Lab 3 Network Sniffing

Network Sniffing Pdf Computer Network Ip Address Specifically, you will first implement a web server by using application level socket. next, you will experiment with icmp tunneling, packet sniffing, and packet spoofing, by using raw sockets. you should download this source code to start with this lab. Explore network operations and encapsulation in this lab manual, featuring hands on exercises with wireshark for packet analysis.

3 2 11 Lab Network Sniffing With Wireshark Pdf Domain Name System Network sniffing & arp spoofing lab this project demonstrates packet sniffing and arp cache poisoning attacks in a controlled environment using seed labs. This document describes a cybersecurity lab exercise on network packet sniffing and analysis using wireshark. the exercise involves analyzing sample packet capture files containing telnet, http, and ftp traffic to identify usernames, passwords, files transferred and their contents. 3.2.10 lab network sniffing with wireshark muhammad abiyyu utomo 4 subscribers subscribe. Below is my code for the next task, i created three different functions for each sub task icmp, tcp, and subnet sniffing. while running the code pass the option as a command line argument to.
Network Sniffing Ppt 3.2.10 lab network sniffing with wireshark muhammad abiyyu utomo 4 subscribers subscribe. Below is my code for the next task, i created three different functions for each sub task icmp, tcp, and subnet sniffing. while running the code pass the option as a command line argument to. In this lab, you had the opportunity to become familiar with capturing packets in both the tcpdump utility and the wireshark application. what are the benefits of using packet capture utilities when performing passive reconnaissance on a potential target?. Lab report on packet sniffing and spoofing using scapy. covers icmp, tcp, subnet sniffing, spoofing, and traceroute analysis. network security. In this hands on lab, you will learn the basics of network sniffing, including passive and active sniffing techniques. you will practice using wireshark to sniff network traffic, and retrieve and apply actionable information from a target network. A mac duplicating or spoofing attack involves sniffing a network for the mac addresses of legitimate clients connected to the network. in this attack, the attacker first retrieves the mac addresses of clients who are actively associated with the switch port.

Exploring Network Sniffing Techniques For Cyber Security Course Hero In this lab, you had the opportunity to become familiar with capturing packets in both the tcpdump utility and the wireshark application. what are the benefits of using packet capture utilities when performing passive reconnaissance on a potential target?. Lab report on packet sniffing and spoofing using scapy. covers icmp, tcp, subnet sniffing, spoofing, and traceroute analysis. network security. In this hands on lab, you will learn the basics of network sniffing, including passive and active sniffing techniques. you will practice using wireshark to sniff network traffic, and retrieve and apply actionable information from a target network. A mac duplicating or spoofing attack involves sniffing a network for the mac addresses of legitimate clients connected to the network. in this attack, the attacker first retrieves the mac addresses of clients who are actively associated with the switch port.
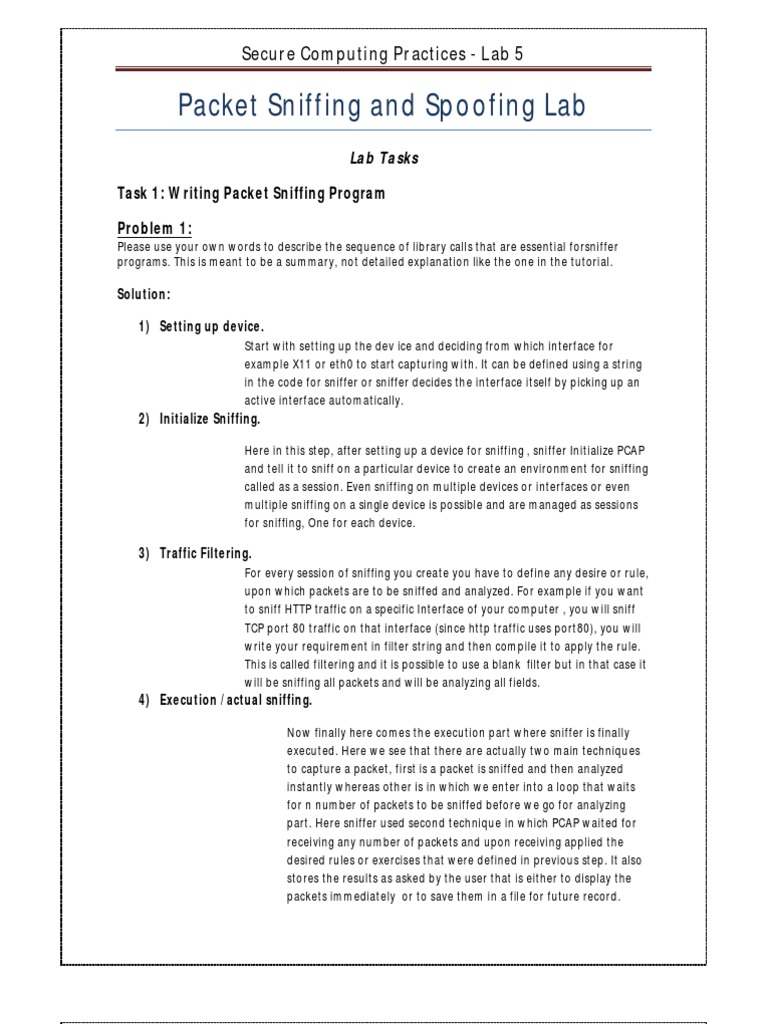
Packet Sniffing And Spoofing Lab Final Pdf Network Socket In this hands on lab, you will learn the basics of network sniffing, including passive and active sniffing techniques. you will practice using wireshark to sniff network traffic, and retrieve and apply actionable information from a target network. A mac duplicating or spoofing attack involves sniffing a network for the mac addresses of legitimate clients connected to the network. in this attack, the attacker first retrieves the mac addresses of clients who are actively associated with the switch port.

Understanding Network Sniffing And How To Protect Your Data
Comments are closed.