Lab 3 Finding And Exploiting An Unused Api Endpoint Api Testing
Lab 3 Finding And Exploiting An Unused Api Endpoint Api Testing Required knowledge to solve this lab, you'll need to know: how to use error messages to construct a valid request. how http methods are used by restful apis. how changing the http method can reveal additional functionality. these points are covered in our api testing academy topic. H i my dear readers, api based applications often have endpoints that are kept for development testing use and then become “unused” or “forgotten”. these can lead to data leakage or late night access breaking if there is no proper access control with the main app.

Finding And Exploiting An Unused Api Endpoint Christian V In this video you will get the detailed solution of lab of api testing from portswigger. more. Api testing labs exploiting a mass assignment vulnerability.md exploiting an api endpoint using documentation.md exploiting server side parameter pollution in a rest url.md exploiting server side parameter pollution in a query string.md finding and exploiting an unused api endpoint.md. These labs covered api documentation exploitation, server side parameter pollution in query strings and rest urls, finding unused api endpoints, and exploiting mass assignment vulnerabilities. This lab from portswigger’s web security academy teaches us how to identify and exploit an unused but accessible api endpoint using http method tampering and basic json manipulation.

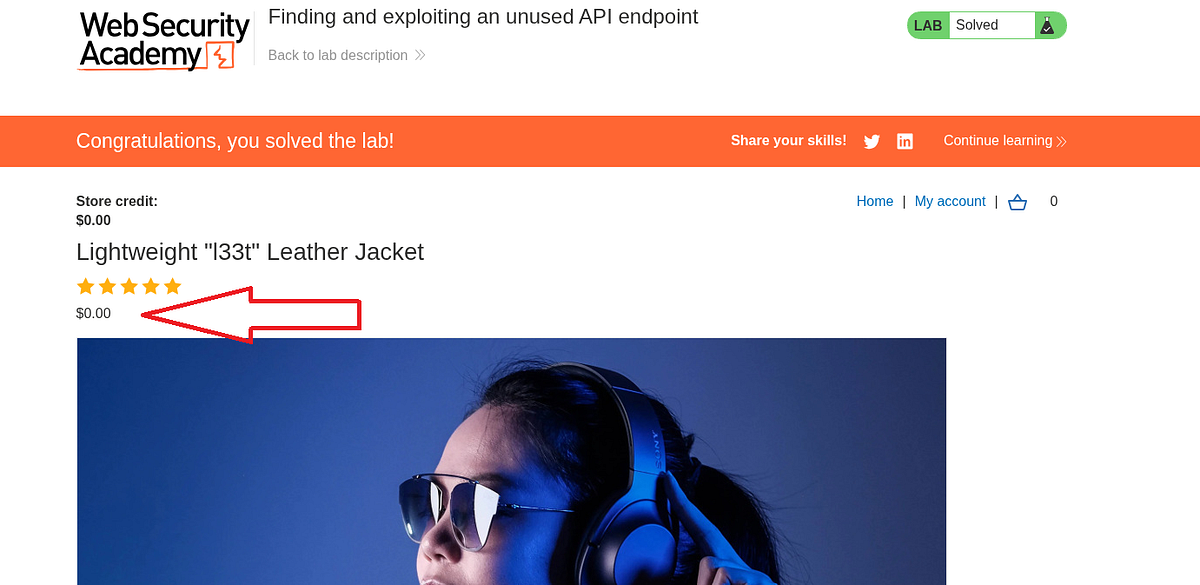
Finding And Exploiting An Unused Api Endpoint Christian V These labs covered api documentation exploitation, server side parameter pollution in query strings and rest urls, finding unused api endpoints, and exploiting mass assignment vulnerabilities. This lab from portswigger’s web security academy teaches us how to identify and exploit an unused but accessible api endpoint using http method tampering and basic json manipulation. Let’s start by reading the lab description where we have to identify and exploit a hidden api endpoint to buy a product without spending any money. for this, we are provided with a credential pair. this lab can be easily solved using the burp suite community edition. Api penetration testing focuses on identifying vulnerabilities in these endpoints that can be exploited to gain unauthorized access, disrupt services, or exfiltrate sensitive data. one. Apis, or application programming interfaces, are the invisible backbone of modern software development. they enable applications and systems to communicate and share data efficiently. Right click the api request and select send to repeater. in the repeater tab, change the http method for the api request from get to options, then send the request.

Finding And Exploiting An Unused Api Endpoint Christian V Let’s start by reading the lab description where we have to identify and exploit a hidden api endpoint to buy a product without spending any money. for this, we are provided with a credential pair. this lab can be easily solved using the burp suite community edition. Api penetration testing focuses on identifying vulnerabilities in these endpoints that can be exploited to gain unauthorized access, disrupt services, or exfiltrate sensitive data. one. Apis, or application programming interfaces, are the invisible backbone of modern software development. they enable applications and systems to communicate and share data efficiently. Right click the api request and select send to repeater. in the repeater tab, change the http method for the api request from get to options, then send the request.

Christian V Finding And Exploiting An Unused Api Endpoint Apis, or application programming interfaces, are the invisible backbone of modern software development. they enable applications and systems to communicate and share data efficiently. Right click the api request and select send to repeater. in the repeater tab, change the http method for the api request from get to options, then send the request.
Comments are closed.