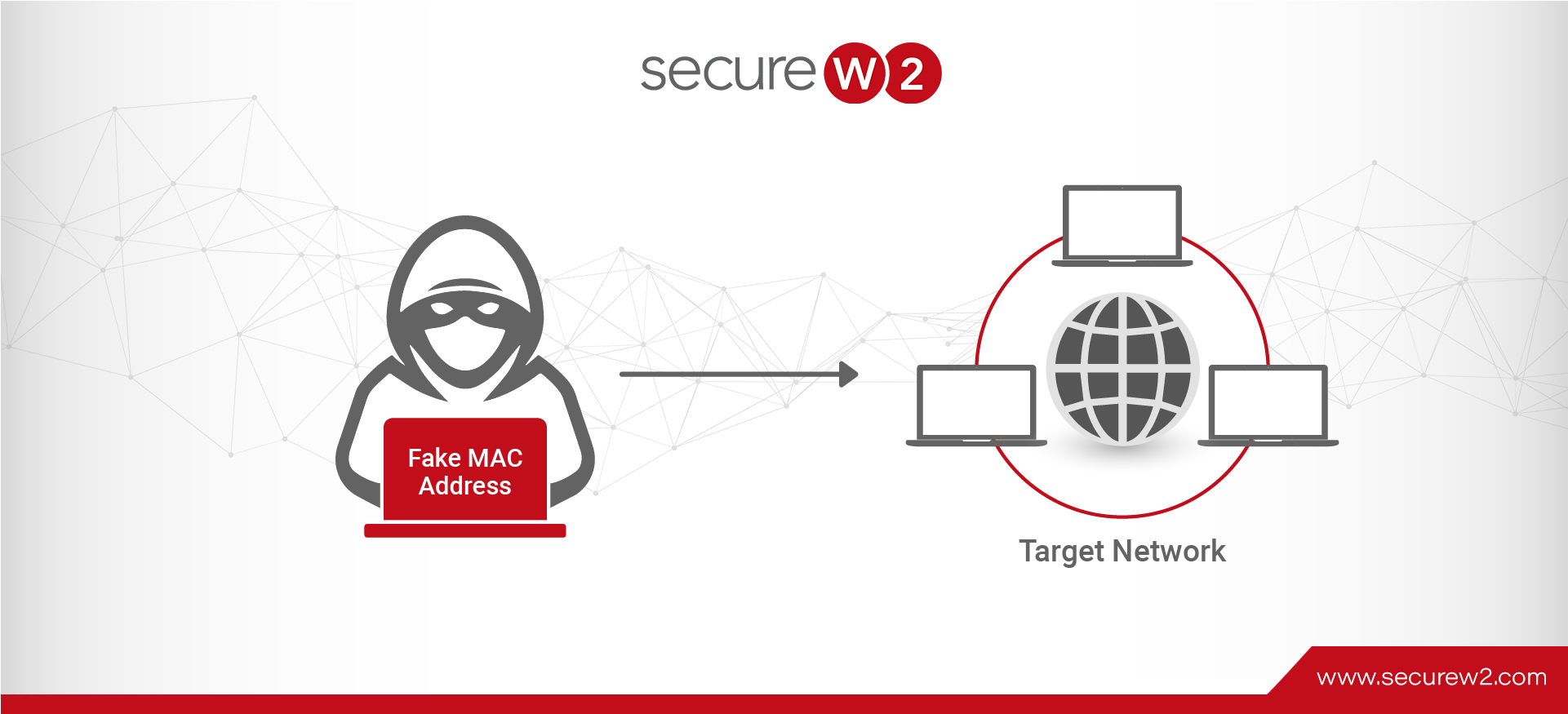
Mac Spoofing Attacks Explained A Technical Overview Among the various techniques used to breach network security, mac spoofing stands out due to its simplicity and effectiveness. this article provides an in depth exploration of mac spoofing, covering its definition, methods, applications, detection, and preventive measures. Learn what mac address spoofing (also called mac address cloning) is, why it’s used, and when it’s helpful. explore real world examples, risks, and differences from imei spoofing. includes step by step instructions for peplink, teltonika, and sierra wireless routers. This study addresses the critical cybersecurity challenges faced by small and mediumsized businesses (smbs) in protecting their local area networks (lans) against evolving mac address spoofing. The “hunting infostealers” blog series covers the ever evolving threat of infostealers. infostealers have gone from simple credential theft to.
Mac Spoofing Attacks Explained A Technical Overview This study addresses the critical cybersecurity challenges faced by small and mediumsized businesses (smbs) in protecting their local area networks (lans) against evolving mac address spoofing. The “hunting infostealers” blog series covers the ever evolving threat of infostealers. infostealers have gone from simple credential theft to.
Comments are closed.