Mac Address Flooding Definition Erorail

Mac Address Flooding Definition Erorail Mac flooding is a network attack in which a switch is intentionally overwhelmed with fake mac (media access control) addresses. this overload disrupts the switch’s ability to direct traffic properly, allowing attackers to intercept data or cause network failure. In a typical mac flooding attack, a switch is fed many ethernet frames, each containing a different source mac address, by the attacker. the intention is to consume the limited memory set aside in the switch to store the mac address table.
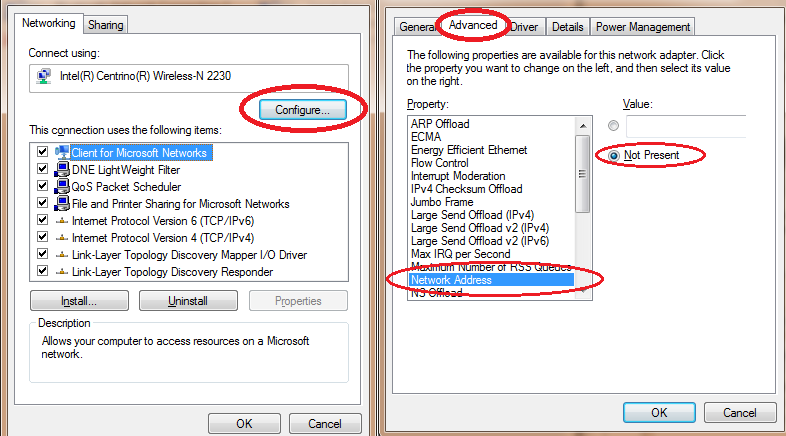
Mac Address Flooding Definition Erorail Mac flooding is a cyber attack targeting switches on a local area network (lan). it involves sending many packets with fake mac addresses to overflow the switch’s address table, causing it to become full and unable to process any legitimate traffic. A mac flooding attack is a network threat that targets the limited storage of a switch’s mac address table. the attacker sends a large number of packets with fake or random mac addresses, quickly filling up the table. A mac flooding attack targets ethernet networks and disrupts how a switch controls where traffic is sent between connected devices. it works by overwhelming the switch with a large number of mac addresses in a short period of time. A mac flooding attack, also known as a mac table overflow attack, is a type of network security attack that targets network switches. it involves overwhelming a switch’s mac address table by flooding it with a massive amount of spoofed ethernet frames, each containing a unique source mac address.
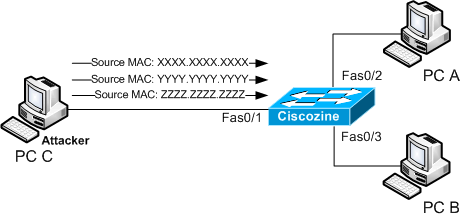
Mac Address Flooding Definition Hopdesc A mac flooding attack targets ethernet networks and disrupts how a switch controls where traffic is sent between connected devices. it works by overwhelming the switch with a large number of mac addresses in a short period of time. A mac flooding attack, also known as a mac table overflow attack, is a type of network security attack that targets network switches. it involves overwhelming a switch’s mac address table by flooding it with a massive amount of spoofed ethernet frames, each containing a unique source mac address. In a mac flooding attack, the attacker floods a network’s mac address table with fake data packets with different source mac addresses. the table automatically adds these new mac addresses to its table until it fills up and can no longer add new mac addresses. A mac flooding attack is a type of cyberattack in which attackers flood a network switch with data packets using fake mac addresses. they overwhelm the network switch capacity, which, when done, broadcasts incoming traffic to all the ports instead of the dedicated ones. A mac flooding attack (also known as a mac table overflow) involves bombarding network switches with ethernet frames carrying random source mac addresses. typically, network switches have limited memory resources and can’t handle such a large number of mac addresses. A flood of mac addresses is when an attacker sends out numerous packets that contain false information about the sender's hardware address. since the attacker is sending this information out, it prevents any other messages from being sent to that destination.

Mac Address Flooding Definition Lasopacuba In a mac flooding attack, the attacker floods a network’s mac address table with fake data packets with different source mac addresses. the table automatically adds these new mac addresses to its table until it fills up and can no longer add new mac addresses. A mac flooding attack is a type of cyberattack in which attackers flood a network switch with data packets using fake mac addresses. they overwhelm the network switch capacity, which, when done, broadcasts incoming traffic to all the ports instead of the dedicated ones. A mac flooding attack (also known as a mac table overflow) involves bombarding network switches with ethernet frames carrying random source mac addresses. typically, network switches have limited memory resources and can’t handle such a large number of mac addresses. A flood of mac addresses is when an attacker sends out numerous packets that contain false information about the sender's hardware address. since the attacker is sending this information out, it prevents any other messages from being sent to that destination.

Mac Flooding Pdf A mac flooding attack (also known as a mac table overflow) involves bombarding network switches with ethernet frames carrying random source mac addresses. typically, network switches have limited memory resources and can’t handle such a large number of mac addresses. A flood of mac addresses is when an attacker sends out numerous packets that contain false information about the sender's hardware address. since the attacker is sending this information out, it prevents any other messages from being sent to that destination.
Comments are closed.