Linux Privilege Escalation For Beginners
Reddit Comments On Linux Privilege Escalation For Beginners Udemy Linux privilege escalation for beginners the cyber mentor 983k subscribers subscribed. When conducting a penetration test, gaining initial access to a linux machine is only half the job. the real objective is privilege escalation. in real world engagements, attackers rarely.
Linux Privilege Escalation For Beginners Hackercool Magazine Learn about various linux privilege escalation techniques in our blogpost made for absolute beginners. learn all techniques. An icon used to represent a menu that can be toggled by interacting with this icon. 1 1. introduction 08:00. 2 2. course tips & resources 05:48. 3 1. capabilities overview 03:36. 4 2. escalation via capabilities 02:44. 5 1. cron jobs & systemd timers overview 04:59. 6 2. escalation via cron paths 02:53. 7 3. escalation via cron wildcards 05:25. This repository contains my beginner friendly walkthrough of linux privilege escalation techniques using a virtual lab setup. i explored how to escalate from a normal user to root by exploiting misconfigurations like suid binaries, sudo permissions, and writable system files. Let’s take a look at what linux privilege escalation is, how it works, and how you can prevent it from happening professionally!.
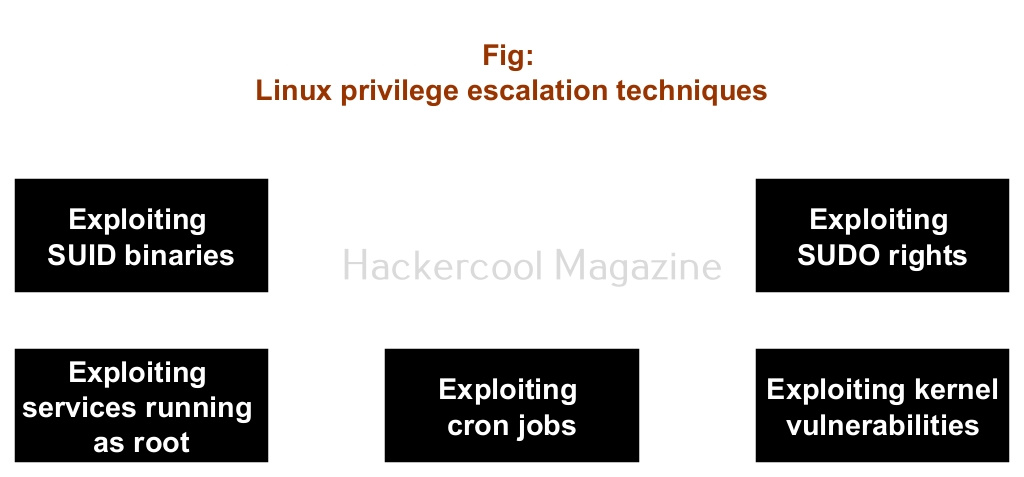
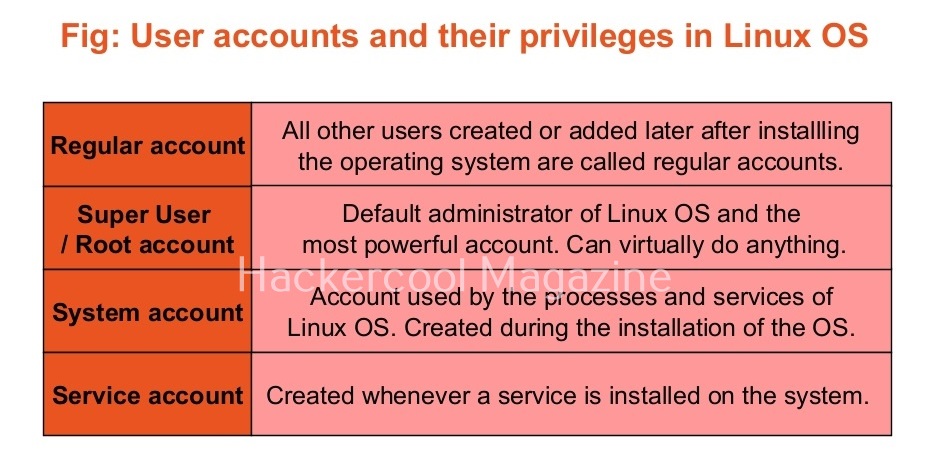
Linux Privilege Escalation For Beginners Hackercool Magazine This repository contains my beginner friendly walkthrough of linux privilege escalation techniques using a virtual lab setup. i explored how to escalate from a normal user to root by exploiting misconfigurations like suid binaries, sudo permissions, and writable system files. Let’s take a look at what linux privilege escalation is, how it works, and how you can prevent it from happening professionally!. On linux systems, privilege escalation is a technique by which an attacker gains initial access to a limited or full interactive shell of a basic user or system account with limited privileges. Linux privilege escalation is a complex but important topic in system security. by understanding the fundamental concepts, usage methods, common practices, and best practices, users can better protect their linux systems from unauthorized access and privilege escalation attacks. By the end of this course, you'll have a solid understanding of linux system enumeration, privilege escalation techniques, and kernel exploits. you'll be equipped to handle real world scenarios effectively. It is not a cheat sheet for enumeration using linux commands, instead the blog is particularly aimed at helping beginners understand the fundamentals of linux privilege escalation with examples.

Github Sujayadkesar Linux Privilege Escalation All Linux Privilege On linux systems, privilege escalation is a technique by which an attacker gains initial access to a limited or full interactive shell of a basic user or system account with limited privileges. Linux privilege escalation is a complex but important topic in system security. by understanding the fundamental concepts, usage methods, common practices, and best practices, users can better protect their linux systems from unauthorized access and privilege escalation attacks. By the end of this course, you'll have a solid understanding of linux system enumeration, privilege escalation techniques, and kernel exploits. you'll be equipped to handle real world scenarios effectively. It is not a cheat sheet for enumeration using linux commands, instead the blog is particularly aimed at helping beginners understand the fundamentals of linux privilege escalation with examples.
Comments are closed.