Learn About Arbitrary File Read
Cve 2024 23897 Jenkins Arbitrary File Read Vulnerability Know much about exploiting path traversal or arbitrary file read vulnerabilities? learn some practical attacks for unearthing high impact, lucrative vulnerabilities. This technique is relevant in cases where you control the file path of a php function that will access a file but you won’t see the content of the file (like a simple call to file()) but the content is not shown.
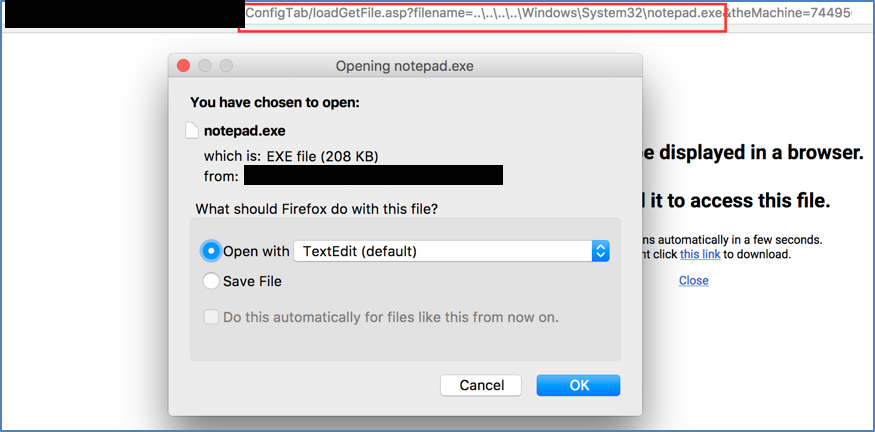
Arbitrary File Read In Kaseya Vsa This article covers cases of possible arbitrary file read on wordpress. this includes improper file fetch handling inside of the plugin theme which can be used to read arbitrary local files inside of the server. Path traversal is also known as directory traversal. these vulnerabilities enable an attacker to read arbitrary files on the server that is running an application. this might include: application code and data. credentials for back end systems. sensitive operating system files. Arbitrary file read is a vulnerability class that allows attackers to read files from the server's filesystem that they should not have access to. this can expose sensitive configuration files, source code, credentials, and private data. Curl’s file: protocol handler is enabled by default, allowing access to local files on the system. this behavior enables an attacker with the ability to run curl commands to read arbitrary files on the host by specifying file paths or using directory traversal techniques.
Learn About Arbitrary File Read Arbitrary file read is a vulnerability class that allows attackers to read files from the server's filesystem that they should not have access to. this can expose sensitive configuration files, source code, credentials, and private data. Curl’s file: protocol handler is enabled by default, allowing access to local files on the system. this behavior enables an attacker with the ability to run curl commands to read arbitrary files on the host by specifying file paths or using directory traversal techniques. Discover cve 2025 30208, a critical arbitrary file read vulnerability in the vite development server. learn how remote attackers exploit @fs url handling to access sensitive files. Arbitrary file read lets attackers access any server file, risking data leaks. learn how this vulnerability works and how to prevent it. File read exploitation guide: lfi, path traversal, sql injection techniques. pentesting strategies for unauthorized file access & escalation. Despite disabling the strings column, it’s still possible to retrieve arbitrary file data. in order for yara scanning to work at all, it must provide a true or false for each yara rule’s scan .
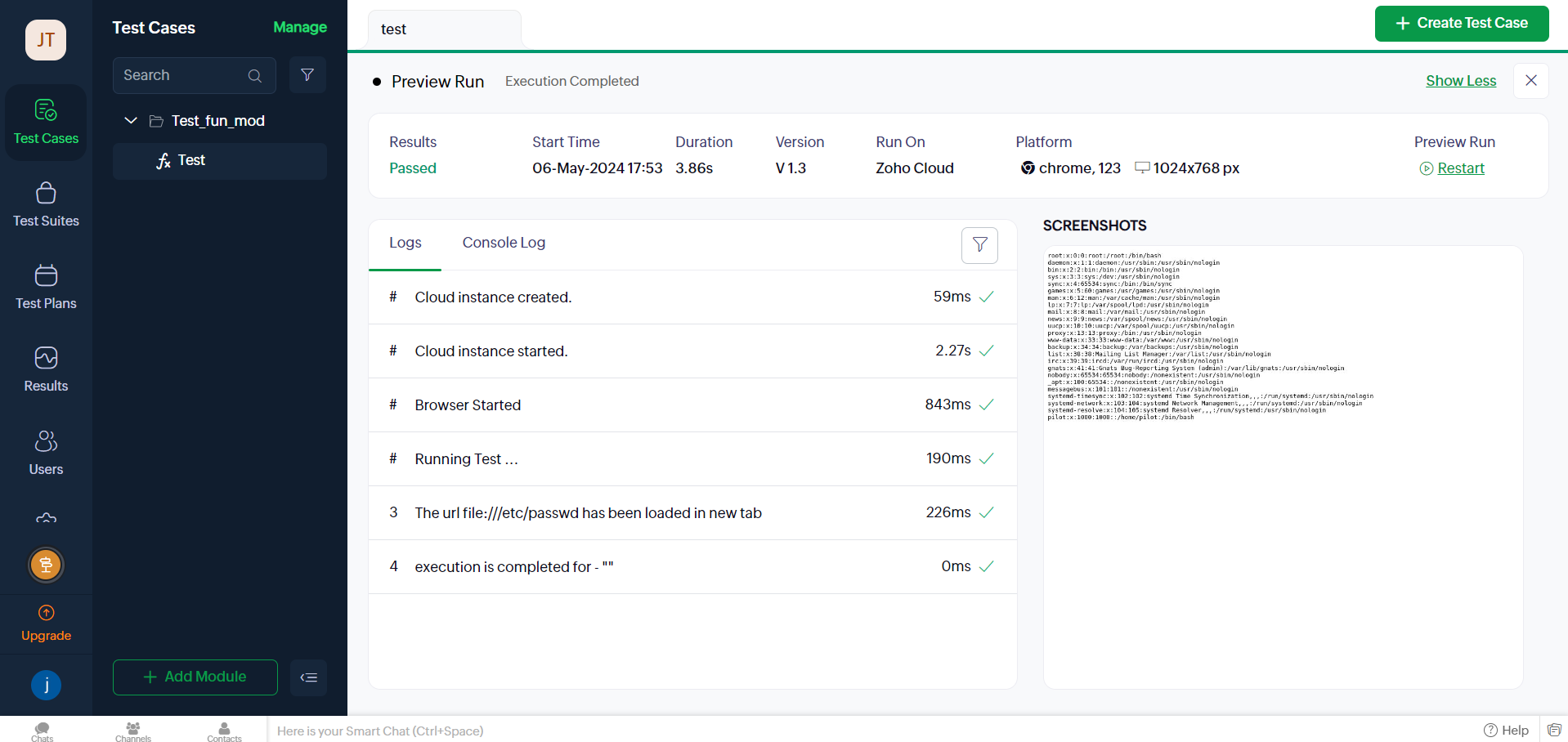
Zoho Qengine Arbitrary File Read Jayateertha G S Blog Discover cve 2025 30208, a critical arbitrary file read vulnerability in the vite development server. learn how remote attackers exploit @fs url handling to access sensitive files. Arbitrary file read lets attackers access any server file, risking data leaks. learn how this vulnerability works and how to prevent it. File read exploitation guide: lfi, path traversal, sql injection techniques. pentesting strategies for unauthorized file access & escalation. Despite disabling the strings column, it’s still possible to retrieve arbitrary file data. in order for yara scanning to work at all, it must provide a true or false for each yara rule’s scan .
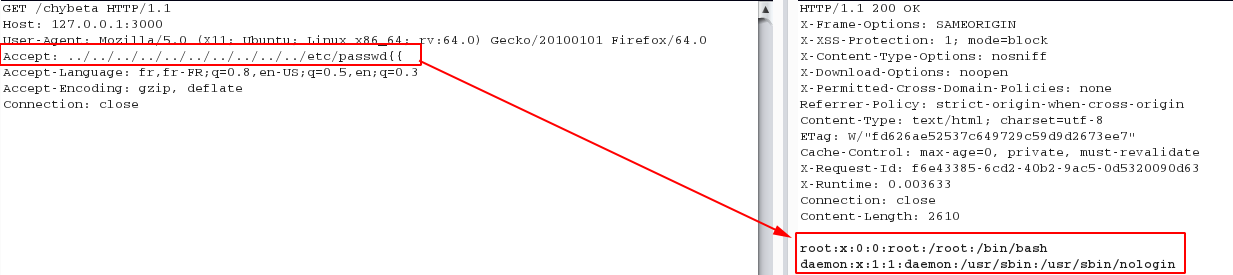
Arbitrary File Read Vulnerability In Hackerrank File read exploitation guide: lfi, path traversal, sql injection techniques. pentesting strategies for unauthorized file access & escalation. Despite disabling the strings column, it’s still possible to retrieve arbitrary file data. in order for yara scanning to work at all, it must provide a true or false for each yara rule’s scan .

Dejan Zelic On Linkedin Arbitrary File Read
Comments are closed.