Logical Entities For 5g Network Access Security
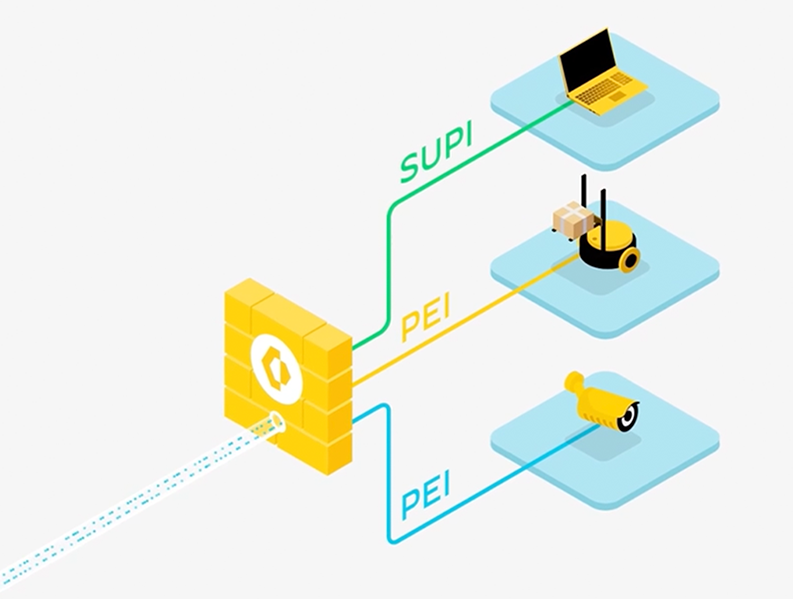
5g Security Palo Alto Networks Understand 5g security architecture, including authentication, network entities, virtualization, and monitoring for secure telecom networks. The present document specifies the security architecture, i.e., the security features and the security mechanisms for the 5g system and the 5g core, and the security procedures performed within the 5g system including the 5g core and the 5g new radio.

5g Security Palo Alto Networks The 5g core network is like the control center of the whole 5g system. it connects users safely and reliably to the internet and manages many important tasks like handling mobile connections, keeping track of user information, checking permissions, and applying network rules. Logical entities for 5g network access security dr. moazzam tiwana 9.85k subscribers subscribed. 5g core network functions support mutually authenticated tls (transport layer security) and https (hypertext transport protocol secure). this takes place by client server certificates protecting control plane signaling. To achieve high security and availability, 5g shall support isolation between network slices by using physical or logical isolation methods. 5g can ensure end to end isolation in ran, bearer network, and core network, as the following figure shows.
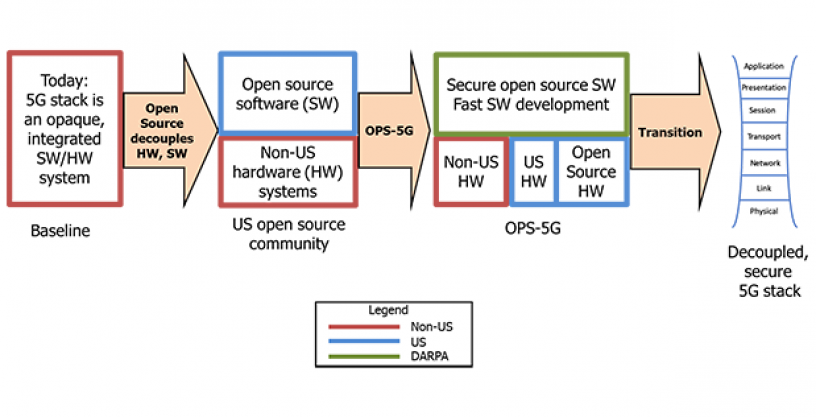
Improving 5g Network Security 5g core network functions support mutually authenticated tls (transport layer security) and https (hypertext transport protocol secure). this takes place by client server certificates protecting control plane signaling. To achieve high security and availability, 5g shall support isolation between network slices by using physical or logical isolation methods. 5g can ensure end to end isolation in ran, bearer network, and core network, as the following figure shows. Network operators can use common network technologies to logically separate the 5g data plane, signaling, and o&m trafic from each other. doing so can improve cybersecurity and privacy in multiple ways, including the following:. To achieve such versatility, 5g services are offered as logically isolated end to end fragments known as network slices. this approach enables 5g operators to create independent network instances that can be tailored for different sets of requirements. We prefer to analyze carefully selected papers considered significant and produce from them an overview of the status of the security of the network technologies used by 5g. Schematically, the 5g system uses the same elements as the previous generations: a user equipment (ue), itself composed of a mobile station and a usim, the radio access network (ng ran) and the core network (5gc), as shown in the figure below.
Security Threats In 5g Network Download Scientific Diagram Network operators can use common network technologies to logically separate the 5g data plane, signaling, and o&m trafic from each other. doing so can improve cybersecurity and privacy in multiple ways, including the following:. To achieve such versatility, 5g services are offered as logically isolated end to end fragments known as network slices. this approach enables 5g operators to create independent network instances that can be tailored for different sets of requirements. We prefer to analyze carefully selected papers considered significant and produce from them an overview of the status of the security of the network technologies used by 5g. Schematically, the 5g system uses the same elements as the previous generations: a user equipment (ue), itself composed of a mobile station and a usim, the radio access network (ng ran) and the core network (5gc), as shown in the figure below.
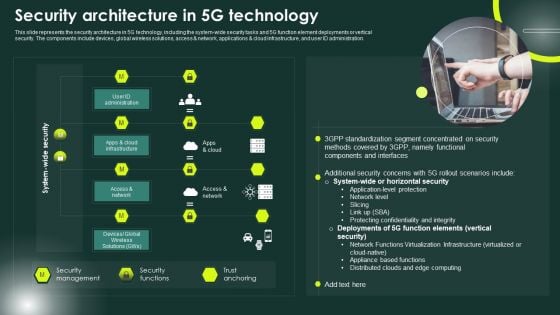
5g Network Security Powerpoint Templates Slides And Graphics We prefer to analyze carefully selected papers considered significant and produce from them an overview of the status of the security of the network technologies used by 5g. Schematically, the 5g system uses the same elements as the previous generations: a user equipment (ue), itself composed of a mobile station and a usim, the radio access network (ng ran) and the core network (5gc), as shown in the figure below.

Entities Of Secondary Authentication In 5g S Security Architecture
Comments are closed.