Mac Address Flooding Attack And Mitigation Tutorial

4 1 42 Mac Flooding Attack Pdf In this tutorial, we looked over how a switched lan network works, and we saw how a mac flooding and a mac spoofing attack works. we discussed what the attacker could achieve and how network administrators can mitigate these attacks. Even though it may be an inconvenience to some, using the techniques discussed in this article will help prevent a flood of mac addresses from becoming a real problem for you.
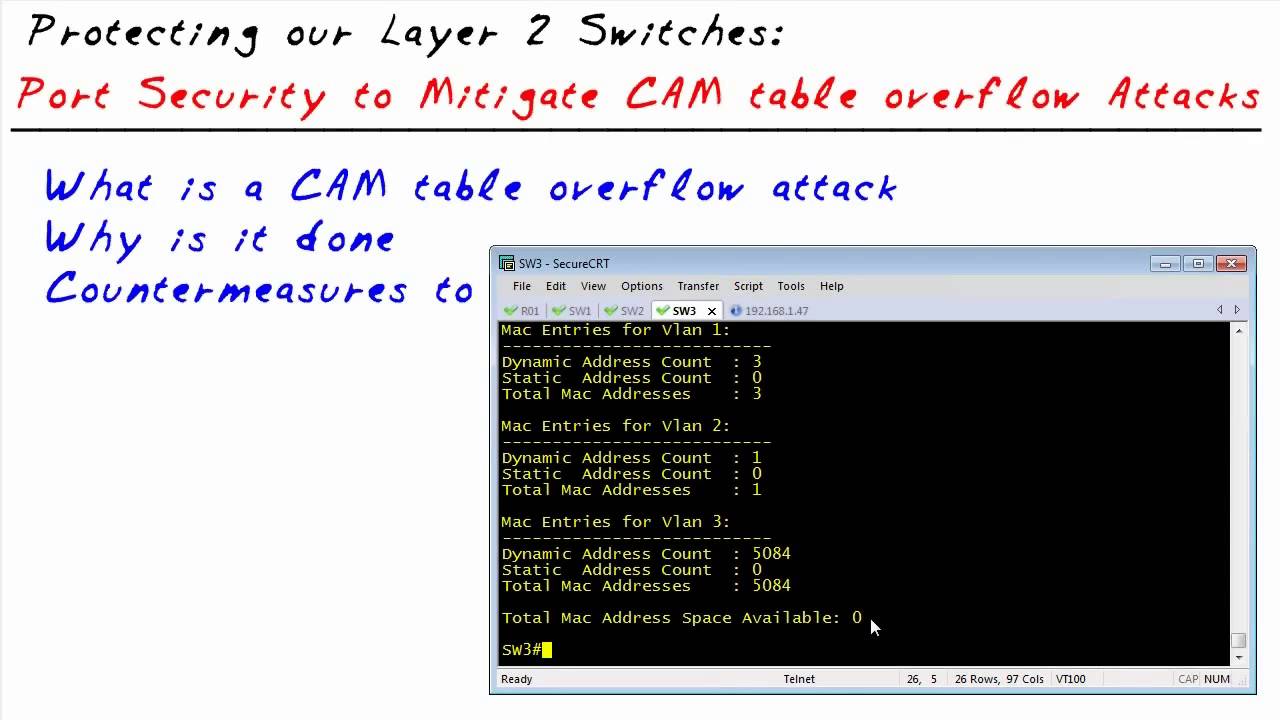
Mac Address Flooding Attack Tool Lasopaur A mac flooding attack can expose your data and compromise your network. in this article, we explain what mac flooding is and how you can prevent it. Mac flooding attacks exploit switch weaknesses to intercept traffic and cause network disruption. learn how they work and how to defend your network. It details the steps for executing the attack, observing the mac address table, and implementing security measures like restrict and protect modes to prevent unauthorized mac addresses. In this lab, we’re going to simulate powerful layer 2 attack that target network switches: mac flooding (mac table overflow) — where an attacker uses tools like macof to flood the switch.

Mac Address Flooding Attack Tool Lasopaline It details the steps for executing the attack, observing the mac address table, and implementing security measures like restrict and protect modes to prevent unauthorized mac addresses. In this lab, we’re going to simulate powerful layer 2 attack that target network switches: mac flooding (mac table overflow) — where an attacker uses tools like macof to flood the switch. Mac address flooding attack (cam table flooding attack) is a type of network attack where an attacker connected to a switch port floods the switch interface with very large number of ethernet frames with different fake source mac address. Learn what mac flooding is, how attackers exploit it to overwhelm network switches, and the steps you can take to detect and prevent this network security threat. This study aims to explore the effectiveness of port security mechanisms in mitigating mac flooding threats through a practical simulation using packet tracer. Mac flooding is another layer 2 attack that exploits the behavior of network switches. switches use mac address tables to determine the appropriate port to forward traffic. when a mac address isn’t in the table, the switch broadcasts the traffic to all ports, flooding the network.
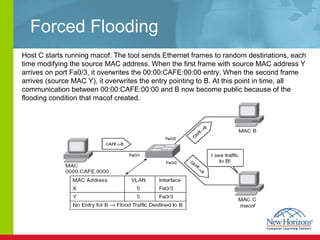
Mac Address Flooding Attack Tool Lasopaline Mac address flooding attack (cam table flooding attack) is a type of network attack where an attacker connected to a switch port floods the switch interface with very large number of ethernet frames with different fake source mac address. Learn what mac flooding is, how attackers exploit it to overwhelm network switches, and the steps you can take to detect and prevent this network security threat. This study aims to explore the effectiveness of port security mechanisms in mitigating mac flooding threats through a practical simulation using packet tracer. Mac flooding is another layer 2 attack that exploits the behavior of network switches. switches use mac address tables to determine the appropriate port to forward traffic. when a mac address isn’t in the table, the switch broadcasts the traffic to all ports, flooding the network.
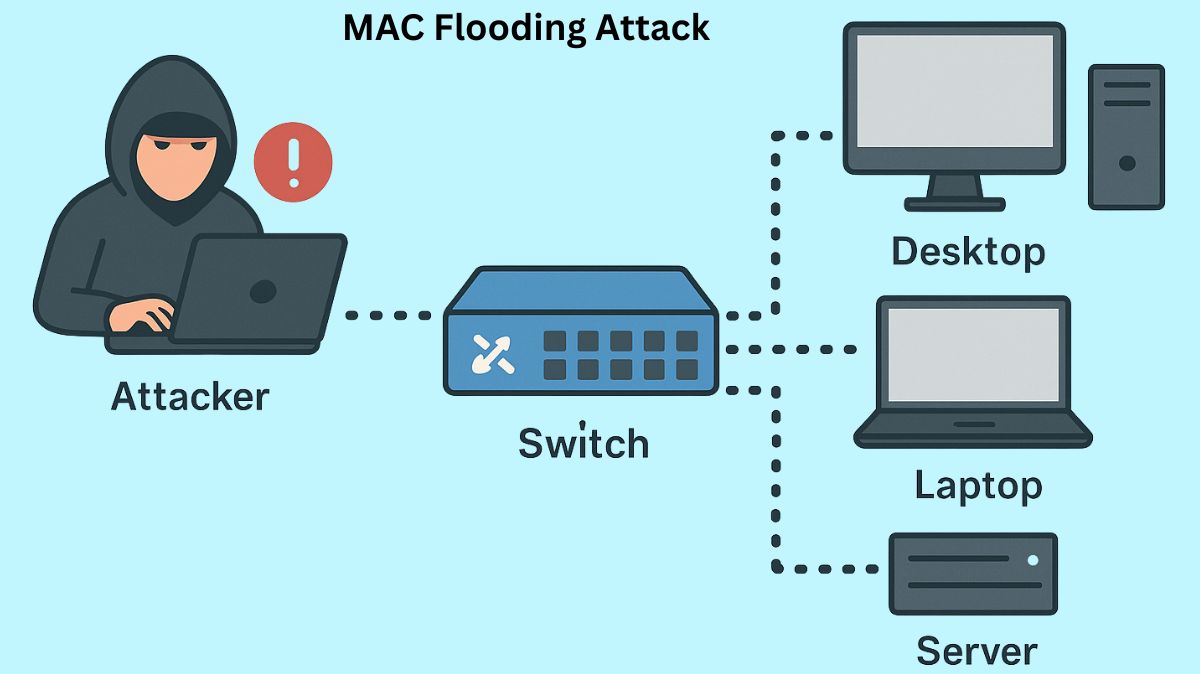
What Is Mac Flooding Attack And Prevention Techniques This study aims to explore the effectiveness of port security mechanisms in mitigating mac flooding threats through a practical simulation using packet tracer. Mac flooding is another layer 2 attack that exploits the behavior of network switches. switches use mac address tables to determine the appropriate port to forward traffic. when a mac address isn’t in the table, the switch broadcasts the traffic to all ports, flooding the network.
Mac Address Flooding Attack Tool Nanaxroom
Comments are closed.