Linux Immutable Malware Process Binary Attack
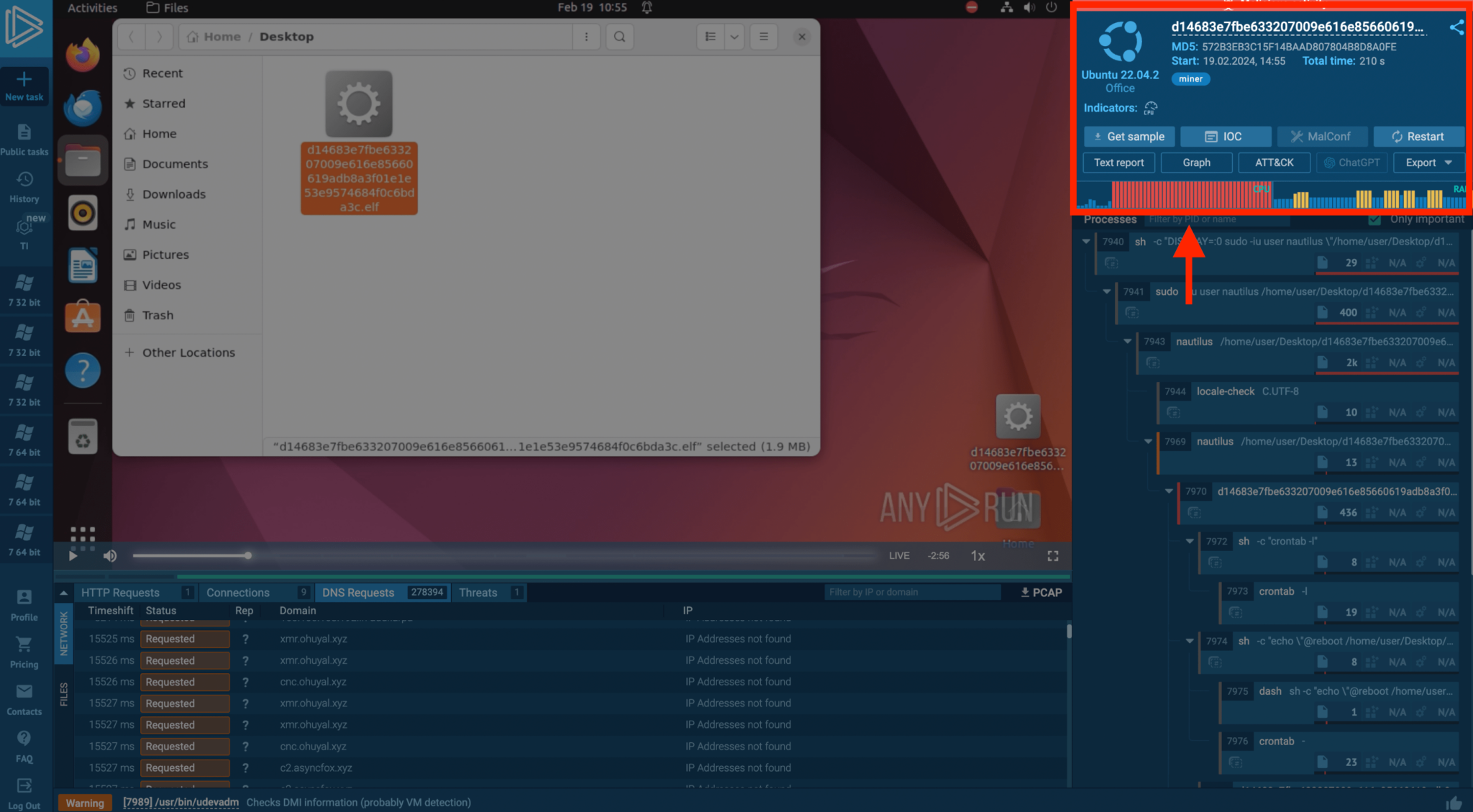
Analyzing Linux Malware In Any Run 3 Examples Any Run S Processes running with an immutable binary are nearly always malware on linux. learn what this attack is, how to automatically detect it, and command line forensics you can use to investigate suspicious processes using this attack tactic. Processes running with an immutable binary are nearly always malware on linux. learn what this attack is, how to automatically detect it, and command line forensics you can use to investigate….
How To Basic Linux Malware Process Forensics For Incident Responders This bash script detects files with immutable attributes on linux systems for persistence detection and rootkit discovery, identifying malware protected with chattr i flags that prevent removal even by root users or security tools. Immutable process binaries on linux are a near certain sign of malware. discover this attack technique and learn how to detect it using command line forensics. In practice, the immutable bit is more commonly used for critical configuration files or important system binaries that administrators want to protect from accidental or malicious changes. Videos education linux forensicsdatejanuary 06, 2025authorthe sandfly security teamprocesses running.

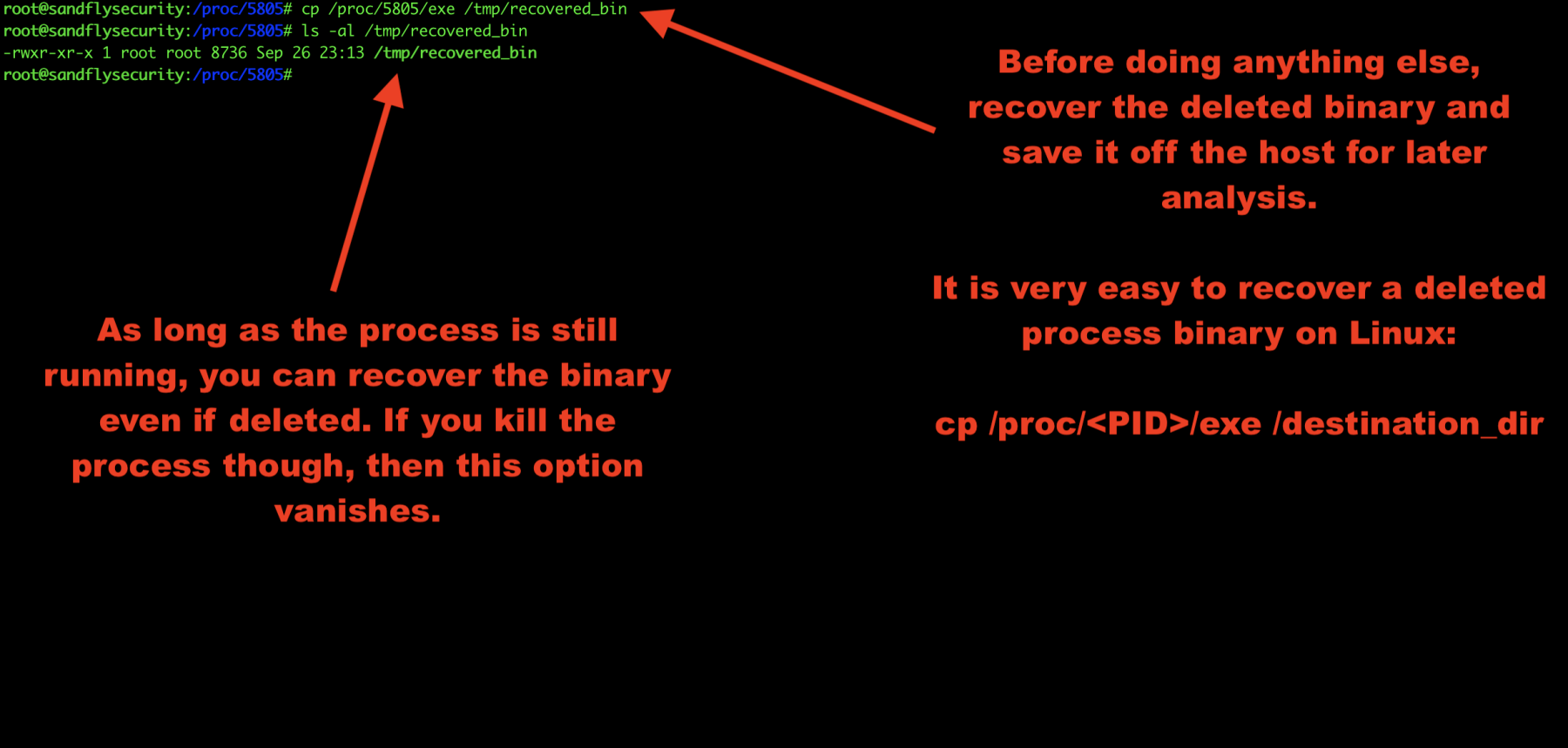
How To Basic Linux Malware Process Forensics For Incident Responders In practice, the immutable bit is more commonly used for critical configuration files or important system binaries that administrators want to protect from accidental or malicious changes. Videos education linux forensicsdatejanuary 06, 2025authorthe sandfly security teamprocesses running. So it's pretty clear that we are taking a look at a linux binary. why is it interesting? what i usually find in my honeypot are irc based miners, scripts for initial deployment and some keys, but this is slightly different. i took a very quick look at the strings, and realized it used golang. The detection rule identifies unusual movements or copies of these binaries, excluding common system processes and paths, to flag potential malicious activity. this helps in identifying attempts at masquerading, a tactic used to bypass security measures. Linux malware often deletes its binary from the disk to evade detection and analysis. learn how to detect and respond to this attack in this video. Processes running with an immutable binary are nearly always malicious on linux. learn what this attack is, how to automatically detect it, and command line forensics you can use to.
Comments are closed.