Lab Exploiting An Api Endpoint Using Documentation Web Security Academy

Lab Exploiting An Api Endpoint Using Documentation Web Security Academy Required knowledge to solve this lab, you'll need to know: what api documentation is. how api documentation may be useful to an attacker. how to discover api documentation. these points are covered in our api testing academy topic. A pi testing — lab: exploiting an api endpoint using documentation in this portswigger web security academy lab, the goal is simple:.

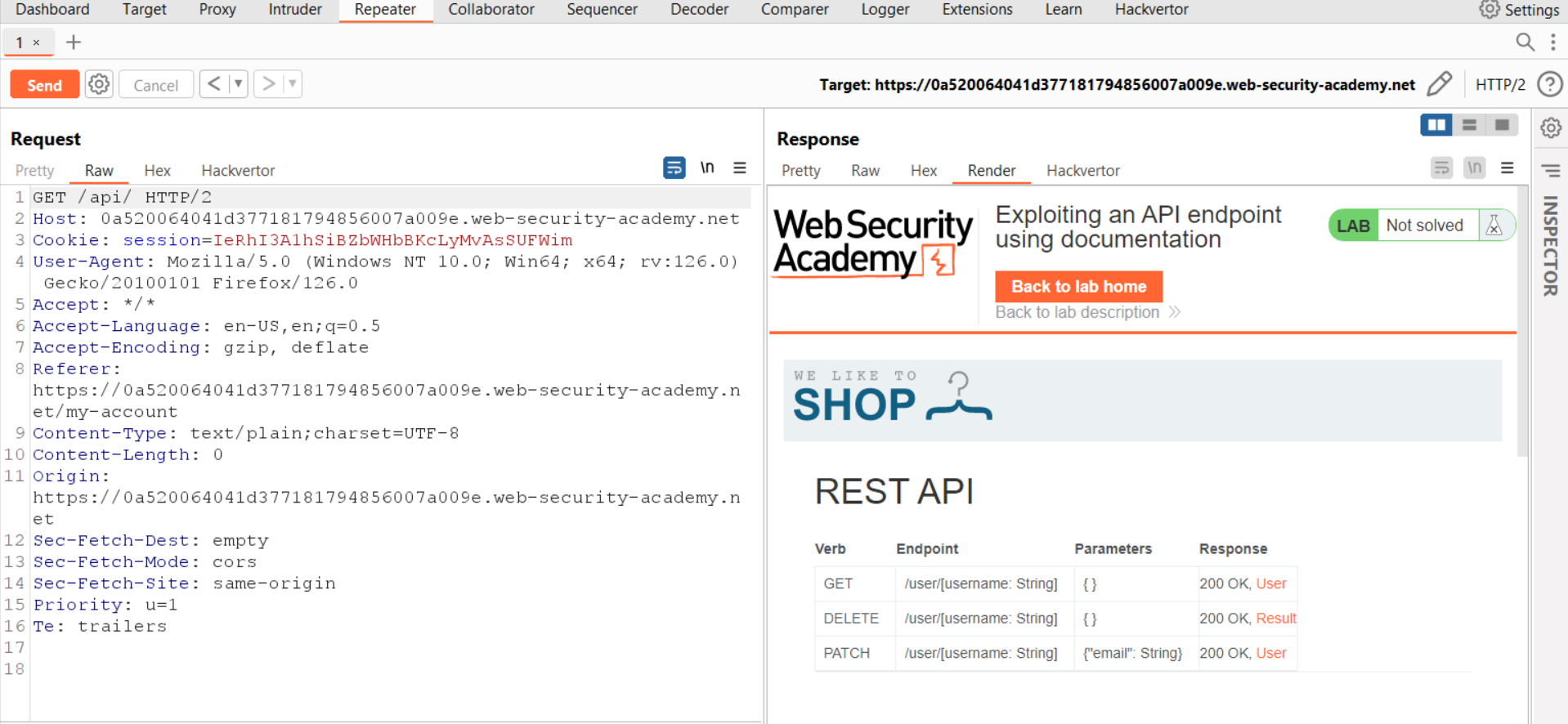
Lab Exploiting An Api Endpoint Using Documentation Web Security Academy Hello hackers, in this video of exploiting an api endpoint using documentation you will see how to exploit, discover and find hidden endpoints and senstive information from burp suite. This interface is intended for developers, but when exposed to attackers, it reveals sensitive administrative endpoints (like delete api user {username}) that are otherwise hidden from the standard web ui. 🧠 theory apis often ship with documentation intended for developers — swagger openapi specs, postman collections, or raw json yaml files. when this documentation is left publicly accessible, an attacker can use it to understand the full api surface: all endpoints, http methods, parameters, and authentication requirements. After getting a basic understanding of apis let’s now try to find these api endpoints and exploit them using their documentation. we will be using portswigger’s lab to see the same in action.

Lab Exploiting An Api Endpoint Using Documentation Infosec Writeups 🧠 theory apis often ship with documentation intended for developers — swagger openapi specs, postman collections, or raw json yaml files. when this documentation is left publicly accessible, an attacker can use it to understand the full api surface: all endpoints, http methods, parameters, and authentication requirements. After getting a basic understanding of apis let’s now try to find these api endpoints and exploit them using their documentation. we will be using portswigger’s lab to see the same in action. Public facing api documentation is often overlooked by devs and testers — but not by attackers. this lab proves how “helpful” docs can turn into a red carpet for exploitation. This article shows readers through practical labs which explore how attacks occur while demonstrating documentation based api endpoint exploitation together with mass assignment vulnerability discovery methods. By thoroughly analyzing api documentation and identifying potential vulnerabilities, i was able to understand the practical aspects of exploiting api endpoints and learn how to better. Exploiting server side parameter pollution in a rest url(利用rest url中的服务器端参数污染) lab: exploiting server side parameter pollution in a rest url | web security academy (portswigger ).
Exploiting An Api Endpoint Using Documentation Cyberiumx Public facing api documentation is often overlooked by devs and testers — but not by attackers. this lab proves how “helpful” docs can turn into a red carpet for exploitation. This article shows readers through practical labs which explore how attacks occur while demonstrating documentation based api endpoint exploitation together with mass assignment vulnerability discovery methods. By thoroughly analyzing api documentation and identifying potential vulnerabilities, i was able to understand the practical aspects of exploiting api endpoints and learn how to better. Exploiting server side parameter pollution in a rest url(利用rest url中的服务器端参数污染) lab: exploiting server side parameter pollution in a rest url | web security academy (portswigger ).
Comments are closed.