Linux System Call Monitoring Black Hills Information Security Inc
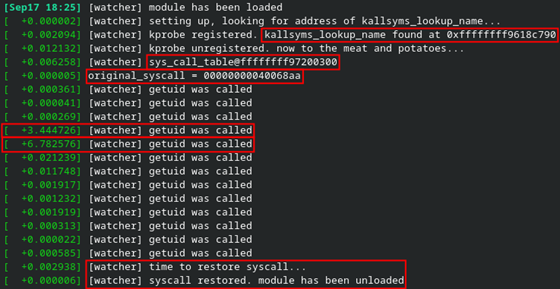
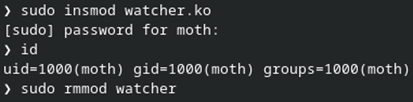
Black Hills Information Security Youtube What i’ve ended up with is a piece of code that i can extend to monitor arbitrary syscalls, as well as a mechanism to investigate linux kernel security. some initial research led me to a kernel tracing facility called kprobes, which can be used to hook most kernel symbols. Bhis | tester's blog linux system call monitoring by: moth published: 9 13 2022 lnkd.in e4jkfk6u.

Black Hills Information Security On Linkedin Linux System Call These are a collection of security and monitoring scripts you can use to monitor your linux installation for security related events or for an investigation. each script works on its own and is independent of other scripts. Learn effective monitoring and alerting strategies for linux to ensure system reliability and proactive issue detection. Collecting and analyzing system call data helps security teams identify patterns of suspicious behavior and investigate potential security incidents on time. the linux audit system is a powerful tool for collecting security and non security events on linux endpoints. Learn how to monitor linux servers effectively using command line tools, key performance metrics, and expert sysadmin strategies to boost performance and security.

Black Hills Information Security The Org Collecting and analyzing system call data helps security teams identify patterns of suspicious behavior and investigate potential security incidents on time. the linux audit system is a powerful tool for collecting security and non security events on linux endpoints. Learn how to monitor linux servers effectively using command line tools, key performance metrics, and expert sysadmin strategies to boost performance and security. This article serves as a comprehensive guide on monitoring system logs for security events, and you can get training on our insights as you delve deeper into this critical aspect of linux security. Security is not an attainable static state, but rather a dynamic practice – constant diligence is required. an organization’s security should be reviewed and updated on a regular basis. this can be as simple as running a periodic vulnerability assessment, or as in depth as a penetration test. Monitoring user activity in remote ssh and local linux sessions can help your organization enhance visibility in your it infrastructure, promptly detect and respond to security threats, and meet certain it compliance requirements. This blog explores the fundamentals of realtime linux security monitoring, key tools, implementation workflows, and best practices to help you build a resilient defense.
Linux System Call Monitoring Black Hills Information Security Inc This article serves as a comprehensive guide on monitoring system logs for security events, and you can get training on our insights as you delve deeper into this critical aspect of linux security. Security is not an attainable static state, but rather a dynamic practice – constant diligence is required. an organization’s security should be reviewed and updated on a regular basis. this can be as simple as running a periodic vulnerability assessment, or as in depth as a penetration test. Monitoring user activity in remote ssh and local linux sessions can help your organization enhance visibility in your it infrastructure, promptly detect and respond to security threats, and meet certain it compliance requirements. This blog explores the fundamentals of realtime linux security monitoring, key tools, implementation workflows, and best practices to help you build a resilient defense.
Linux System Call Monitoring Black Hills Information Security Inc Monitoring user activity in remote ssh and local linux sessions can help your organization enhance visibility in your it infrastructure, promptly detect and respond to security threats, and meet certain it compliance requirements. This blog explores the fundamentals of realtime linux security monitoring, key tools, implementation workflows, and best practices to help you build a resilient defense.

Black Hills Information Security Top 10 Cybersecurity Consulting
Comments are closed.