Lect5 Source Code Review Pdf

Source Code Report Detail Pdf String Computer Science Formalism Lect5 source code review free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. Lecture 5: syntax analysis review: syntax analysis specifying the form of a programming language.

051 Source Code Section 9 All Lectures Working With Other Data Types Pdf Contribute to w4111 w4111.github.io development by creating an account on github. All (13375) courses (3063) programs (38) learning materials (10274) course. Coditt5 is pretrained on large amounts of source code and natural language comments to perform edits, and we evaluate this model by fine tuning it on three distinct downstream tasks: comment updating, bug fixing and automated code review. Key commands include s find replace to substitute text, d to delete lines, and p to print lines. sed scripts contain a list of commands that are applied sequentially to each line of input. download as a pdf, pptx or view online for free.
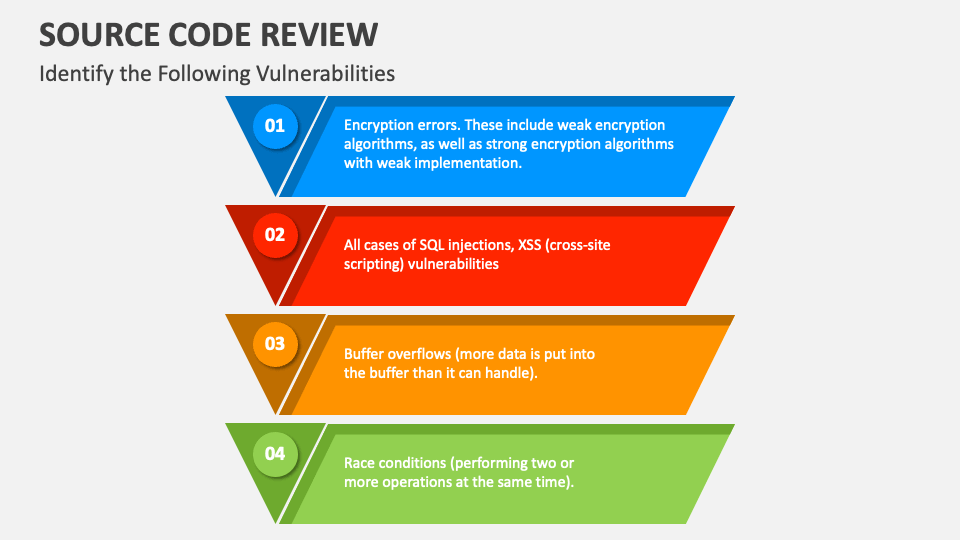
Source Code Review Powerpoint Presentation Slides Ppt Template Coditt5 is pretrained on large amounts of source code and natural language comments to perform edits, and we evaluate this model by fine tuning it on three distinct downstream tasks: comment updating, bug fixing and automated code review. Key commands include s find replace to substitute text, d to delete lines, and p to print lines. sed scripts contain a list of commands that are applied sequentially to each line of input. download as a pdf, pptx or view online for free. The practical secure code review training course is designed to teach developers and security professionals a repeatable process for reviewing source code for security flaws. How to ensure a healthy body of source code and preserve quality over time? guido van rossum: code is read much more than it is written! who writes style guides? what bugs can static analysis find? discuss: review this piece of code!. During the actual review, members of a review team review the application code for security problems and categorize the findings based on the weakness categories (e.g., authentication, authorization, etc.). each finding is assigned a risk rating of high, medium, low, or informational. A secure code review can be a manual or automated review, each with advantages and disadvantages. in a manual review, an analyst reviews the code line by line, looking for defects and.
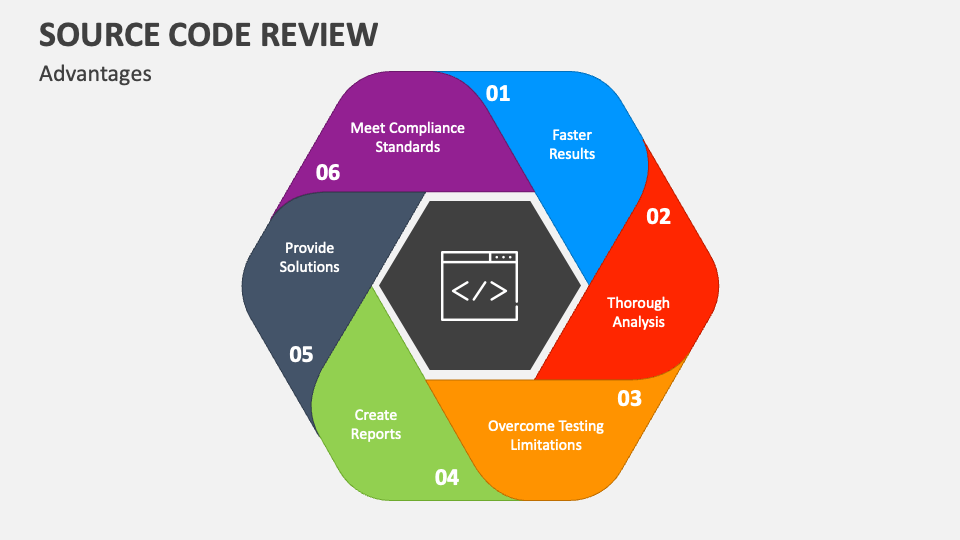
Source Code Review Powerpoint Presentation Slides Ppt Template The practical secure code review training course is designed to teach developers and security professionals a repeatable process for reviewing source code for security flaws. How to ensure a healthy body of source code and preserve quality over time? guido van rossum: code is read much more than it is written! who writes style guides? what bugs can static analysis find? discuss: review this piece of code!. During the actual review, members of a review team review the application code for security problems and categorize the findings based on the weakness categories (e.g., authentication, authorization, etc.). each finding is assigned a risk rating of high, medium, low, or informational. A secure code review can be a manual or automated review, each with advantages and disadvantages. in a manual review, an analyst reviews the code line by line, looking for defects and.
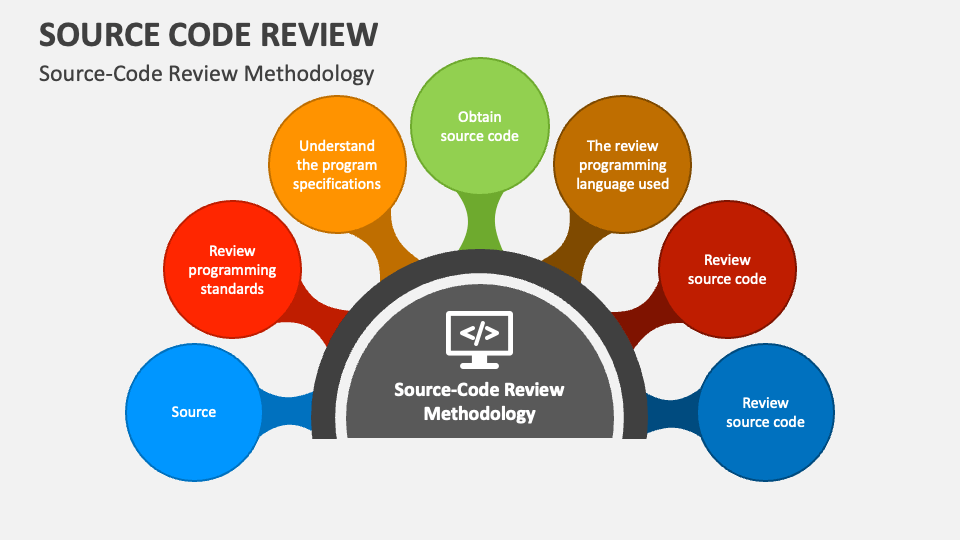
Source Code Review Powerpoint Presentation Slides Ppt Template During the actual review, members of a review team review the application code for security problems and categorize the findings based on the weakness categories (e.g., authentication, authorization, etc.). each finding is assigned a risk rating of high, medium, low, or informational. A secure code review can be a manual or automated review, each with advantages and disadvantages. in a manual review, an analyst reviews the code line by line, looking for defects and.
Comments are closed.