Linux Privilege Escalation Using Kernel Exploit
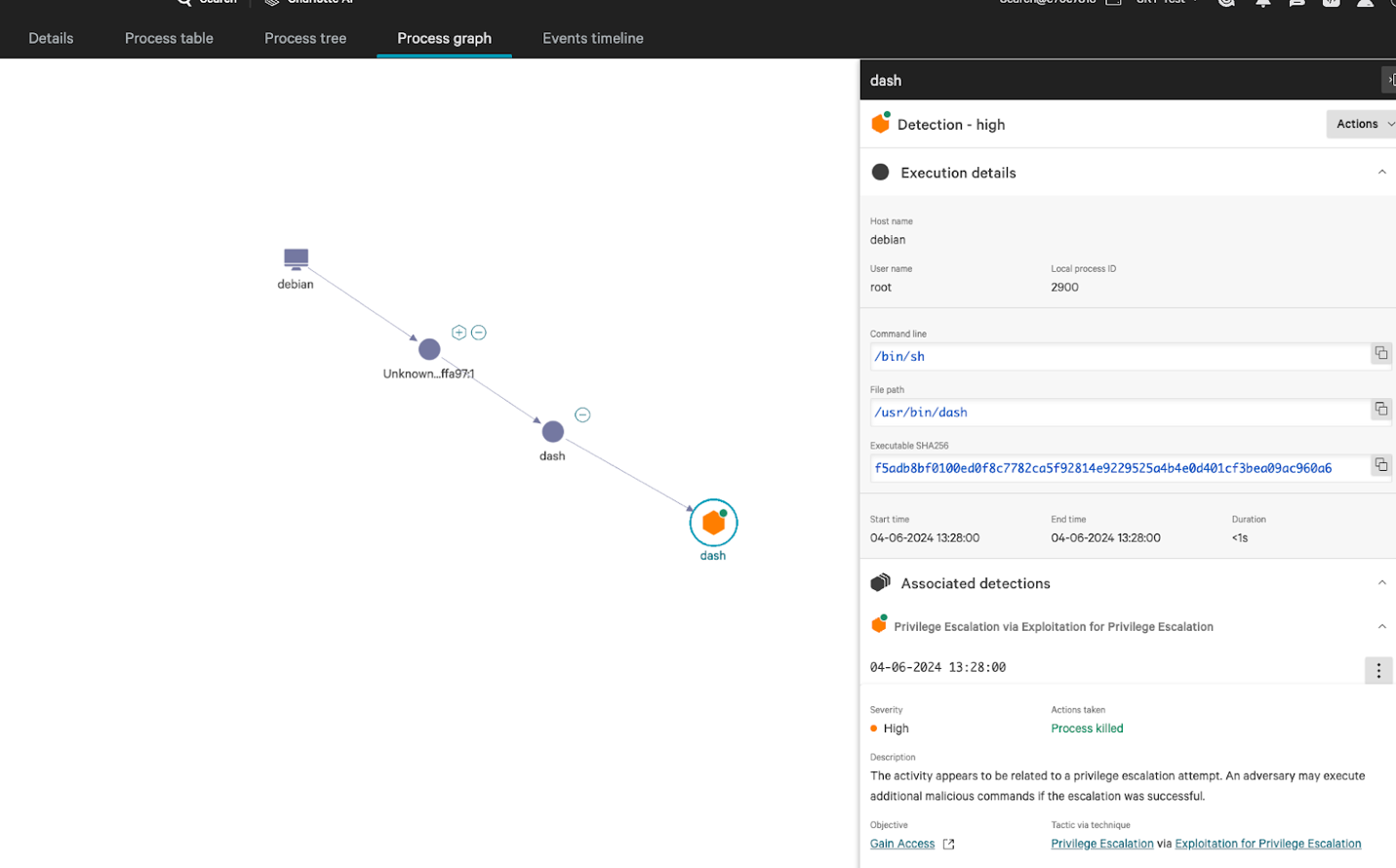
Active Exploitation Observed For Linux Kernel Privilege Escalation We have walked you through various linux privilege escalation techniques such as kernel and service exploits, understanding suid, managing scheduled tasks, and navigating password discovery. This tryhackme room covers privilege escalation techniques on linux systems. in this activity, we focus on exploiting a kernel vulnerability to gain root access.

How To Conduct Linux Privilege Escalations Techtarget Gtfoargs: argument injection exploitation vector list | gtfoargs is a curated list of unix binaries whose arguments can be exploited for argument injection, enabling shell escapes, privilege escalation, file read write, and other post exploitation techniques. Linux security & privilege escalation relevant source files this section documents the methodologies, vectors, and technical implementations for assessing linux security and achieving privilege escalation. it covers system enumeration, kernel exploitation, service specific vulnerabilities (grafana, logstash, ipsec), and post exploitation. The room provides a deep dive into eight core privilege escalation techniques, while also covering essential linux fundamentals that support the enumeration and exploitation process. Then we can look for an exploit for this kernel through exploit database for example. now we can either download the file from here or locate it on our machine through the file name.
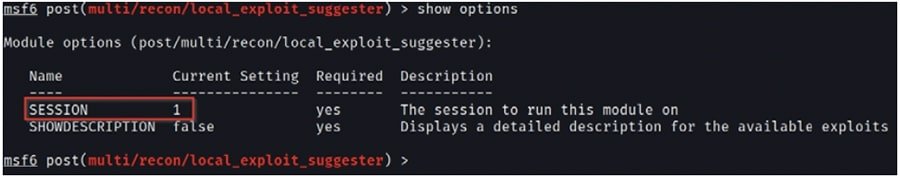
How To Conduct Linux Privilege Escalations Techtarget The room provides a deep dive into eight core privilege escalation techniques, while also covering essential linux fundamentals that support the enumeration and exploitation process. Then we can look for an exploit for this kernel through exploit database for example. now we can either download the file from here or locate it on our machine through the file name. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host. By understanding common techniques—such as kernel exploits, misconfigured services, suid misuse, sudo misconfigurations, and cron job vulnerabilities—you can better secure systems against these threats. Privilege escalation is the process of exploiting a system’s weaknesses to increase access privileges. attackers use this to transition from a low privileged user to root access, enabling them to modify critical files, extract sensitive data, and maintain persistence. This blog will delve into the fundamental concepts of linux privilege escalation, explore common usage methods, discuss typical practices, and provide best practices to mitigate the risks.
Comments are closed.