Lab05 Reverse_engineering Lab Cybersecurity Reverseengineering Coding
Github Nappolitane Reverseengineering Lab This Is A Repository For Lab05 — dll key xor decoding 🔵 same binary as lab04. but this time there's a second stage. after clearing stage 1, the binary loads payload.dll and asks for another key. Contribute to leambeam cybersecurity development by creating an account on github.

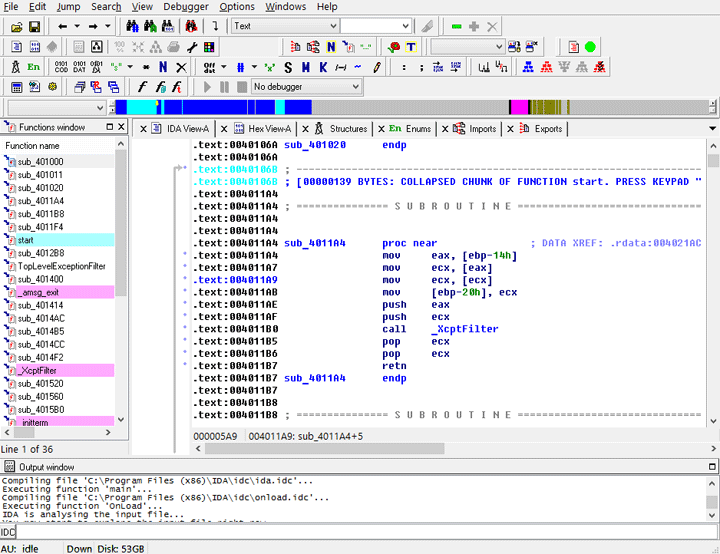
Reverse Engineering Malware Part 1 Getting Started This details reverse engineering activities and answers for labs contained in the book ‘practical malware analysis’ by michael sikorski and andrew honig, which is published by no starch press. What is reverse engineering? reverse engineering is a popular hacking approach that extracts the knowledge and design of a system and reproduces its behavior based on the extracted. I approached this lab as an opportunity to sharpen my reverse‑engineering skills using ida pro. in practical malware analysis lab 5, i was given a suspicious dll lab05–01.dll, and asked. The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware.
Github A0m0rajab Reverse Engineering Lab I approached this lab as an opportunity to sharpen my reverse‑engineering skills using ida pro. in practical malware analysis lab 5, i was given a suspicious dll lab05–01.dll, and asked. The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Lab 5 1 analyze the malware found in the file lab05 01.dll using only ida pro. the goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Real world reverse engineering applied to closed source user and kernel targets, covering beginner and advanced topics including custom deobfuscation routine development in rust. Using real world vulnerability classes, students will examine how attackers identify flaws in modern software and exploit these flaws bypassing state of the art protection mechanisms found in modern operating systems.

Lab1 Reverse Engineering Assignment Pdf Lab 1 Reverse Engineering The goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Lab 5 1 analyze the malware found in the file lab05 01.dll using only ida pro. the goal of this lab is to give you hands on experience with ida pro. if you’ve already worked with ida pro, you may choose to ignore these questions and focus on reverse engineering the malware. Real world reverse engineering applied to closed source user and kernel targets, covering beginner and advanced topics including custom deobfuscation routine development in rust. Using real world vulnerability classes, students will examine how attackers identify flaws in modern software and exploit these flaws bypassing state of the art protection mechanisms found in modern operating systems.
Reverse Engineering Untuk Mengatasi Cyber Attack Coding Studio Real world reverse engineering applied to closed source user and kernel targets, covering beginner and advanced topics including custom deobfuscation routine development in rust. Using real world vulnerability classes, students will examine how attackers identify flaws in modern software and exploit these flaws bypassing state of the art protection mechanisms found in modern operating systems.
Comments are closed.