Mac Spoofing Attacks Explained A Technical Overview

How Do Mac Spoofing Attacks Work Learn how a mac spoofing attack works and allows unauthorized access to hackers by mimicking trusted devices. learn how you can prevent it. Mac spoofing is a technique that can be used to fool the operating system into believing it has received an arp request from another machine. this allows the attacker to gain access to a victim's network without being detected.
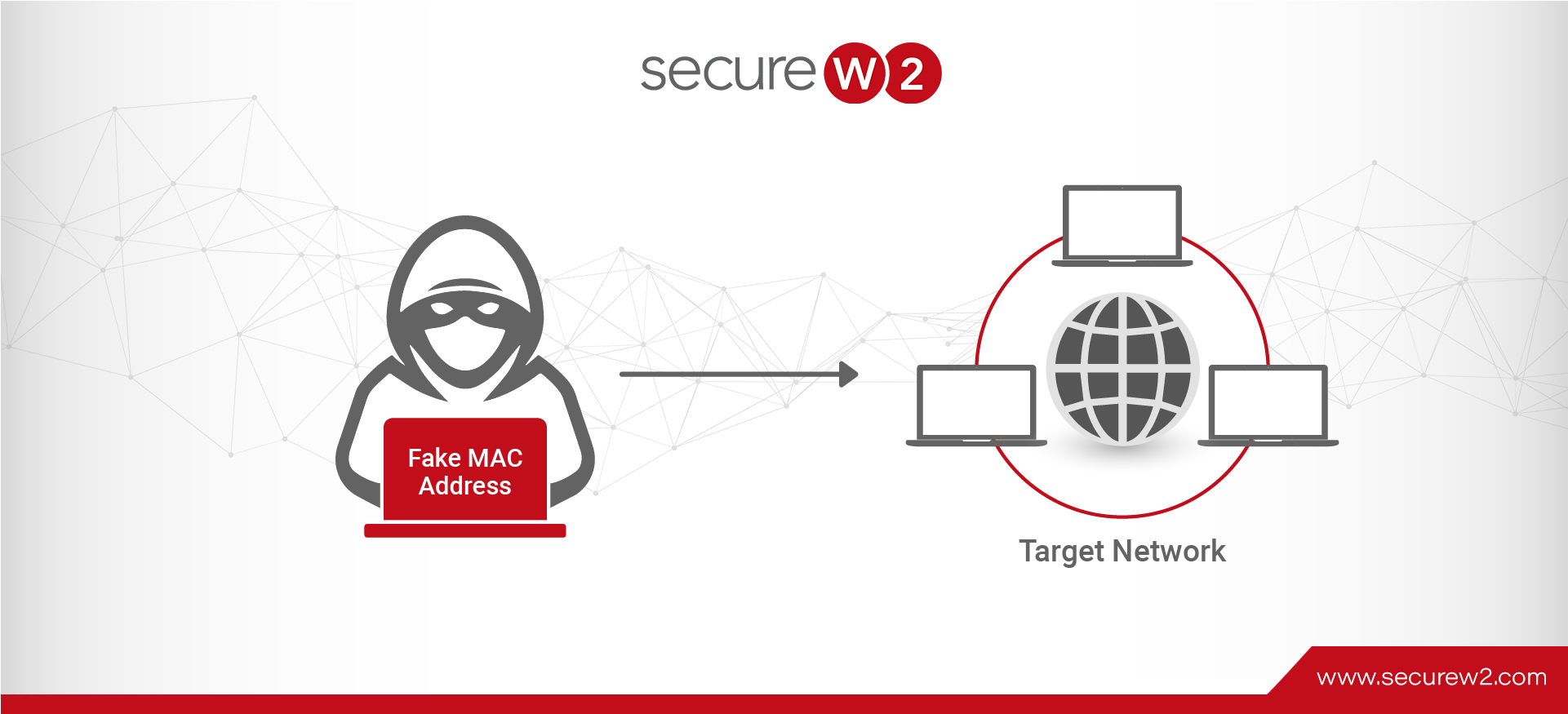
Mac Spoofing Attacks Explained A Technical Overview Learn what mac spoofing is, how attackers use it, and how to prevent it. this 2025 guide covers detection tools, real world risks, and expert prevention techniques for businesses and individuals. Among the various techniques used to breach network security, mac spoofing stands out due to its simplicity and effectiveness. this article provides an in depth exploration of mac spoofing, covering its definition, methods, applications, detection, and preventive measures. Mac spoofing is a technique where an attacker alters the media access control (mac) address of their device to mimic another device on the network. this deceptive practice is often used to bypass network security measures that rely on mac addresses for authentication and access control. Learn what mac spoofing is, how attackers fake device identities, risks to networks, detection methods, and best ways to prevent mac address spoofing.

Mac Spoofing Attacks Explained A Technical Overview Mac spoofing is a technique where an attacker alters the media access control (mac) address of their device to mimic another device on the network. this deceptive practice is often used to bypass network security measures that rely on mac addresses for authentication and access control. Learn what mac spoofing is, how attackers fake device identities, risks to networks, detection methods, and best ways to prevent mac address spoofing. Discover how hackers use mac spoofing to bypass security and learn simple, effective ways to protect your network from these hidden threats. A mac spoofing attack is when a hacker changes the mac address of their device to match the mac address of another on a network in order to gain unauthorized access or launch a man in the middle attack. Mac spoofing can be challenging to detect, but there are established methods to identify and prevent such attacks on your network. here's a practical guide on detecting and preventing mac spoofing. In this tutorial, we looked over how a switched lan network works, and we saw how a mac flooding and a mac spoofing attack works. we discussed what the attacker could achieve and how network administrators can mitigate these attacks.
Comments are closed.