Lecture 19 Wsn Network Security Essentials Part 3

Wsn Lecture Notes Pdf Wireless Sensor Network Network Congestion Network security essentials 6th edition william stallings prof.mouhammd al kasassbeh · course. Network security essentials : applications and standards. introduction: computer security concepts pt. 1. crytography. symmetric encryption and message confidentiality public key cryptography and message authentication pt. 2. network security applications.
Cns Part3 Cryptography And Network Security Full Lecture Notes Part 3 3. network security essentials 4th edition william stallings.pdf google drive. loading…. Practical use of rsa: chapter 3 expands the discussion of rsa encryption and rsa digital signatures to show how padding and other techniques are used to provide prac tical security using rsa. Solutions manual for network security essentials: applications and standards, fifth edition. includes answers to review questions and homework problems. Task 3: a network — overview to understand network security, it is essential to comprehend what a network is, the components or assets that form it, and how these components work together.

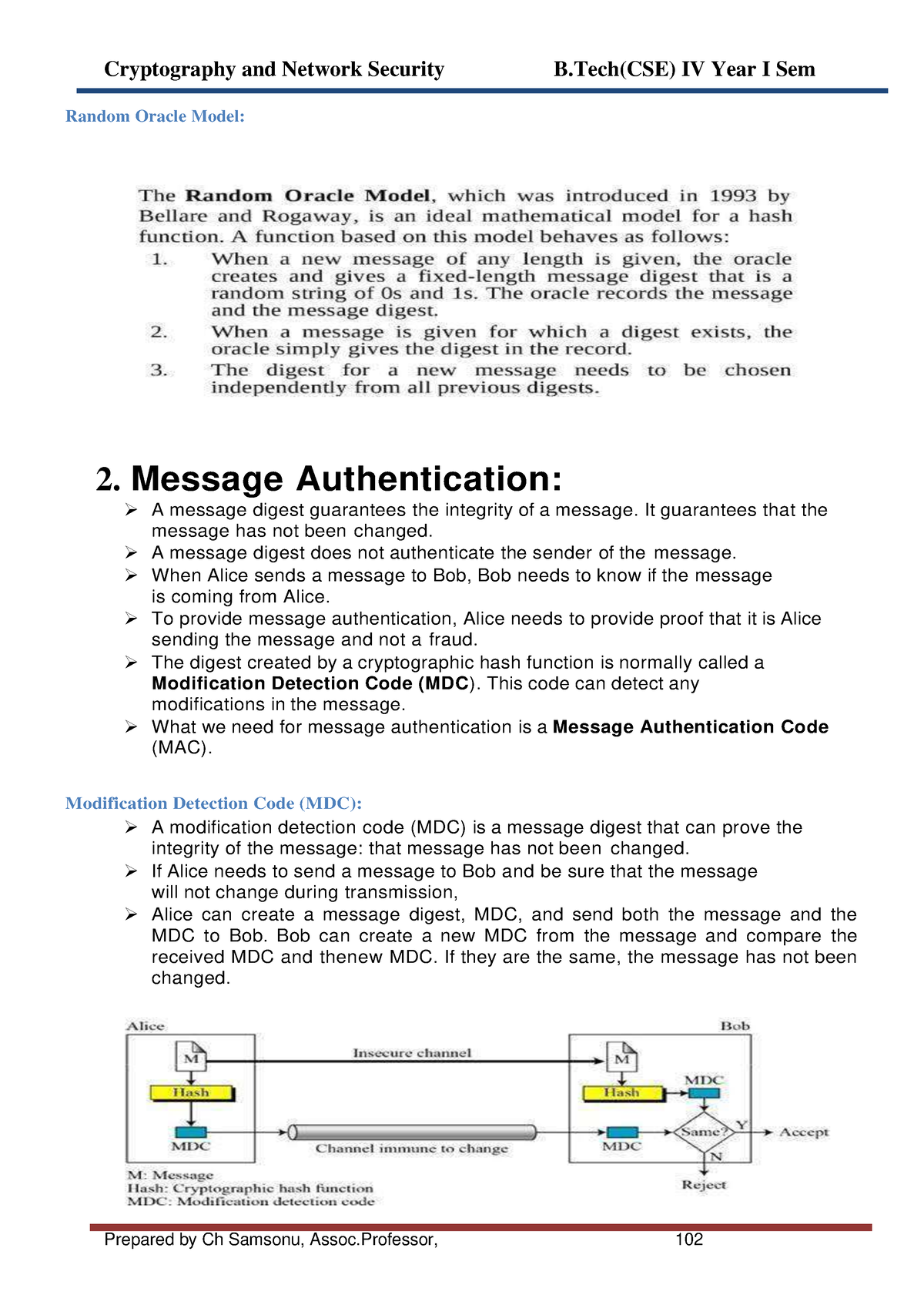
Pdf A Review On Security Enhancement In Wsn Using Neural Network Solutions manual for network security essentials: applications and standards, fifth edition. includes answers to review questions and homework problems. Task 3: a network — overview to understand network security, it is essential to comprehend what a network is, the components or assets that form it, and how these components work together. A tutorial and survey on network security technology. the book covers important network security tools and applications, including s mime, ip security, kerberos, ssl tls, and x509v3. Step by step video answers explanations by expert educators for all network security essentials: applications and standards, fourth edition 4th by william stallings only on numerade. Nonrepudiation: provides protection against denial by one of the entities involved in a communication of having participated in all or part of the communication. Chapter 3 public key cryptography and message authentication 75 3.1 approaches to message authentication 77 3.2 secure hash functions 81 3.3 message authentication codes 88 3.4 public key cryptography principles 94.
Comments are closed.