Linux Privilege Escalation Exploit Suid Files And Become Root

ёэрдёэрлёэрлёэриёэроёэру Linux Privilege Escalation Exploit Misconfigurations Elevate We will show you how to use both manual techniques and automated tools to detect potential privilege escalation methods. whether through kernel exploits, service exploits, cron jobs, or sudo permissions, we will show you examples of how to gain root access via one of many methods. In this post, i’ll walk through suid privilege escalation, a common technique in linux environments where misconfigured binaries can allow regular users to escalate to root.

ёэрдёэрлёэрлёэриёэроёэру Linux Privilege Escalation Exploit Misconfigurations Elevate In this lab, you will learn about the suid (set user id upon execution) permission and how to leverage it for privilege escalation on linux systems. the goal is to gain root access by exploiting suid binaries with various techniques, including using bash, find, cp, and mv commands. Learn how you can find and exploit unusual suid binaries to perform horizontal and then vertical privilege escalation to get a privileged shell and read the files. Learn how misconfigured suid binaries can give instant root access on linux. step by step guide with gtfobins exploitation examples included. Linux privilege escalation is one of the most critical skills in penetration testing — systematically identifying misconfigured binaries, writable files, and kernel vulnerabilities that allow you to move from a limited user to root. this guide covers the full methodology. run linpeas linenum.

Tryhackme Linux Privilege Escalation Suid Tryhackme Learn how misconfigured suid binaries can give instant root access on linux. step by step guide with gtfobins exploitation examples included. Linux privilege escalation is one of the most critical skills in penetration testing — systematically identifying misconfigured binaries, writable files, and kernel vulnerabilities that allow you to move from a limited user to root. this guide covers the full methodology. run linpeas linenum. Let’s break down the nitty gritty of advanced linux privilege escalation, from classic suid exploits to the modern world of linux capabilities. step by step, with hands on code and real world pentesting flavor. If a file with this bit is ran, the uid will be changed by the owner one. if the file owner is root, the uid will be changed to root even if it was executed from user bob. Privilege escalation is a critical phase in penetration testing and ethical hacking, where an attacker seeks to gain higher level permissions on a system. understanding these techniques not only helps in securing systems but also in identifying potential vulnerabilities during security assessments. In this instance, we use ‘stdbuf’ to run ‘cat’ with unbuffered input, attempting to display the contents of the flag file with the suid bit set, and accessing a file owned by root.
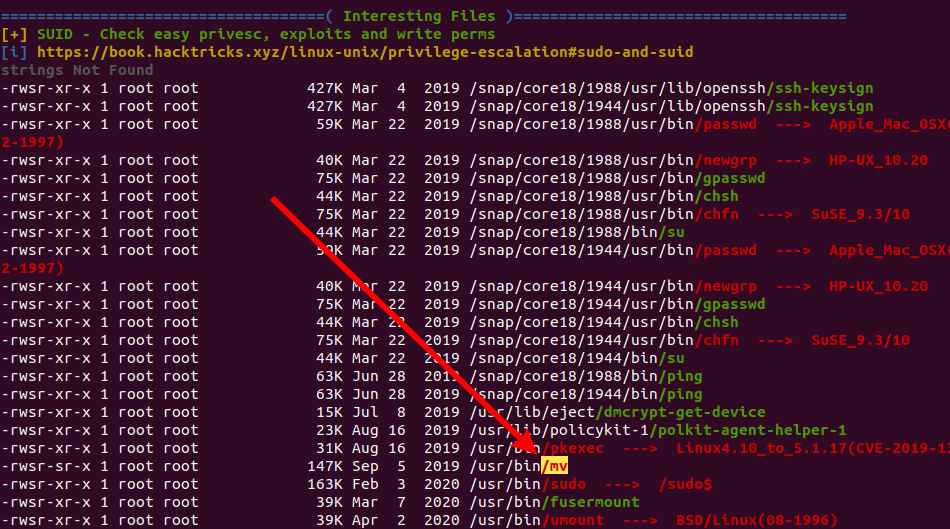
Linux Privilege Escalation Suid Binaries Steflan S Security Blog Let’s break down the nitty gritty of advanced linux privilege escalation, from classic suid exploits to the modern world of linux capabilities. step by step, with hands on code and real world pentesting flavor. If a file with this bit is ran, the uid will be changed by the owner one. if the file owner is root, the uid will be changed to root even if it was executed from user bob. Privilege escalation is a critical phase in penetration testing and ethical hacking, where an attacker seeks to gain higher level permissions on a system. understanding these techniques not only helps in securing systems but also in identifying potential vulnerabilities during security assessments. In this instance, we use ‘stdbuf’ to run ‘cat’ with unbuffered input, attempting to display the contents of the flag file with the suid bit set, and accessing a file owned by root.

Linux Privilege Escalation Suid Binaries Steflan S Security Blog Privilege escalation is a critical phase in penetration testing and ethical hacking, where an attacker seeks to gain higher level permissions on a system. understanding these techniques not only helps in securing systems but also in identifying potential vulnerabilities during security assessments. In this instance, we use ‘stdbuf’ to run ‘cat’ with unbuffered input, attempting to display the contents of the flag file with the suid bit set, and accessing a file owned by root.
Comments are closed.