Lecture 3 Stream Ciphers Random Numbers And The One Time Pad By Christof Paar
Stream Ciphers Random Numbers And The One Time Pad Hunter Richardson Lecture 3: stream ciphers, random numbers and the one time pad by christof paar. interested in studying cybersecurity at the highest level? bochum offers one of the most. This is a series of lectures on cryptography that was taught in the 2010 2011 academic year at ruhr university bochum. the lectures give a fairly comprehensive introduction to modern applied cryptography.
Stream Ciphers Random Numbers And The One Time Pad Hunter Richardson Cryptographically secure pseudo random number generator requires unpredictable sequences satisfies the "next bit test“: given consecutive sequence of bits output (but not seed), next bit must be hard to predict. Paar proceeds to explore the relationship between stream ciphers and the shift cipher, emphasizing the modular operation that underpins both. An ordered list of profesor paar's lectures in cryptography, including primitives, protocols, and some attacks. Beschreibung the 27 lectures give a comprehensive introduction to modern applied crypto. only high school math is required to follow the course, as the audie.
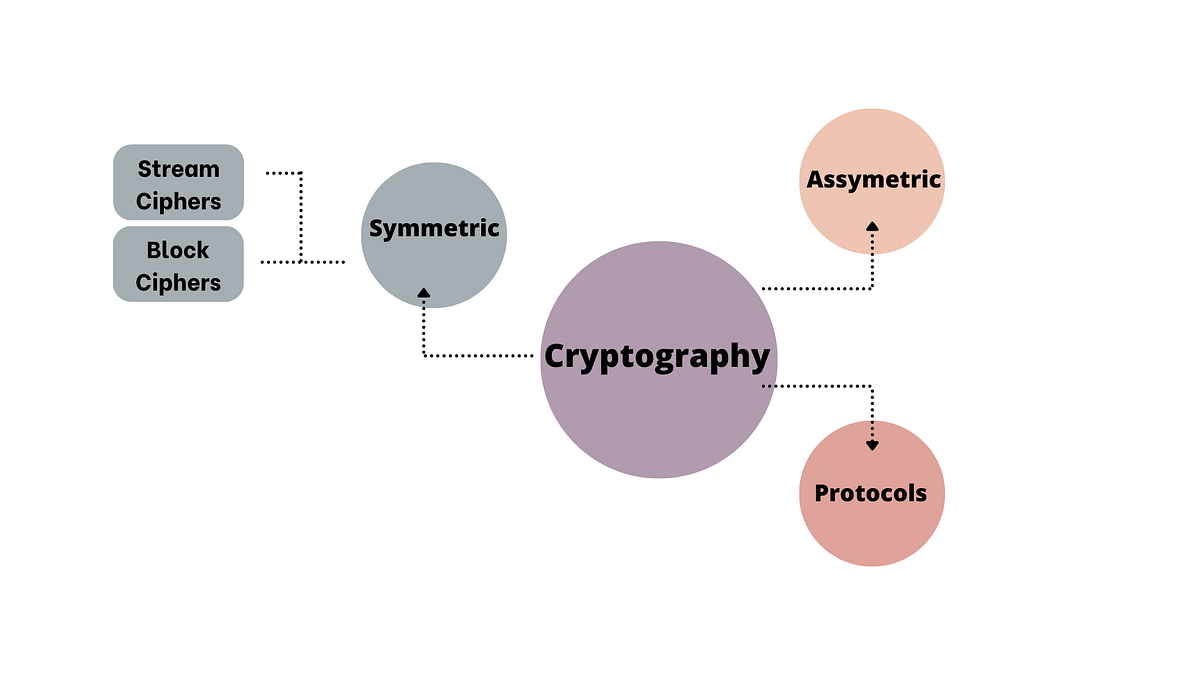
Stream Ciphers Rngs One Time Pad By Srupa Thota Medium An ordered list of profesor paar's lectures in cryptography, including primitives, protocols, and some attacks. Beschreibung the 27 lectures give a comprehensive introduction to modern applied crypto. only high school math is required to follow the course, as the audie. Lecture 3: stream ciphers, random numbers and the one time pad by christof paar 4. A university level introduction to cryptography by dr. christof paar. • we generate a pseudorandom “key stream” from a seed, a “real key” much shorter than the full “key stream” added to the message • we try to make the set of possible seeds, the real keys, so large that exhaustive search is impossible in practice • we try to eliminate any shortcuts to finding this key from the “key stream” additive stream ciphers. Lecture 3 cryptography: one time pad, information theoretical security, and stream ciphers cs426 fall 2010 lecture 3 given a ciphertext that is the xor of two english texts, how to break it? * fix any ciphertext, need at least one key for each plaintext message.
Understanding Stream Ciphers Random Numbers And The One Time Pad By Lecture 3: stream ciphers, random numbers and the one time pad by christof paar 4. A university level introduction to cryptography by dr. christof paar. • we generate a pseudorandom “key stream” from a seed, a “real key” much shorter than the full “key stream” added to the message • we try to make the set of possible seeds, the real keys, so large that exhaustive search is impossible in practice • we try to eliminate any shortcuts to finding this key from the “key stream” additive stream ciphers. Lecture 3 cryptography: one time pad, information theoretical security, and stream ciphers cs426 fall 2010 lecture 3 given a ciphertext that is the xor of two english texts, how to break it? * fix any ciphertext, need at least one key for each plaintext message.
Guarding Secrets Understanding Stream Ciphers Random Numbers And The • we generate a pseudorandom “key stream” from a seed, a “real key” much shorter than the full “key stream” added to the message • we try to make the set of possible seeds, the real keys, so large that exhaustive search is impossible in practice • we try to eliminate any shortcuts to finding this key from the “key stream” additive stream ciphers. Lecture 3 cryptography: one time pad, information theoretical security, and stream ciphers cs426 fall 2010 lecture 3 given a ciphertext that is the xor of two english texts, how to break it? * fix any ciphertext, need at least one key for each plaintext message.

Lecture 3 Stream Ciphers Random Numbers And The One Time Pad By
Comments are closed.