Lab1 Walkthrough

Walkthrough Lab1 Explain How You Would Add Your Own Hello World Challange: memlabs lab1 challange description: my sister’s computer crashed. we were very fortunate to recover this memory dump. your job is get all her important files from the system. I decided to refresh my memory forensics knowledge by going through memlabs ctf styled challenges and this post is writeup for the first challenge named “beginner’s luck”. the following is the statement of the challenge that contains the clues that should be extracted to plan how to approach the challenge. my sister’s computer crashed.

Ece 3610 Lab 1 State Machine Design And Implementation Course Hero Use the tools and techniques described in the chapter to gain information about the files and answer the questions below. upload the files to virustotal and view the reports. does either file match any existing antivirus signatures?. In this blog posts series, i’ll be delving into the practical exercises provided in the renowned book “practical malware analysis,” offering insights, strategies, and hands on experiences to fortify my understanding of malware behavior and analysis techniques. Practical walkthrough of portswigger web security academy labs with step by step exploitation, real payloads, and easy to understand explanations for web security learners. nikhilkumar0102 portsw. [memlabs write up] memlabs lab 1 — beginner’s luck challenge description my sister’s computer crashed. we were very fortunate to recover this memory dump. your job is get all her important ….

Cs669 Lab1 Walkthrough Slides Pptx Lab 1 Walkthrough Copyright 2010 Practical walkthrough of portswigger web security academy labs with step by step exploitation, real payloads, and easy to understand explanations for web security learners. nikhilkumar0102 portsw. [memlabs write up] memlabs lab 1 — beginner’s luck challenge description my sister’s computer crashed. we were very fortunate to recover this memory dump. your job is get all her important …. Lab01 01.dll imports show it uses ws2 32.dll for creating sockets means we need to investigate the traffic, it also uses createprocess from kernel32.dll which means investigate new process spawned. q5 do any imports hint at what this malware does? if so, which imports are they?. Our first step will be checking the image info to know which profile will be used in the analysis. as we see it “win7sp1x64” so let’s start check the process and see if there are anything suspicious. so we found cmd.exe that was running so we scanned it. This is a walkthrough of the lab 1 1 from the book practical malware analysis: basic static malware analysis techniques are applied to the samples lab01 01.exe and lab01 01.dll. In this series i’ll be sharing my write ups for the labs included in this book. there’s a total of 18 chapters that contain lab exercises. let’s kick it off with the labs included in chapter 1! this lab uses the files lab01 01.exe and lab01 01.dll.

Memlabs Lab1 Walkthrough Write Up By 0d 3mr Medium Lab01 01.dll imports show it uses ws2 32.dll for creating sockets means we need to investigate the traffic, it also uses createprocess from kernel32.dll which means investigate new process spawned. q5 do any imports hint at what this malware does? if so, which imports are they?. Our first step will be checking the image info to know which profile will be used in the analysis. as we see it “win7sp1x64” so let’s start check the process and see if there are anything suspicious. so we found cmd.exe that was running so we scanned it. This is a walkthrough of the lab 1 1 from the book practical malware analysis: basic static malware analysis techniques are applied to the samples lab01 01.exe and lab01 01.dll. In this series i’ll be sharing my write ups for the labs included in this book. there’s a total of 18 chapters that contain lab exercises. let’s kick it off with the labs included in chapter 1! this lab uses the files lab01 01.exe and lab01 01.dll.
Nintendohunt Lab Cyberdefenders Walkthrough Write Up By 0d 3mr Sep This is a walkthrough of the lab 1 1 from the book practical malware analysis: basic static malware analysis techniques are applied to the samples lab01 01.exe and lab01 01.dll. In this series i’ll be sharing my write ups for the labs included in this book. there’s a total of 18 chapters that contain lab exercises. let’s kick it off with the labs included in chapter 1! this lab uses the files lab01 01.exe and lab01 01.dll.
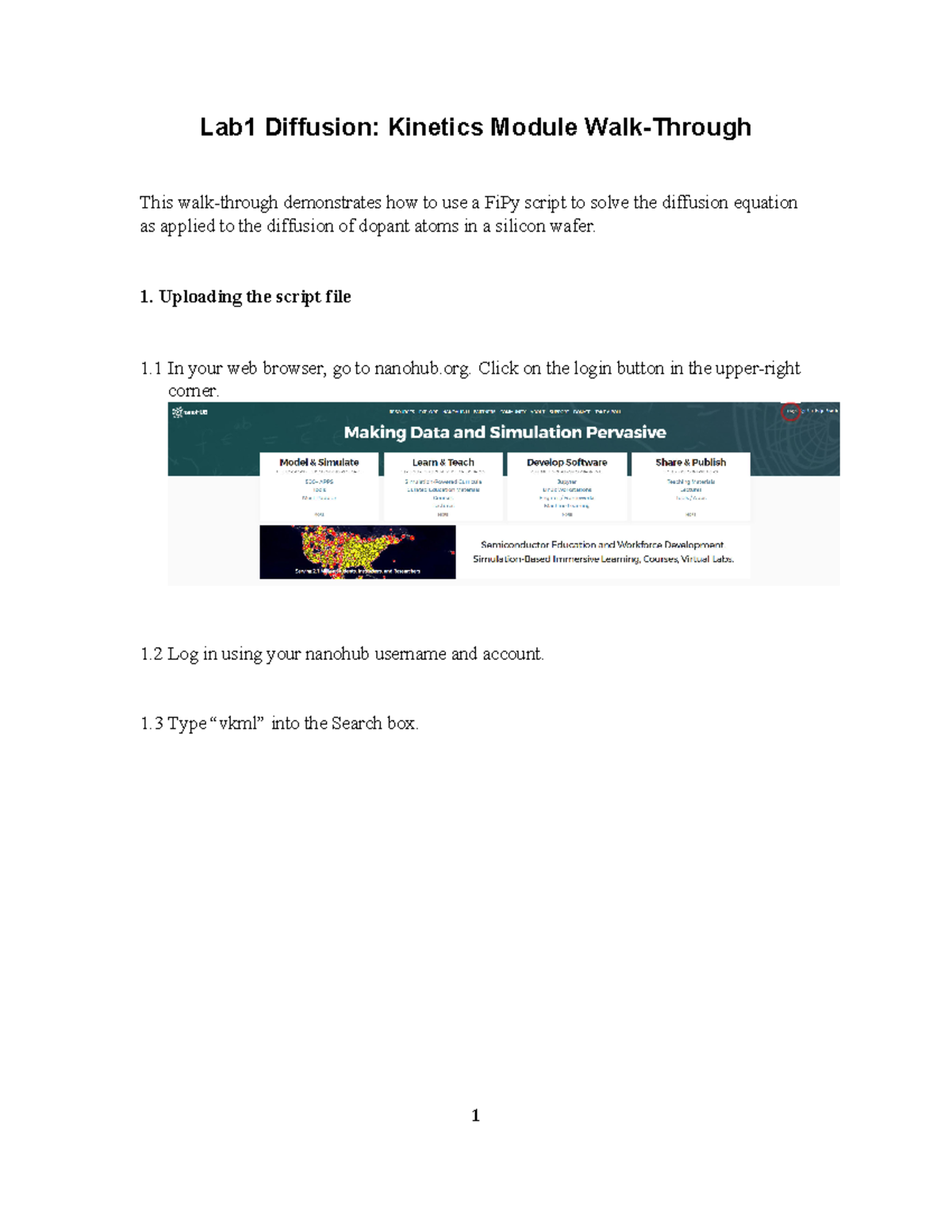
Lab1 Diffusion Walkthrough Lab1 Diffusion Kinetics Module Walk
Comments are closed.