Mac Address Flooding Attack
Mac Address Flooding Attack Tool Lasopaur In computer networking, a media access control attack or mac flooding is a technique employed to compromise the security of network switches. the attack works by forcing legitimate mac table contents out of the switch and forcing a unicast flooding behavior, potentially sending sensitive information to portions of the network where it is not. Mac flooding is a cyber attack targeting switches on a local area network (lan). it involves sending many packets with fake mac addresses to overflow the switch’s address table, causing it to become full and unable to process any legitimate traffic.

Mac Address Flooding Attack Tool Lasopaline A mac flooding attack can expose your data and compromise your network. in this article, we explain what mac flooding is and how you can prevent it. Mac flooding is a network attack in which a switch is intentionally overwhelmed with fake mac (media access control) addresses. this overload disrupts the switch’s ability to direct traffic properly, allowing attackers to intercept data or cause network failure. A flood of mac addresses is when an attacker sends out numerous packets that contain false information about the sender's hardware address. since the attacker is sending this information out, it prevents any other messages from being sent to that destination. A mac flooding attack targets ethernet networks and disrupts how a switch controls where traffic is sent between connected devices. it works by overwhelming the switch with a large number of mac addresses in a short period of time.
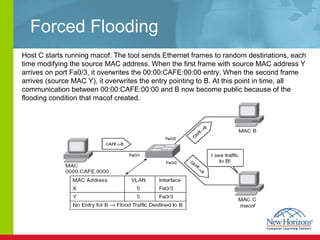
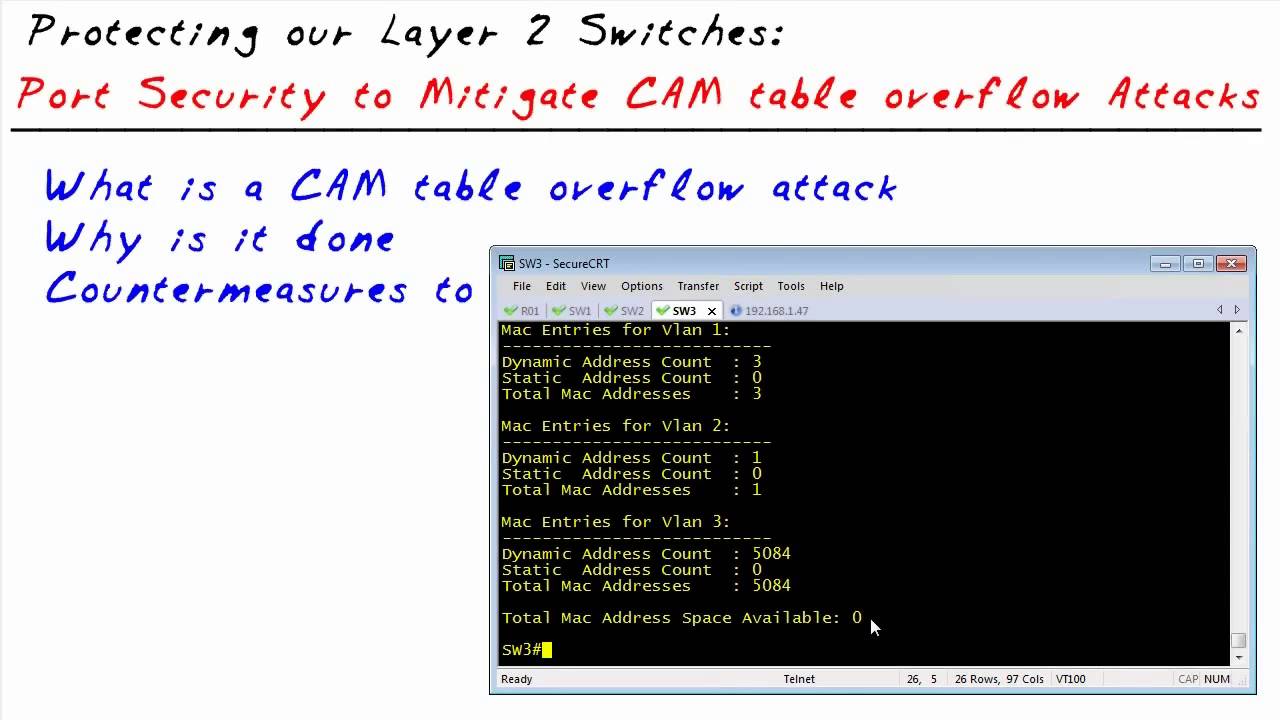
Mac Address Flooding Attack Tool Lasopaline A flood of mac addresses is when an attacker sends out numerous packets that contain false information about the sender's hardware address. since the attacker is sending this information out, it prevents any other messages from being sent to that destination. A mac flooding attack targets ethernet networks and disrupts how a switch controls where traffic is sent between connected devices. it works by overwhelming the switch with a large number of mac addresses in a short period of time. Learn how mac flooding attacks work, the risks they pose to networks, and simple steps to detect and prevent them. Mac flooding is another layer 2 attack that exploits the behavior of network switches. switches use mac address tables to determine the appropriate port to forward traffic. when a mac address isn’t in the table, the switch broadcasts the traffic to all ports, flooding the network. Mac flooding is an attack in which legal mac table contents are being replaced with the attacker’s desired ones by sending unicast flooding to network switches. Mac address flooding attack (cam table flooding attack) is a type of network attack where an attacker connected to a switch port floods the switch interface with very large number of ethernet frames with different fake source mac address.
Mac Address Flooding Attack Tool Nanaxroom Learn how mac flooding attacks work, the risks they pose to networks, and simple steps to detect and prevent them. Mac flooding is another layer 2 attack that exploits the behavior of network switches. switches use mac address tables to determine the appropriate port to forward traffic. when a mac address isn’t in the table, the switch broadcasts the traffic to all ports, flooding the network. Mac flooding is an attack in which legal mac table contents are being replaced with the attacker’s desired ones by sending unicast flooding to network switches. Mac address flooding attack (cam table flooding attack) is a type of network attack where an attacker connected to a switch port floods the switch interface with very large number of ethernet frames with different fake source mac address.
Mac Address Flooding Attack Tool Lasopaline Mac flooding is an attack in which legal mac table contents are being replaced with the attacker’s desired ones by sending unicast flooding to network switches. Mac address flooding attack (cam table flooding attack) is a type of network attack where an attacker connected to a switch port floods the switch interface with very large number of ethernet frames with different fake source mac address.
Comments are closed.