Lecture 4 Pdf Cloud Computing Security

Cloud Computing Security I Lecture 9 Pdf Cloud security lecture 4 free download as pdf file (.pdf), text file (.txt) or read online for free. Google doc protection yber criminals, encryption consider the best strategy. this is particularly true for google docs in the online threats inste being on the desktop. there are plenty of ways to protect cloud documents such as:.

Cloud Security Chapter Pdf Software As A Service Cloud Computing Although virtualization and cloud computing can help companies accomplish more by breaking the physical bonds between an it infrastructure and its users, heightened security threats must be overcome in order to benefit fully from this new computing paradigm. Contribute to kmnaim aws academy cloud foundations development by creating an account on github. If business critical processes are migrated to a cloud computing model, internal security processes need to evolve to allow multiple cloud providers to participate in those processes, as needed. With the widespread adoption of cloud computing by businesses and organizations of all sizes, ensuring the security of cloud based resources has become a critical concern.
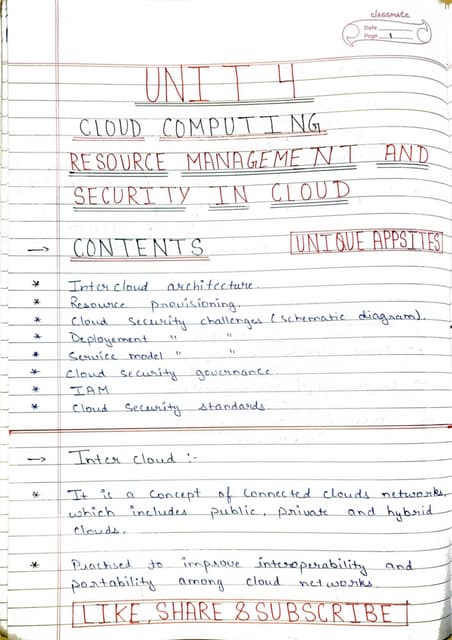
Unit 4 Cloud Computing Pdfunit 4 Cloud Computing Pdf If business critical processes are migrated to a cloud computing model, internal security processes need to evolve to allow multiple cloud providers to participate in those processes, as needed. With the widespread adoption of cloud computing by businesses and organizations of all sizes, ensuring the security of cloud based resources has become a critical concern. Trusted cloud computing, data privacy, and testing practices are crucial aspects of ensuring the security, confidentiality, and integrity of data and services in cloud environments. 4.1 software vulnerabilities the goal of this first phase of testing is to confirm the fact that the software running on each amis is often out of date and, therefore, must be immediately updated by the user. Lecture 4 cloud security free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. this document discusses security issues related to cloud computing. The document covers essential cloud security concepts including confidentiality, integrity, availability, privacy, authentication, non repudiation, access control, defense in depth, and the principle of least privilege.

Cloud Computing Security Pdf Trusted cloud computing, data privacy, and testing practices are crucial aspects of ensuring the security, confidentiality, and integrity of data and services in cloud environments. 4.1 software vulnerabilities the goal of this first phase of testing is to confirm the fact that the software running on each amis is often out of date and, therefore, must be immediately updated by the user. Lecture 4 cloud security free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. this document discusses security issues related to cloud computing. The document covers essential cloud security concepts including confidentiality, integrity, availability, privacy, authentication, non repudiation, access control, defense in depth, and the principle of least privilege.

Lecture 4 Cloud Security Download Free Pdf Cloud Computing Security Lecture 4 cloud security free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. this document discusses security issues related to cloud computing. The document covers essential cloud security concepts including confidentiality, integrity, availability, privacy, authentication, non repudiation, access control, defense in depth, and the principle of least privilege.

Cloud Security Pdf Cloud Computing Security Engineering
Comments are closed.