Live Data Acquisition Using Ftk Imager

Access Data Ftk Imager Pdf Using ftk imager portable version in a usb pen drive or hdd and opening it directly from the evidence machine. this option is most frequently used in live data acquisition where the evidence pc laptop is switched on. Live data acquisition using ftk imager computing for all 7.92k subscribers subscribe.
Evidence Acquisition Using Accessdata Ftk Imager Forensic Focus This document outlines practical exercises for a cyber forensics course, including creating forensic images using ftk imager, data acquisition with usb write blockers, and analyzing data with autopsy and wireshark. There are many tools for capturing data from memory, but one company, access data, has been providing their ftk (forensic tool kit) imager for years for free and, as a result, it has become the de facto standard in image capturing. Ftk imager is a popular tool used by professionals to acquire digital evidence. in this guide we will be using ftk imager tool to acquire a forensic image from a pc. With ftk imager, you can: create forensic images or perfect copies of local hard drives, floppy and zip disks, dvds, folders, individual files, etc. without making changes to the original evidence.
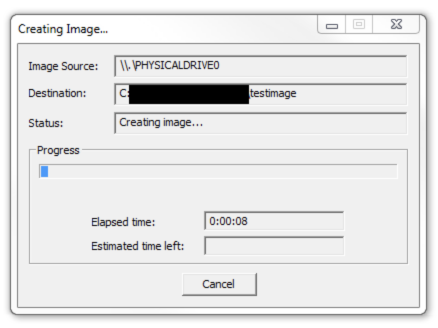
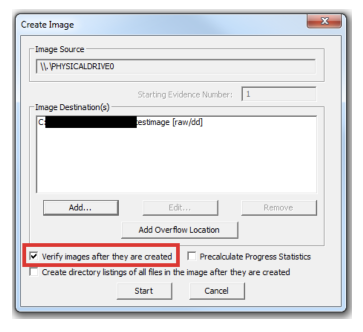
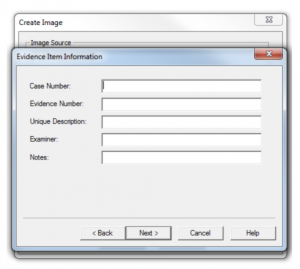
Evidence Acquisition Using Accessdata Ftk Imager Forensic Focus Ftk imager is a popular tool used by professionals to acquire digital evidence. in this guide we will be using ftk imager tool to acquire a forensic image from a pc. With ftk imager, you can: create forensic images or perfect copies of local hard drives, floppy and zip disks, dvds, folders, individual files, etc. without making changes to the original evidence. By following this procedure, a forensic examiner can successfully acquire and preserve a forensic image of digital media using ftk imager, ensuring that the evidence is accurate, reliable, and legally admissible. Perform memory capture or registry capture on a live device to recover passwords or other data stored in memory on the active device. write and read the most common forensic image formats, making it easy to continue your forensic analysis and review ftk forensic toolkit. The rest of this article will walk the reader through the process of taking a drive image using accessdata's ftk imager tool. ftk imager is a windows acquisition tool included in various forensics toolkits, such as helix and the sans sift workstation. Ftk imager, made by exterro, is a forensic imaging tool. you install it on a windows machine, point it at a drive or at live memory, and it creates an exact bit for bit duplicate of whatever you’re targeting.
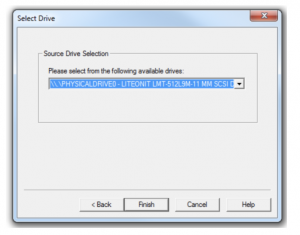
Evidence Acquisition Using Accessdata Ftk Imager Forensic Focus By following this procedure, a forensic examiner can successfully acquire and preserve a forensic image of digital media using ftk imager, ensuring that the evidence is accurate, reliable, and legally admissible. Perform memory capture or registry capture on a live device to recover passwords or other data stored in memory on the active device. write and read the most common forensic image formats, making it easy to continue your forensic analysis and review ftk forensic toolkit. The rest of this article will walk the reader through the process of taking a drive image using accessdata's ftk imager tool. ftk imager is a windows acquisition tool included in various forensics toolkits, such as helix and the sans sift workstation. Ftk imager, made by exterro, is a forensic imaging tool. you install it on a windows machine, point it at a drive or at live memory, and it creates an exact bit for bit duplicate of whatever you’re targeting.

Evidence Acquisition Using Accessdata Ftk Imager Forensic Focus The rest of this article will walk the reader through the process of taking a drive image using accessdata's ftk imager tool. ftk imager is a windows acquisition tool included in various forensics toolkits, such as helix and the sans sift workstation. Ftk imager, made by exterro, is a forensic imaging tool. you install it on a windows machine, point it at a drive or at live memory, and it creates an exact bit for bit duplicate of whatever you’re targeting.
Evidence Acquisition Using Accessdata Ftk Imager Forensic Focus
Comments are closed.