Logical Components Of Zero Trust Architecture Zero Trust Network Security P

Zero Trust Network Access Logical Components Of Zero Trust Architecture Zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. traditional security works like a castle with walls. once you're inside, you can access everything. Zero trust architecture (zta) is a security framework that operates on the principle of “never trust, always verify.” it eliminates implicit trust in users, devices, and networks, even if they are already inside the corporate network.

Logical Components Of Zero Trust Architecture Zero Trust Network Security P This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. Zero trust architecture in system design explores a security model focused on the principle of 'never trust, always verify.' this approach assumes that threats could exist both inside and outside the network, so it requires rigorous verification for every user and device trying to access resources. Achieving zero trust security requires a combination of two key elements: zero trust network access (ztna), which delivers zero trust from the outside, and microsegmentation, which achieves zero trust from the inside – for example, between machines within your network. A zero trust architecture is not a single technology but a cohesive framework built on multiple interconnected security components. the core of its functionality lies in a comprehensive approach to identity, device, and network security.

Zero Trust Network Access External Components Of Zero Trust Network Achieving zero trust security requires a combination of two key elements: zero trust network access (ztna), which delivers zero trust from the outside, and microsegmentation, which achieves zero trust from the inside – for example, between machines within your network. A zero trust architecture is not a single technology but a cohesive framework built on multiple interconnected security components. the core of its functionality lies in a comprehensive approach to identity, device, and network security. The nist sp 800 207 describes the logical components that make up a zero trust architecture deployment in an enterprise, which are displayed in the figure below. This architecture guide is focused on the cisco zero trust framework with the user and device security, network and cloud security, and application and data security pillars. In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy. The architecture relies on identity security, endpoint security, application security, data security, and continuous monitoring. it enforces three key principles: never trust, always verify; assume breach; and apply least privileged access.
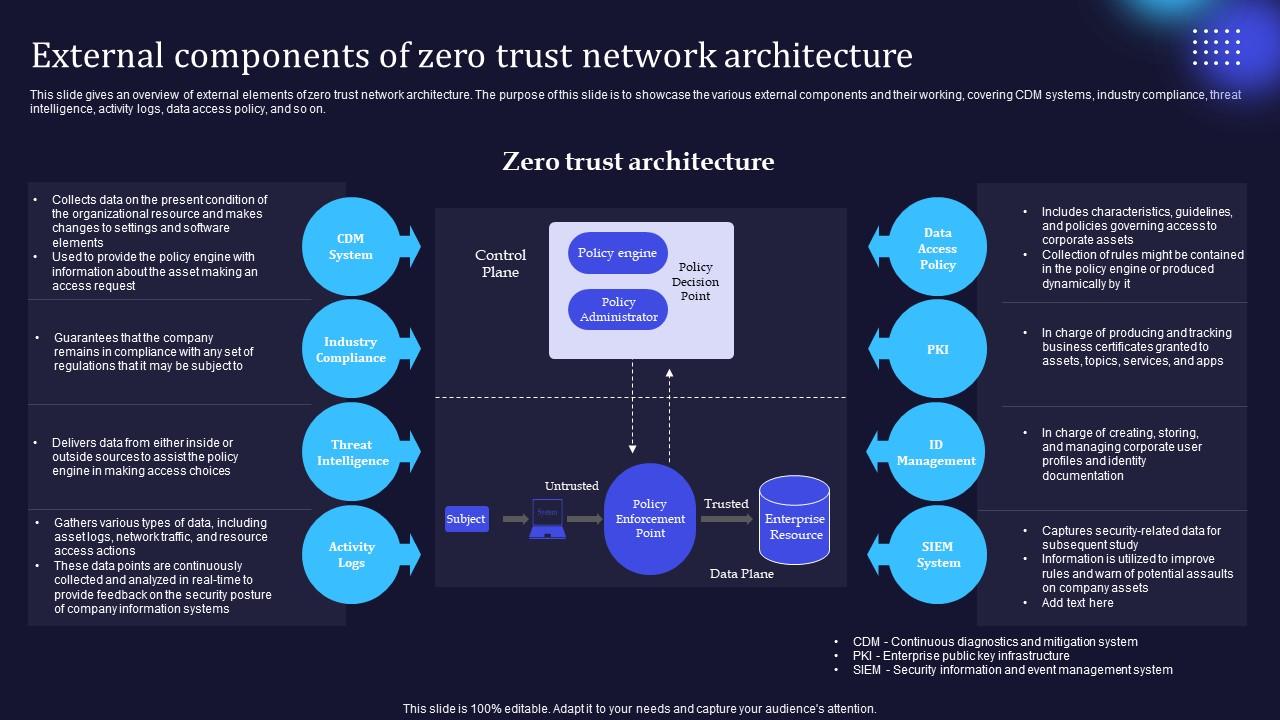
Zero Trust Model External Components Of Zero Trust Network Architecture The nist sp 800 207 describes the logical components that make up a zero trust architecture deployment in an enterprise, which are displayed in the figure below. This architecture guide is focused on the cisco zero trust framework with the user and device security, network and cloud security, and application and data security pillars. In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy. The architecture relies on identity security, endpoint security, application security, data security, and continuous monitoring. it enforces three key principles: never trust, always verify; assume breach; and apply least privileged access.
Comments are closed.