Logical Attacks Physical Attacks
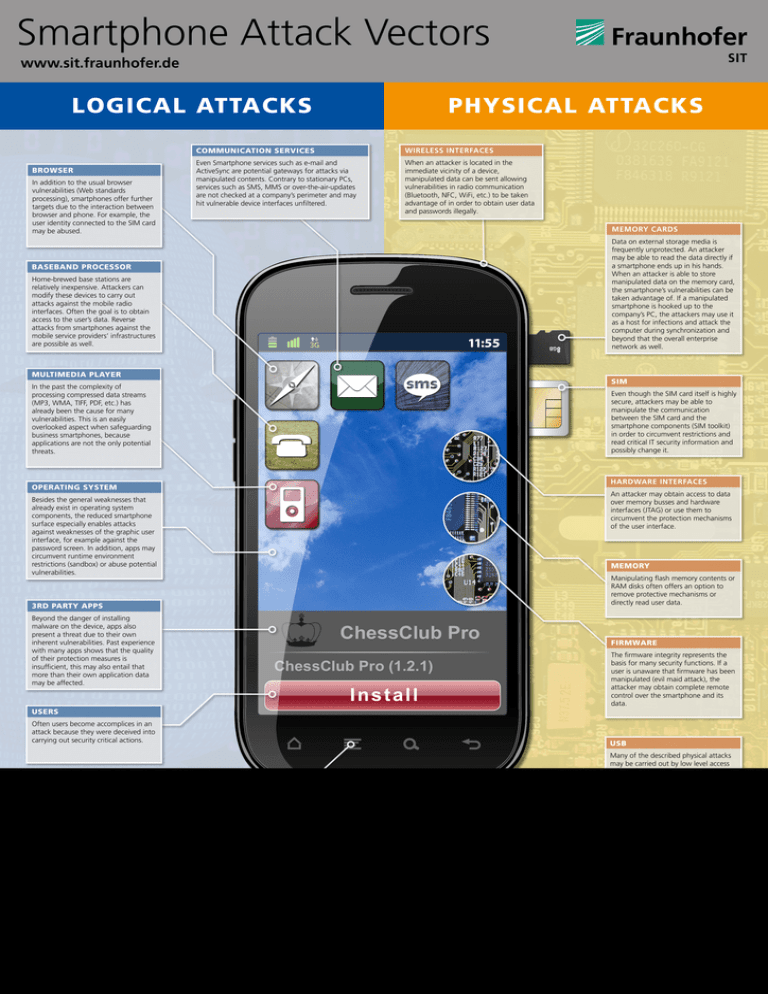
Logical Attacks Physical Attacks Conversely, we can attack logical systems to cover for a physical attack. if we can compromise the security system that receives alerts from the physical intrusion detection system, we can cause not only a distraction but a complete lack of confidence in the functionality of the system. Nxp has also developed resistance against logical attacks, which exploit logical errors, software bugs and flaws in decision‑making processes. logical attacks and physical attacks can be combined to downscale attacks in overall complexity, while still fully automated and deployed remotely.
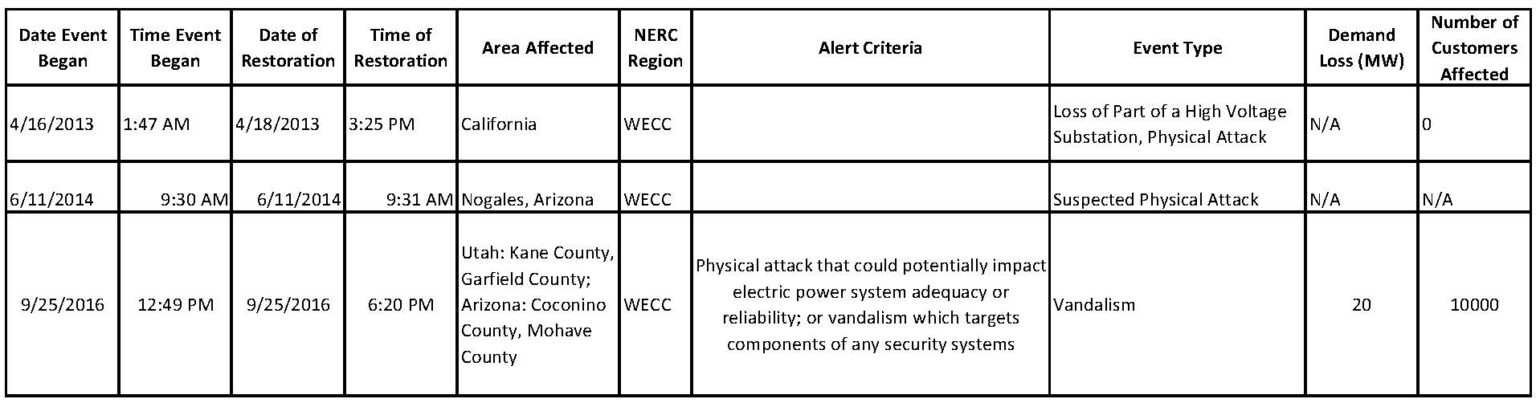
Physical Attacks Secure The Grid Abstract: an overview is given of attacks on hardware security by introducing the four attack classes: logical attacks, physical observative attacks, physical fault injection attacks, and physical manipulative attacks. descriptions and examples are given for each class of attack. To counter obfuscation, a number of logical (e.g. boolean satisfiability) and physical (e.g. electro optical probing) attacks have been proposed. by definition, these attacks use only a subset of the information leaked by a circuit to unlock it. This code base contains code for the physical portion of the clap attack aimed at guiding an eofm probe to extract key leakage from a die. it can be run entirely in simulation. Logical vs physical logical attacks: use the card as it is using the ‘normal’ functionality, but in unexpected ways, or exploiting bugs physical attacks: attack the underlying hardware incl. side channel attacks these can be passive or active, with different levels of invasiveness.
Logical Attacks Ppt This code base contains code for the physical portion of the clap attack aimed at guiding an eofm probe to extract key leakage from a die. it can be run entirely in simulation. Logical vs physical logical attacks: use the card as it is using the ‘normal’ functionality, but in unexpected ways, or exploiting bugs physical attacks: attack the underlying hardware incl. side channel attacks these can be passive or active, with different levels of invasiveness. In this article, we’ll be talking about some types of attacks that bypass electronic security measures, and how physical access can compromise computers and networks. Physical security has conventionally been about access control, guards and cameras, while logical security was about cyber security techs sequestered in darkened rooms responding to. In practice, a common approach to characterise physical and cyber attacks is lacking, which may cause security gaps. this article proposes a set of technical criteria to characterise attacks. it evaluates these criteria based on attack scenarios to assess their efficacy. Physical attacks are of relevance if an adversary gains physical access to the cryptographic device or its near by environment, e.g., a smart card. there are two different objectives which have to be regarded in order to counter physical attacks.
Physical Attacks Cypherock In this article, we’ll be talking about some types of attacks that bypass electronic security measures, and how physical access can compromise computers and networks. Physical security has conventionally been about access control, guards and cameras, while logical security was about cyber security techs sequestered in darkened rooms responding to. In practice, a common approach to characterise physical and cyber attacks is lacking, which may cause security gaps. this article proposes a set of technical criteria to characterise attacks. it evaluates these criteria based on attack scenarios to assess their efficacy. Physical attacks are of relevance if an adversary gains physical access to the cryptographic device or its near by environment, e.g., a smart card. there are two different objectives which have to be regarded in order to counter physical attacks.
Logical Attacks Pdf In practice, a common approach to characterise physical and cyber attacks is lacking, which may cause security gaps. this article proposes a set of technical criteria to characterise attacks. it evaluates these criteria based on attack scenarios to assess their efficacy. Physical attacks are of relevance if an adversary gains physical access to the cryptographic device or its near by environment, e.g., a smart card. there are two different objectives which have to be regarded in order to counter physical attacks.

Logical Attacks Pdf
Comments are closed.