Lec 3 Isp And Security Pdf

Lec 3 Network Security Pdf Malware Computer Virus An overview of network security challenges like malware, denial of service attacks, packet sniffing, and ip spoofing. the importance of considering security in all layers of network design is also discussed. download as a pdf, pptx or view online for free. Lec3 free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses the structure of the internet as a complex 'network of networks' comprising various access isps, regional isps, and global transit isps.

1 Lec Pdf Information Security Policy So this module we will basically talk about isps, so isp stands for internet service provider, how they are typically structured in a very hierarchical model and also talk about that the different types of delays that a network packet can possibly incur when it goes from a source mission to a destination mission travelling across the different. 2. prinsip dasar jaringan (networking service) prinsip prinsip dasar dalam sistem networking service mencakup komponen komponen dan mekanisme yang mendasari konektivitas serta aliran informasi di dalam jaringan. berikut adalah beberapa prinsip dasar tersebut:. Q: given millions of access isps, how to connect together? option 1: connect each access isp to every other access isp? option 2: connect each access isp to one global transit isp? customer and provider isps have economic agreement. Privacy concerns: some network security measures, such as deep packet inspection and monitoring, may raise privacy concerns among users and stakeholders, requiring careful balancing of security needs with individual privacy rights.
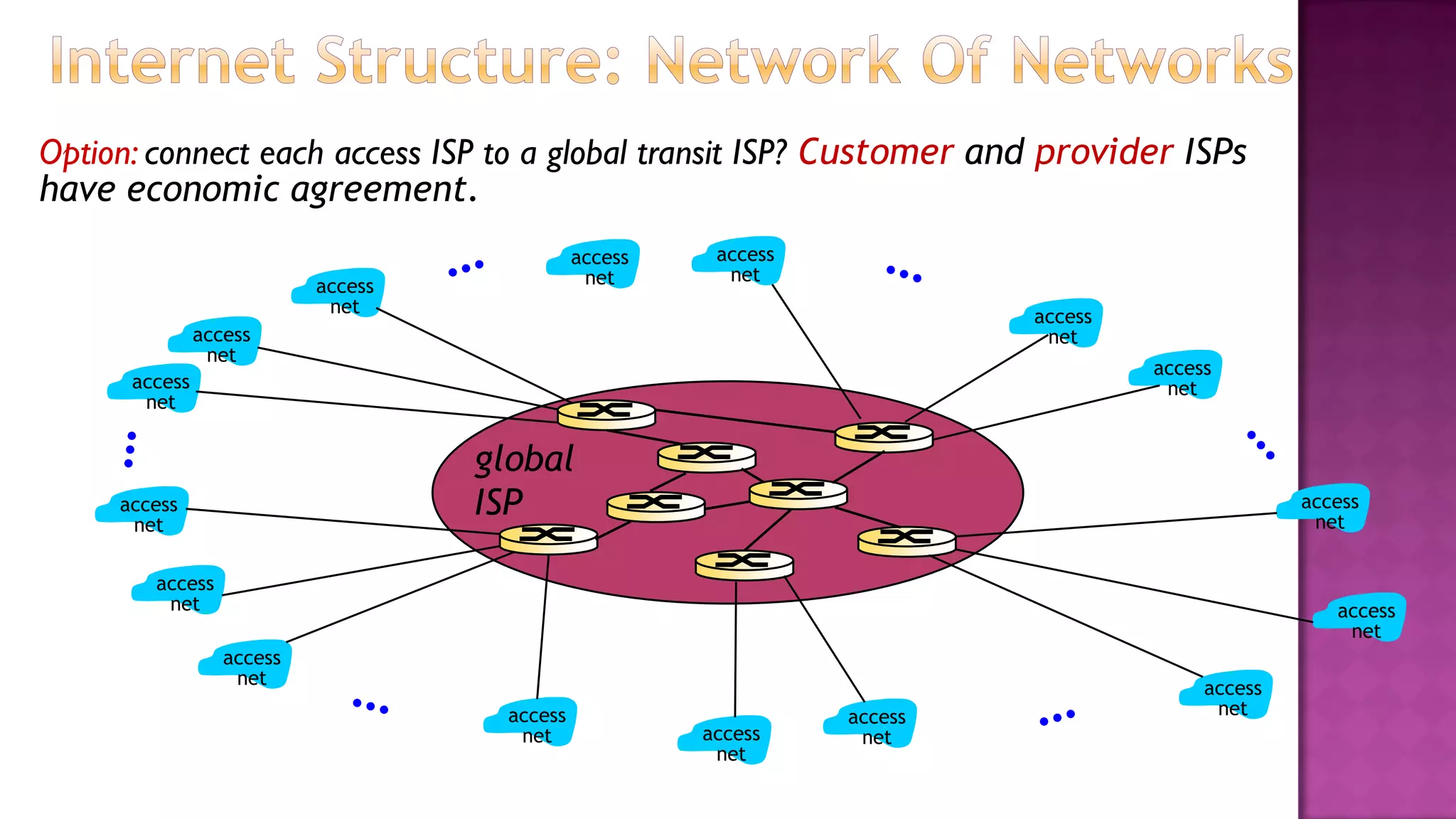
Lec 3 Isp And Security Pdf Q: given millions of access isps, how to connect together? option 1: connect each access isp to every other access isp? option 2: connect each access isp to one global transit isp? customer and provider isps have economic agreement. Privacy concerns: some network security measures, such as deep packet inspection and monitoring, may raise privacy concerns among users and stakeholders, requiring careful balancing of security needs with individual privacy rights. Attacks on computers and computer security: introduction, the need of security, security approaches, principles of security, types of security attacks, security services, security mechanisms, a model for network security. – private network that connects its data centers to internet – often bypasses tier 1, regional isps, may buy transit – by not paying provider isp, save money and better control qos for traffic. In this unit, we shall learn about how to build a secure network. we shall also learn about the various parameters which must be considered for network security. Wireless connectivity to servers and storage is becoming increasingly common these days. to provide security and asurance, wireless networks have adopted many security mechanisms from the wired world. wireless security course resourses slides lec 03.pdf at master · uit bmtt wireless security course.
Lec 3 Isp And Security Ppt Attacks on computers and computer security: introduction, the need of security, security approaches, principles of security, types of security attacks, security services, security mechanisms, a model for network security. – private network that connects its data centers to internet – often bypasses tier 1, regional isps, may buy transit – by not paying provider isp, save money and better control qos for traffic. In this unit, we shall learn about how to build a secure network. we shall also learn about the various parameters which must be considered for network security. Wireless connectivity to servers and storage is becoming increasingly common these days. to provide security and asurance, wireless networks have adopted many security mechanisms from the wired world. wireless security course resourses slides lec 03.pdf at master · uit bmtt wireless security course.

Unit 3 Network Security Pdf Public Key Cryptography Encryption In this unit, we shall learn about how to build a secure network. we shall also learn about the various parameters which must be considered for network security. Wireless connectivity to servers and storage is becoming increasingly common these days. to provide security and asurance, wireless networks have adopted many security mechanisms from the wired world. wireless security course resourses slides lec 03.pdf at master · uit bmtt wireless security course.
Comments are closed.